Discover and manage shadow IT with Microsoft 365
Credit to Author: Todd VanderArk| Date: Mon, 15 Apr 2019 16:00:46 +0000
While IT teams methodically plan corporate adoption of cloud services, the rest of us have dived in headfirst. Ten years ago, a vendor shared a video file with me via Dropbox because it was too big to email. It was my first experience with a cloud file sharing service, and when I realized I could get free storage, I was hooked. I created an account for work projects, and I also created personal folders to share photos and music with friends. It was super easy to use, and best of all, I was able to do it without needing a technical background or access to a corporate server. In fact, it didn’t even occur to me that IT might need to know that I was accessing a cloud app from the corporate network.
A lot has happened in the past decade. Mobile phones function as secondary work computers, cloud app usage has proliferated, and I’ve gotten much smarter about cybersecurity. What hasn’t changed is how cloud apps are introduced to the enterprise: through industrious employees, coworkers, partners, and vendors. This is one of the big challenges that we in the security community face. Bad actors use sophisticated methods to exploit personal devices and cloud apps to gain access to enterprise resources, because it’s hard to track and secure the technologies that employees use to stay connected and productive.
Our second e-book in the series, Discover and manage shadow IT, delves into this problem and provides real-world solutions. It tells the story of how a (fictitious) SecOps manager named Luis uses the security capabilities in Microsoft 365 to help the sales team find the best tools to collaborate without putting the enterprise at risk.
Discover unsanctioned cloud apps
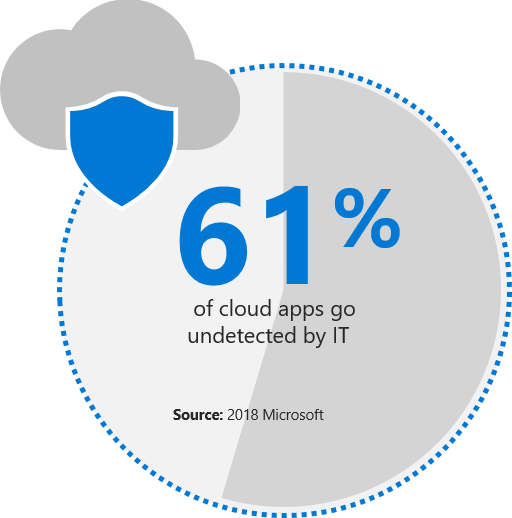
If you feel uncertain about the state of your own shadow IT, you aren’t alone. According to Microsoft’s internal numbers, on average, enterprises are using over 1,100 cloud apps, yet 61 percent go undetected by IT. The Discover and manage shadow IT e-book illustrates how Microsoft Cloud App Security and other products in Microsoft 365 Enterprise E5 can help you detect the apps that people in your organization use. You can even be alerted when new cloud apps are introduced.
Detect which apps are risky and block them
Once you discover a cloud app, how do you know if it is safe or not? The e-book provides several examples of how Microsoft 365 Enterprise E5 harnesses the intelligence across all its products and endpoints to help you evaluate the risk level of each app. You can dig into details including who is using the app and how privileged their access is. If an app doesn’t meet your compliance and risk standards, you can use Microsoft Cloud App Security to block it.
Manage devices and apps
Unknown devices can be just as risky as cloud apps. If a user hasn’t maintained their device operating system or software, there may be a security vulnerability that can be exploited. The Discover and manage shadow IT e-book shows how Microsoft Intune helps to enforce security policies for personal devices. You’ll also learn how you can onboard sanctioned apps to make it easier and more secure for users to access them.
Learn more
Like most people, my use of cloud apps has increased over the years. I still use Dropbox to share personal files, but I’ve also added Box and Microsoft OneDrive. Most often, I access these apps using my personal iPhone. Intune keeps my personal and work data separate, and Microsoft Cloud App Security applies corporate security policies whenever I sign in to a cloud service. It’s just as easy to access the apps I need as it was ten years ago, but now I don’t worry about putting my company at risk.
To learn more, download the first two e-books in our series:
- Discover and manage shadow IT—For more details on how you can discover cloud apps, detect and block risky apps, and securely manage apps and devices.
- Secure access to your enterprise—To learn how you can move your organization towards a password-less future.
Also, stay tuned for the third e-book in our series, “Defend your digital landscape,” which provides tips for defending and responding to a security breach.
The post Discover and manage shadow IT with Microsoft 365 appeared first on Microsoft Security.