Feds Charge Five Men in ‘Scattered Spider’ Roundup
Credit to Author: BrianKrebs| Date: Thu, 21 Nov 2024 20:13:08 +0000
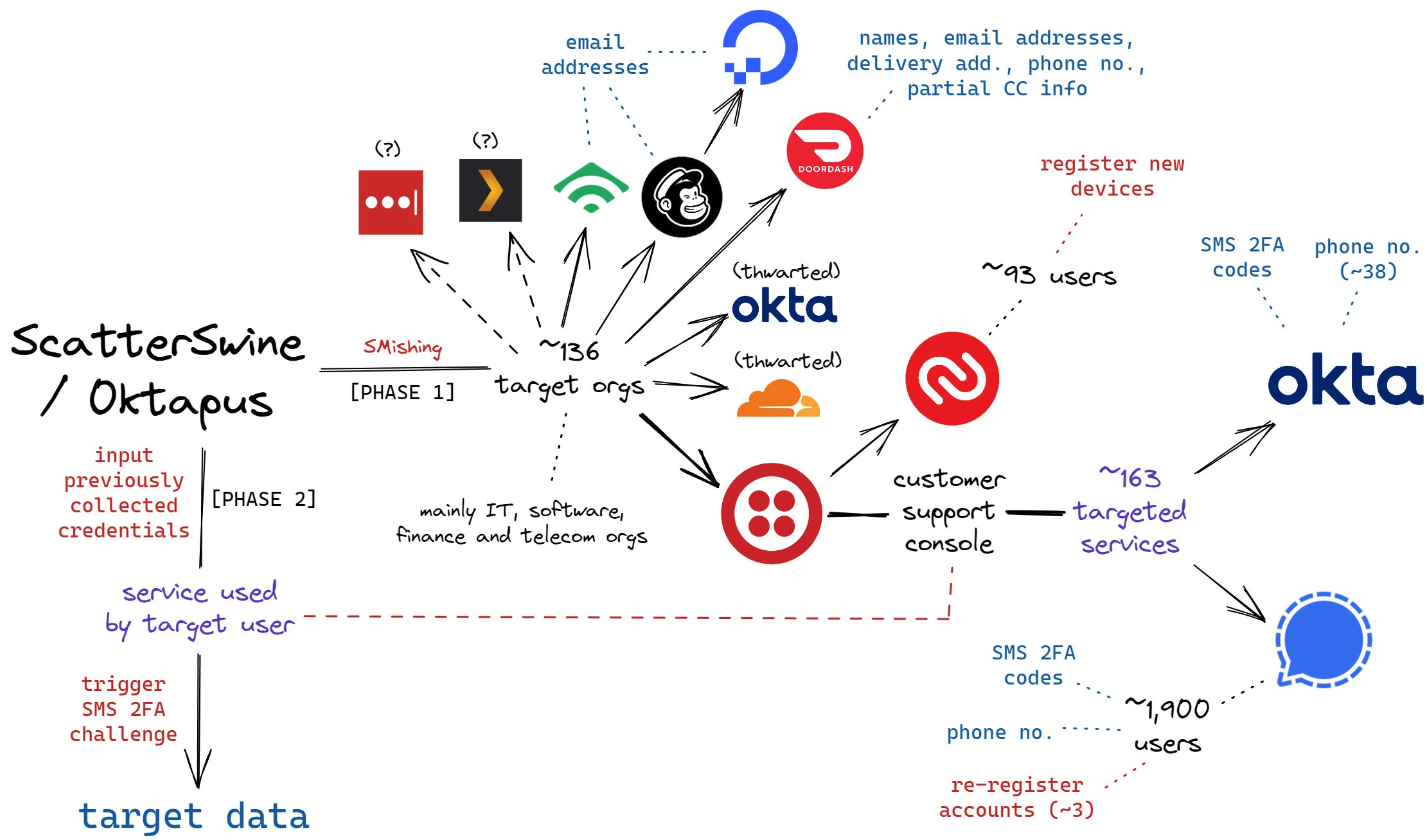
Federal prosecutors in Los Angeles this week unsealed criminal charges against five men alleged to be members of a hacking group responsible for dozens of cyber intrusions at major U.S. technology companies between 2021 and 2023, including LastPass, MailChimp, Okta, T-Mobile and Twilio.
Read More
