Bad ad fad leads to IcedID, Gozi infections

Credit to Author: Matt Wixey| Date: Thu, 20 Jul 2023 10:00:07 +0000
Malvertising campaigns using paid ads result in infostealer and backdoor attacks
Read more
Credit to Author: Matt Wixey| Date: Thu, 20 Jul 2023 10:00:07 +0000
Malvertising campaigns using paid ads result in infostealer and backdoor attacks
Read moreCredit to Author: Jovi Umawing| Date: Wed, 27 Apr 2022 10:15:34 +0000
Emotet is back with a new spam campaign. And it’s now spreading itself as a shortcut link file pretending to be Word document.
The post Emotet fixes bug in code, resumes spam campaign appeared first on Malwarebytes Labs.
Read more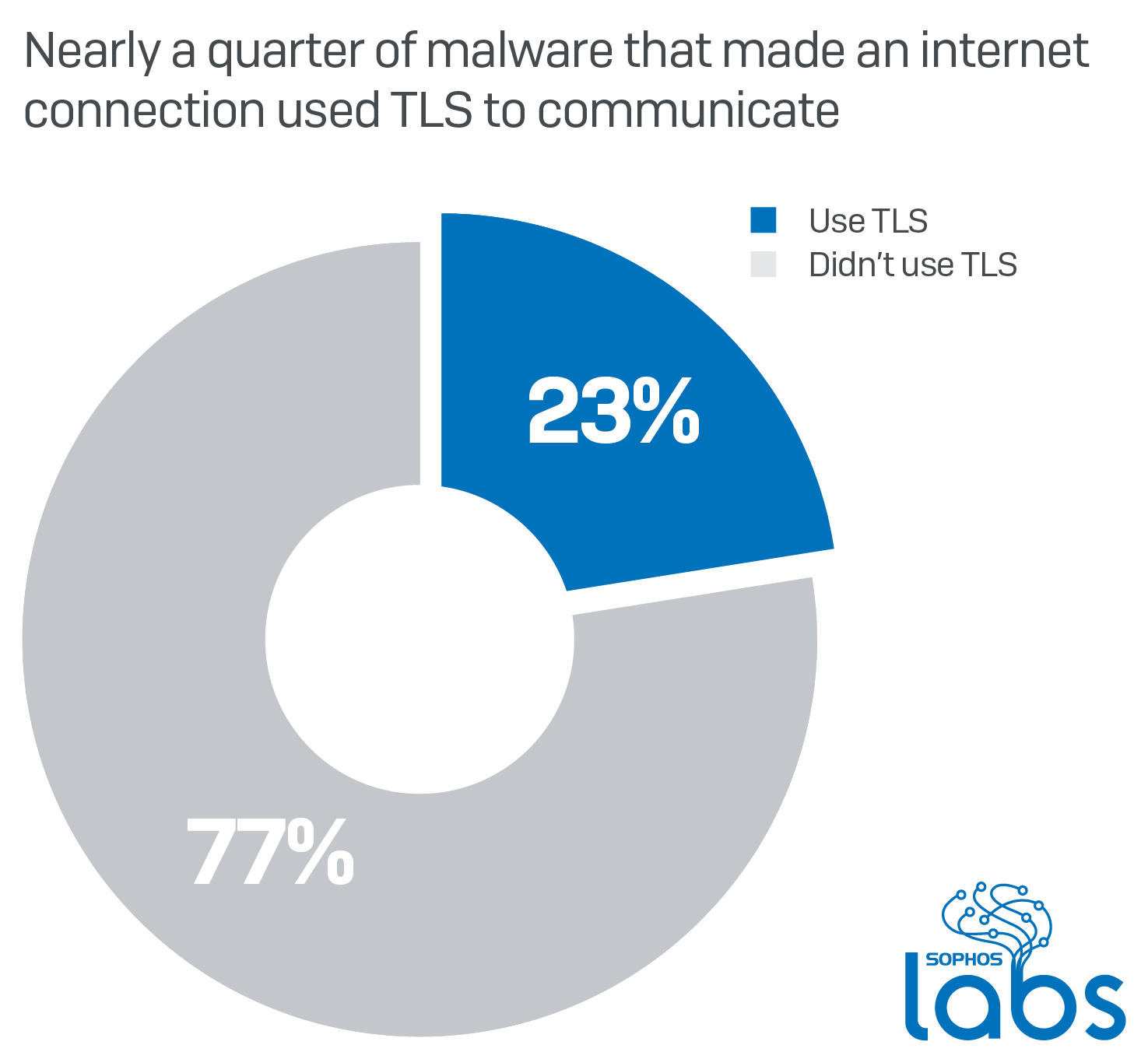
Credit to Author: Luca Nagy| Date: Tue, 18 Feb 2020 13:30:07 +0000
Encryption is one of the strongest weapons malware authors can leverage: They can use it to obfuscate their code, to prevent users (in the case of ransomware) from being able to access their files, and for securing their malicious network communication. As websites and apps more widely adopt TLS (Transport Layer Security) and communicate over […]<img src=”http://feeds.feedburner.com/~r/sophos/dgdY/~4/XXvUtjG7XVU” height=”1″ width=”1″ alt=””/>
Read moreCredit to Author: Bajrang Mane| Date: Wed, 29 Nov 2017 13:23:03 +0000
IcedID is a new player in the banking Trojan family. It has a modular architecture and capable of stealing banking credentials of the user by performing a man-in-the-middle attack (MITM). IcedID sets up a local proxy and redirects all Internet traffic through it. Additionally, it can download and execute components…
Read moreCredit to Author: Bajrang Mane| Date: Wed, 29 Nov 2017 13:23:03 +0000
IcedID is a new player in the banking Trojan family. It has a modular architecture and capable of stealing banking credentials of the user by performing a man-in-the-middle attack (MITM). IcedID sets up a local proxy and redirects all Internet traffic through it. Additionally, it can download and execute components…
Read more