Domain Theft Strands Thousands of Web Sites
Credit to Author: BrianKrebs| Date: Mon, 12 Feb 2018 13:41:53 +0000
Newtek Business Services Corp. [NASDAQ:NEWT], a Web services conglomerate that operates more than 100,000 business Web sites and some 40,000 managed technology accounts, had several of its core domain names stolen over the weekend. The theft shut off email and stranded Web sites for many of Newtek’s customers.
An email blast Newtek sent to customers late Saturday evening made no mention of a breach or incident, saying only that the company was changing domains due to “increased” security. A copy of that message can be read here (PDF).
In reality, three of their core domains were hijacked by a Vietnamese hacker, who replaced the login page many Newtek customers used to remotely manage their Web sites (webcontrolcenter[dot]com) with a live Web chat service. As a result, Newtek customers seeking answers to why their Web sites no longer resolved correctly ended up chatting with the hijacker instead.
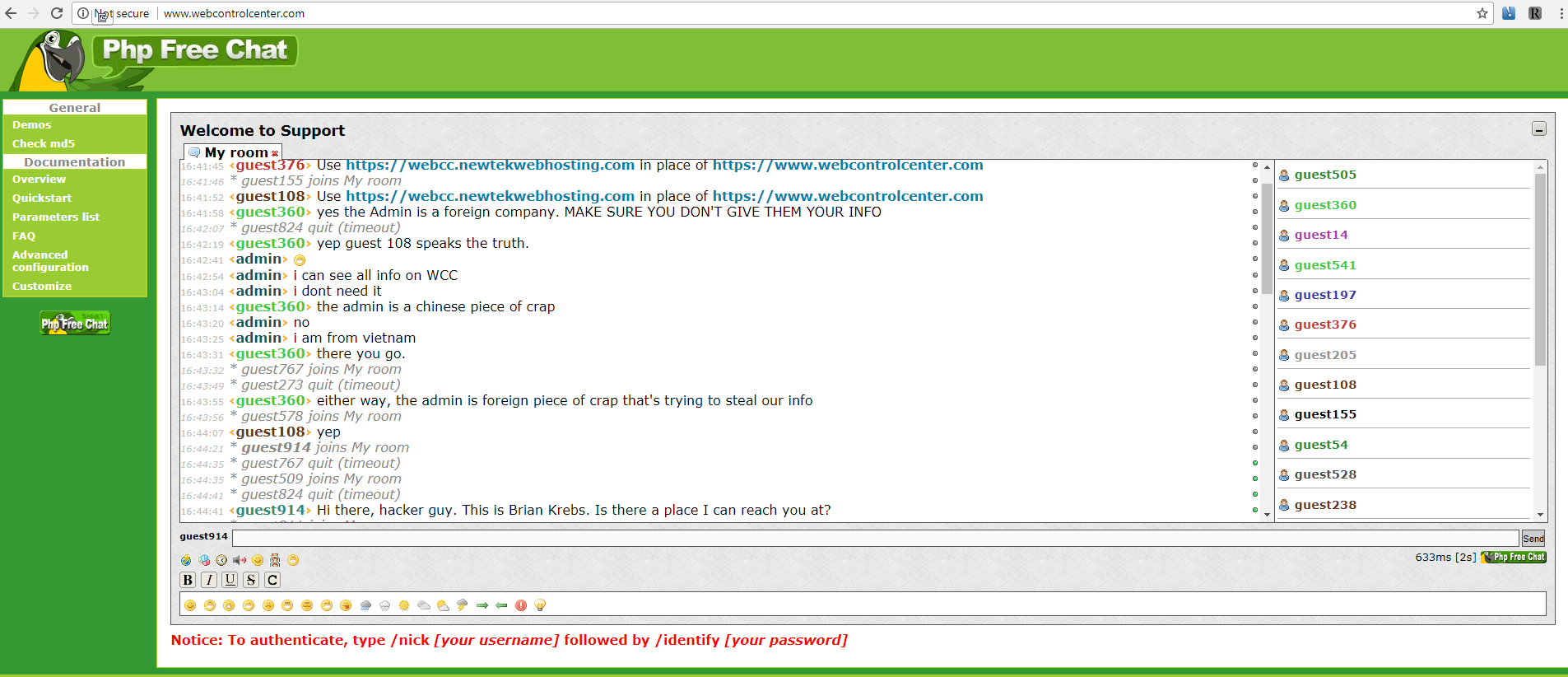
The PHP Web chat client that the intruder installed on Webcontrolcenter[dot]com, a domain that many Newtek customers used to manage their Web sites with the company. The perpetrator can be seen in this chat using the name “admin.” Click to enlarge.
In a follow-up email sent to customers 10 hours later (PDF), Newtek acknowledged the outage was the result of a “dispute” over three domains, webcontrolcenter[dot]com, thesba[dot]com, and crystaltech[dot]com.
“We strongly request that you eliminate these domain names from all your corporate or personal browsers, and avoid clicking on them,” the company warned its customers. “At this hour, it has become apparent that as a result over the dispute for these three domain names, we do not currently have control over the domains or email coming from them.”
The warning continued: “There is an unidentified third party that is attempting to chat and may engage with clients when visiting the three domains. It is imperative that you do not communicate or provide any sensitive data at these locations.”
Newtek did not respond to requests for comment.
Domain hijacking is not a new problem, but it can be potentially devastating to the victim organization. In control of a hijacked domain, a malicious attacker could seamlessly conduct phishing attacks to steal personal information, or use the domain to foist malicious software on visitors.
Newtek is not just a large Web hosting firm: It aims to be a one-stop shop for almost any online service a small business might need. As such, it’s a mix of very different business units rolled up into one since its founding in 1998, including lending solutions, HR, payroll, managed cloud solutions, group health insurance and disaster recovery solutions.
“NEWT’s tentacles go deep into their client’s businesses through providing data security, human resources, employee benefits, payments technology, web design and hosting, a multitude of insurance solutions, and a suite of IT services,” reads a Sept. 2017 profile of the company at SeekingAlpha, a crowdsourced market analysis publication.
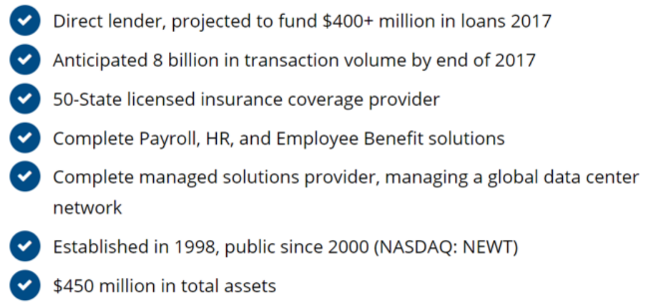
Newtek’s various business lines. Source: Newtek.

Reached via the Web chat client he installed at webcontrolcenter[dot]com, the person who claimed responsibility for the hijack said he notified Newtek five days ago about a “bug” he found in the company’s online operations, but that he received no reply.
A Newtek customer who resells the company’s products to his clients said he had to spend much of the weekend helping clients regain access to email accounts and domains as a result of the incident. The customer, who asked to remain anonymous, said he was shocked that Newtek made little effort to convey the gravity of the hijack to its customers — noting that the company’s home page still makes no mention of the incident.
“They also fail to make it clear that any data sent to any host under the domain could be recorded (email passwords, web credentials, etc.) by the attacker,” he said. “I’m floored at how bad their communication was to their users. I’m not surprised, but concerned, that they didn’t publish the content in the emails directly on their website.”
The source said that at a minimum Newtek should have expired all passwords immediately and required resets through non-compromised hosts.
“And maybe put a notice about this on their home page instead of relying on email, because a lot of my customers can’t get email right now as a result of this,” the source said.
There are a few clues that suggest the perpetrator of these domain hijacks is indeed being truthful about both his nationality and that he located a bug in Newtek’s service. Two of the hijacked domains were moved to a Vietnamese domain registrar (inet.vn).
This individual gave me an email address to contact him at — hd2416@gmail.com — although he has so far not responded to questions beyond promising to reply in Vietenamese. The email is tied to two different Vietnamese-language social networking profiles.
A search at Domaintools indicates that this address is linked to the registration records for four domains, including one (giakiemnew[dot]com) that was recently hosted on a dedicated server operated by Newtek’s legacy business unit Crystaltek [full disclosure: Domaintools is an advertiser on this site]. Recall that Crystaltek[dot]com was among the three hijacked domains.
In addition, the domain giakiemnew[dot]com was registered through Newtek Technology Services, a domain registration service offered by Newtek. This suggests that the perpetrator was in fact a customer of Newtek, and perhaps did discover a vulnerability while using the service.