Cryptojacking Has Gotten Out of Control
Credit to Author: Lily Hay Newman| Date: Fri, 29 Dec 2017 12:00:00 +0000
The practice of using a website visitor’s device to mine cryptocurrency has expanded—and evolved—at an alarming rate.
Read more
Credit to Author: Lily Hay Newman| Date: Fri, 29 Dec 2017 12:00:00 +0000
The practice of using a website visitor’s device to mine cryptocurrency has expanded—and evolved—at an alarming rate.
Read more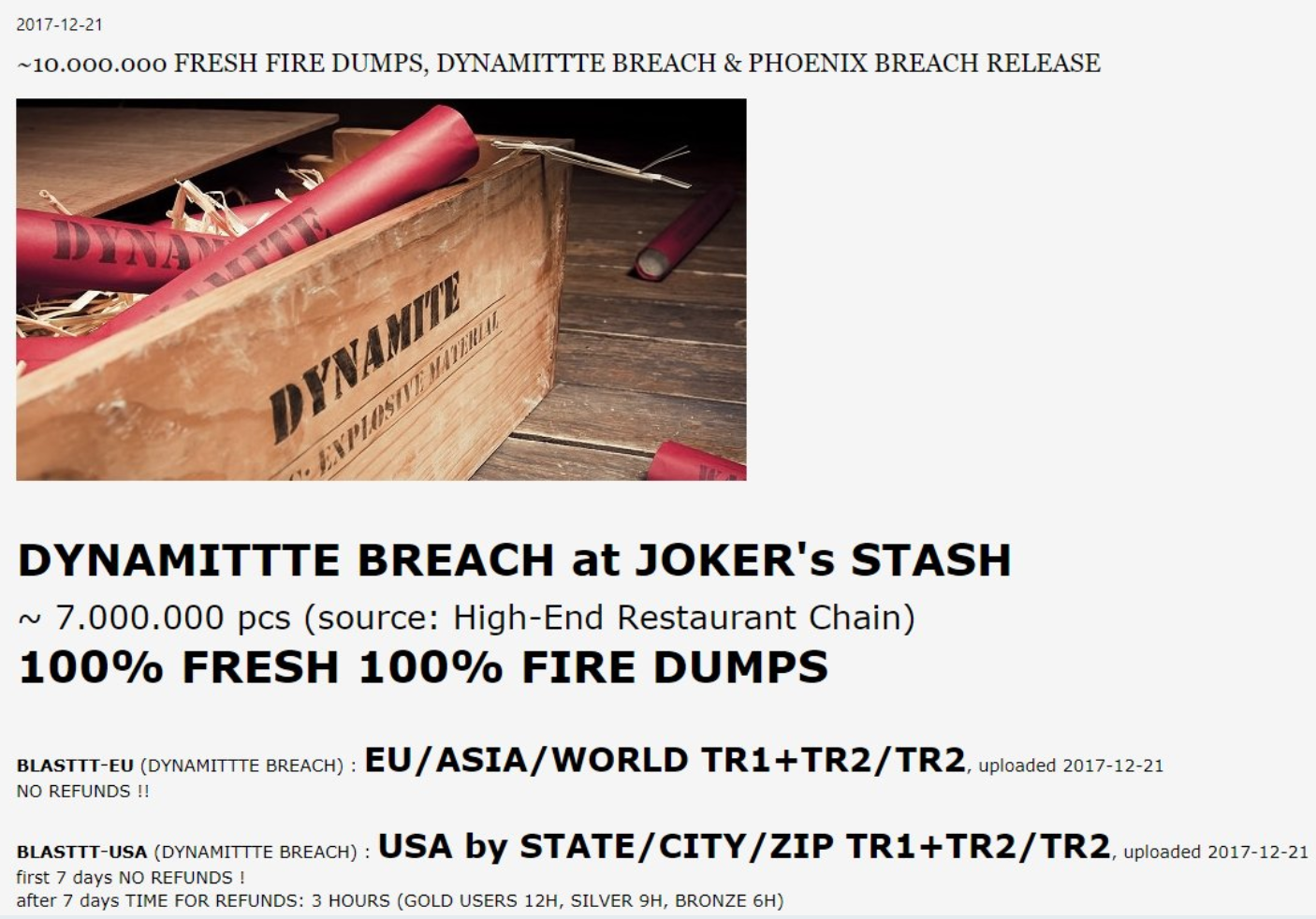
Credit to Author: BrianKrebs| Date: Thu, 28 Dec 2017 15:36:55 +0000
Dec. 18 marked the fourth anniversary of this site breaking the news about a breach at Target involving some 40 million customer credit and debit cards. It has been fascinating in the years since that epic intrusion to see how organized cyber thieves have shifted from targeting big box retailers to hacking a broad swath of small to mid-sized merchants that accept credit cards.
Read more
Credit to Author: Rajoo Nagar| Date: Thu, 28 Dec 2017 13:45:59 +0000
To mitigate the cyber risks associated with Internet of Medical Things (IoMT) devices connecting to healthcare networks, security controls must be put in place to ensure that one compromised medical device does not lead to the compromise of the entire network and the loss of valuable patient data.
Read more
Credit to Author: Wired Staff| Date: Thu, 28 Dec 2017 12:00:00 +0000
From Donald Trump to Russian hackers, these are the dangerous characters we’ve been watching online in 2017.
Read more
Credit to Author: Lucas Mearian| Date: Thu, 28 Dec 2017 03:36:00 -0800
While blockchain technology tends to get the most attention for its role in underpinning cryptocurrencies such as Bitcoin and Ether, vertical industries are quickly adopting it for its efficiency and transparency.
To read this article in full, please click here
(Insider Story)
Read more
Credit to Author: Matt Kapko| Date: Thu, 28 Dec 2017 03:17:00 -0800
Windows Hello is a biometrics-based technology that enables Windows 10 users to authenticate secure access to their devices, apps, online services and networks with just a fingerprint, iris scan or facial recognition. The sign-in mechanism is essentially an alternative to passwords and is widely considered to be a more user friendly, secure and reliable method to access critical devices, services and data than traditional logins using passwords.
“Windows Hello solves a few problems: security and inconvenience,” said Patrick Moorhead, president and principal analyst at Moor Insights & Strategy. “Traditional passwords are unsafe as they are hard to remember, and therefore people either choose easy-to-guess passwords or write down their passwords.”
Credit to Author: Nikolay Pankov| Date: Thu, 28 Dec 2017 07:40:53 +0000
2017’s threat of the year was no contest (and no surprise)
Read more![]()
Credit to Author: Steven J. Vaughan-Nichols| Date: Wed, 27 Dec 2017 09:35:00 -0800
It was that biannual time again when I must buy a new smartphone. My Samsung Galaxy 7’s battery wasn’t holding a charge like it used to, and it was getting a little slower and crankier. So I started looked at the new generation of smartphones. And, after considering both minor- and major-league smartphones such as the Samsung Galaxy 8, iPhone 8 and iPhone X, I got a Google Pixel 2.