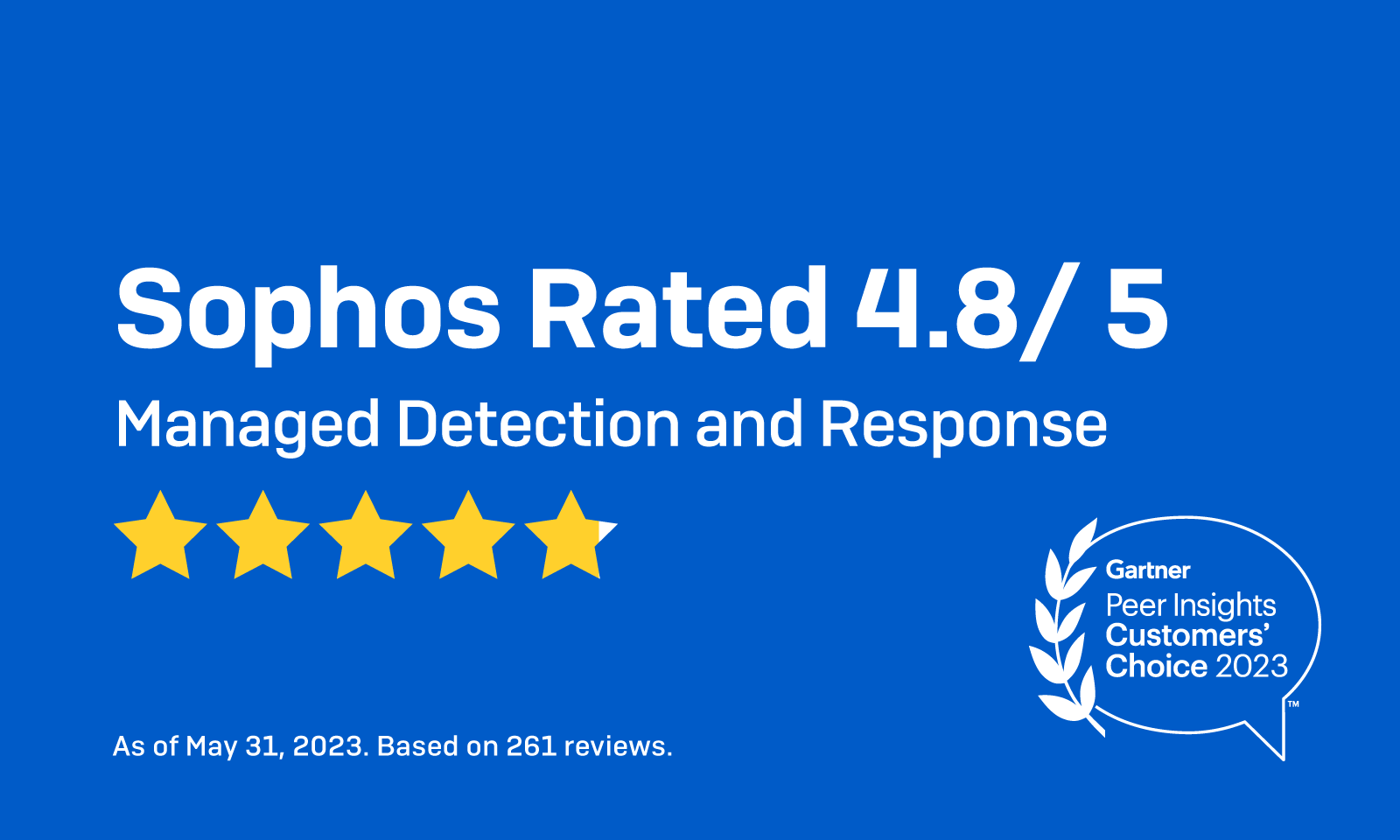
Sophos named a Gartner® Peer Insights™ Customers’ Choice for Managed Detection and Response (MDR) Services for the 2nd time

Credit to Author: rajansanhotra| Date: Tue, 03 Dec 2024 15:53:39 +0000
Sophos is the only vendor named a Customers’ Choice across Endpoint Protection Platforms, Network Firewalls, and Managed Detection and Response
Read More