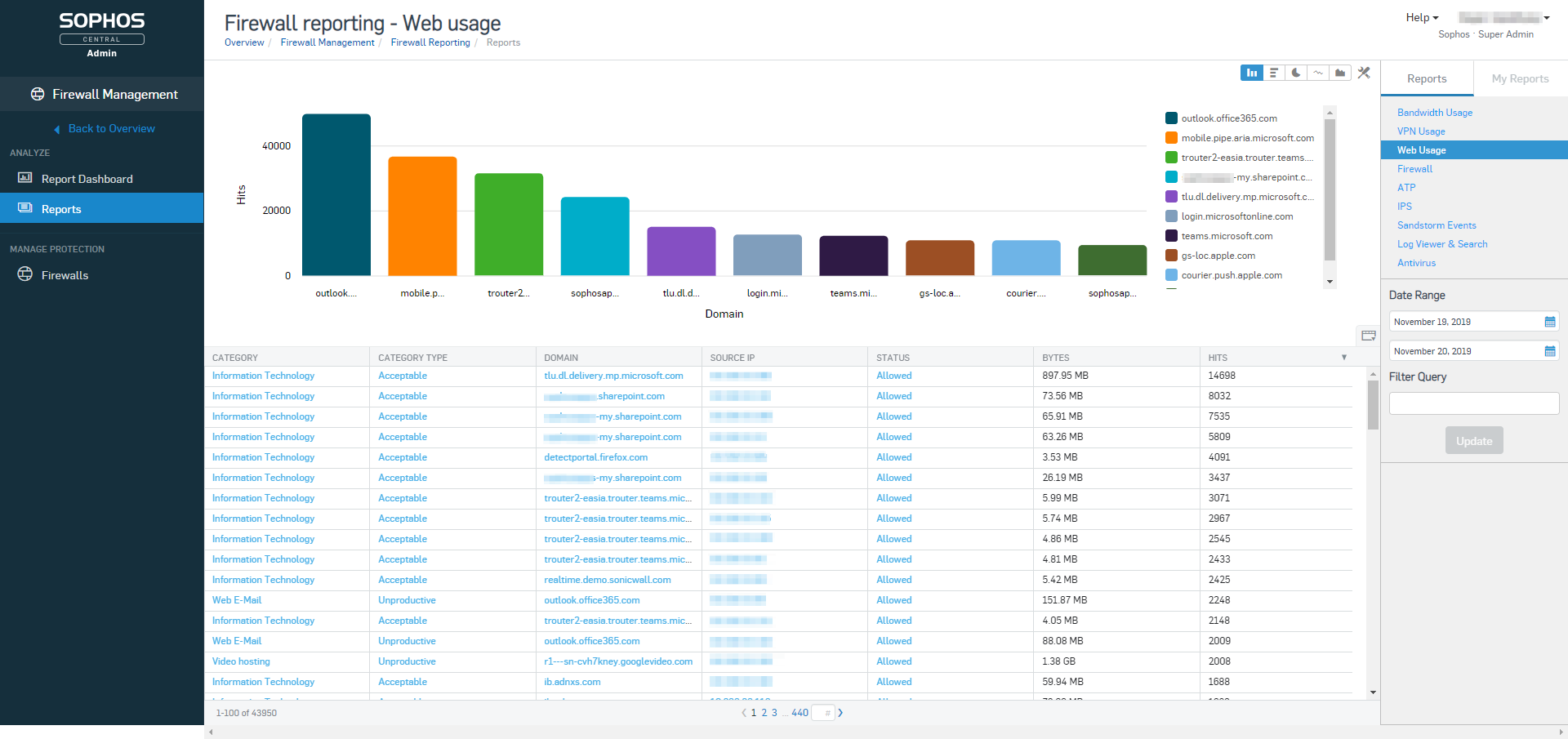
Introducing Central Firewall Reporting with XG Firewall v18
Credit to Author: scottgrebesophos| Date: Fri, 28 Feb 2020 17:45:15 +0000
New cloud-based reporting tool provides the flexibility to create custom historical reports on network activity for free.<img src=”http://feeds.feedburner.com/~r/sophos/dgdY/~4/eoQXzp5fOFk” height=”1″ width=”1″ alt=””/>
Read More