SSD安全公告-vBulletin routestring未经验证的远程代码执行

Credit to Author: SSD / Maor Schwartz| Date: Sun, 31 Dec 2017 06:31:17 +0000
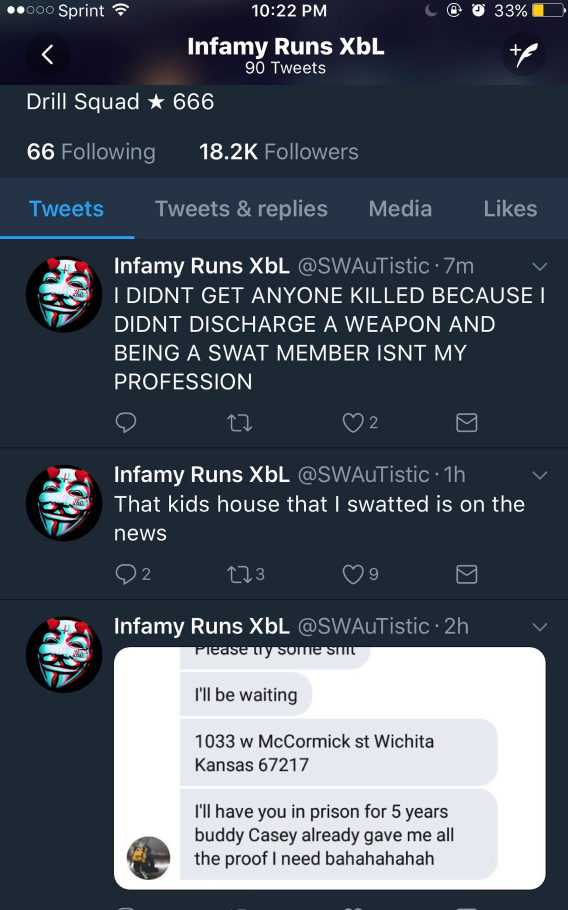
漏洞概要 以下安全公告描述了在vBulletin5中发现的一个未经身份验证的文件包含漏洞,成功利用该漏洞可造成远程代码执行。 vBulletin也称为vB,由vBulletin Solutions公司基于PHP和MySQL开发,广泛用于搭建网络论坛。 vBulletin为许多网络大型的社交网站提供技术支持,数量超过10万,其中包括财富500强和Alexa Top 1M公司的网站和论坛。根据最新的W3Techs1统计,vBulletin 4拥有超过55%的vBulletin市场份额,而vBulletin 3和vBulletin 5则占剩下的45%。 漏洞提交者 一位独立的安全研究人员向 Beyond Security 的 SSD 报告了该漏洞 厂商响应 自2017年11月21日起,我们多次尝试联系vBulletin,但是暂时没有得到回复。目前,漏洞暂时还没有解决方案。 漏洞详细信息 vBulletin存在一个漏洞,导致远程攻击者可以从vBulletin服务器中包含任意文件并执行PHP代码。 未经身份验证的用户可以向/index.php发送GET请求,然后使用参数routestring =触发文件包含漏洞。 该请求允许攻击者向安装在Windows操作系统上的Vbulletin服务器创建精心制作的请求,并在Web服务器上包含任意文件。 /index.php 部分代码: [crayon-5a496258a4faa266544584/] 让我们仔细看看vB5_Frontend_Application :: init — /includes/vb5/frontend/application.php部分代码: [crayon-5a496258a4fb1671370675/] 我们可以看到setRoutes()被调用 /includes/vb5/frontend/routing.php部分代码: [crayon-5a496258a4fb4744772041/] 因此,如果我们的字符串不以’.gif,‘.png’,’.jpg’,’.css’或者‘.js’结尾并且不包含’/’字符,vBulletin会从vB5_Frontend_Controller_Relay中调用legacy() /includes/vb5/frontend/controller/relay.php部分代码: [crayon-5a496258a4fbd144806678/] 如果我们从Api_Interface_Collapsed类中检查relay() /include/api/interface/collapsed.php部分代码: [crayon-5a496258a4fbf779937258/] 正如我们所看到的,攻击者无法在$文件中使用“/”,所以不能在Linux上更改当前目录。但是对于Windows而言,可以使用’’作为路径分隔符,通过PHP包含任意所需的文件(也可以使用’ .. ’技巧)。 如果我们想包含扩展名为’.gif’,’.png’,’.jpg’,’.css’或’.js’这样的文件,需要绕过setRoutes()方法里面的过滤,绕过很容易,可以通过添加点(’.’)或空格(’%20’)到文件名来绕过。 完整的漏洞证明 我们可以通过发送下面的GET请求来检查服务器是否有漏洞: /index.php?routestring=.\ 如果回显是: 那么服务器存在漏洞 如果我们想要在服务器上的任何文件中注入一个php代码,我们可以使用access.log例如: /?LogINJ_START=< ?php phpinfo();?>LogINJ_END … Continue reading SSD安全公告-vBulletin routestring未经验证的远程代码执行
Read More

 Last Sunday, my day could be best described by the lyrics of Sammy Hagar’s song “I Can’t Drive 55.” I was issued a ticket for an alleged speeding infraction. I usually drive about 10 mph over the speed limit, but my “alleged” lead foot got the best of me and so did the Texas Highway…
Last Sunday, my day could be best described by the lyrics of Sammy Hagar’s song “I Can’t Drive 55.” I was issued a ticket for an alleged speeding infraction. I usually drive about 10 mph over the speed limit, but my “alleged” lead foot got the best of me and so did the Texas Highway…
