BlackCat ransomware attacks not merely a byproduct of bad luck

Credit to Author: Andrew Brandt| Date: Thu, 14 Jul 2022 11:05:03 +0000
Older hardware and outdated operating systems contribute to attacks
Read MoreRSS Reader for Computer Security Articles

Credit to Author: Andrew Brandt| Date: Thu, 14 Jul 2022 11:05:03 +0000
Older hardware and outdated operating systems contribute to attacks
Read More
Credit to Author: Angela Gunn| Date: Thu, 14 Jul 2022 08:01:51 +0000
Ngrok is a legitimate remote-access tool. It is regularly abused by attackers, who use its capabilities and reputation to maneuver while bypassing network protections. This incident guide shows Security Operations Centers (SOCs) and response teams how to detect and respond to the suspicious presence or use of ngrok on the network.
Read More
Credit to Author: Angela Gunn| Date: Wed, 13 Jul 2022 03:20:43 +0000
Windows-facing issues make up the bulk of the 85 CVEs addressed, with one vulnerability under active exploit in the wild
Read More
Credit to Author: Andrew Brandt| Date: Thu, 16 Jun 2022 11:00:03 +0000
Automated attacks are now widely exploiting the Atlassian vulnerability
Read More
Credit to Author: Andrew Brandt| Date: Wed, 15 Jun 2022 21:16:52 +0000
Two groups with common task targeted network security devices in two-stage attacks, dropping remote access tools.
Read More
Credit to Author: Matt Wixey| Date: Wed, 15 Jun 2022 11:00:05 +0000
Attacker targets bugs in a popular web application graphical interface development tool
Read More
Credit to Author: Angela Gunn| Date: Tue, 14 Jun 2022 18:24:12 +0000
The second-lightest set of updates so far in 2022 goes heavy on RCEs, brings along four Intel patches for company
Read More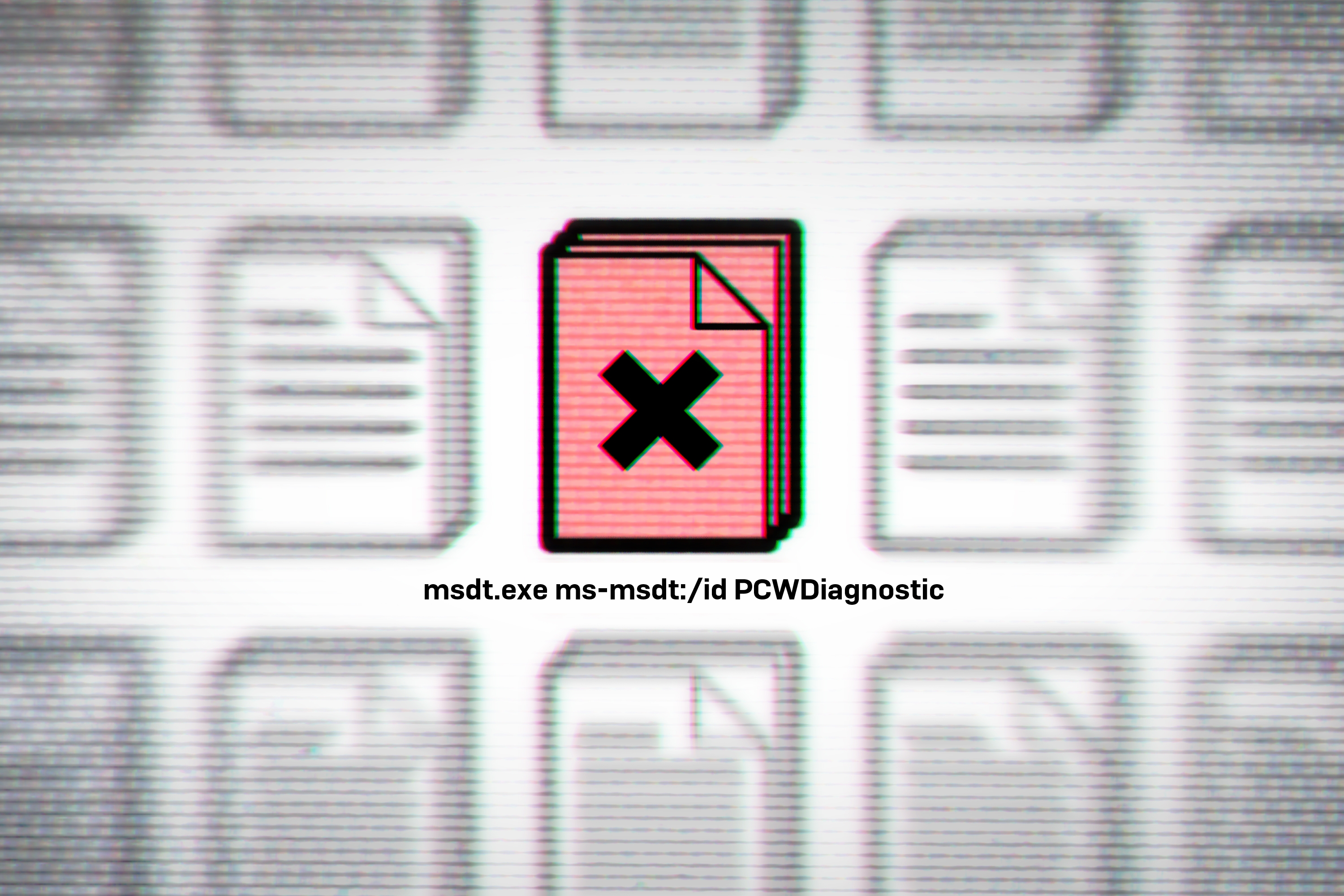
Credit to Author: Andrew Brandt| Date: Tue, 31 May 2022 00:41:42 +0000
MSDT.exe misuse in May makes for Memorial Day Monday mayhem
Read More