How and why you need HomeKit-secured smart homes
Credit to Author: Jonny Evans| Date: Thu, 27 Feb 2020 04:40:00 -0800
Once upon a time the Internet was amazing, enabling niche interests and connecting people. Apple’s iMac was the epitome of the era, while the iPhone became the prophet of change.
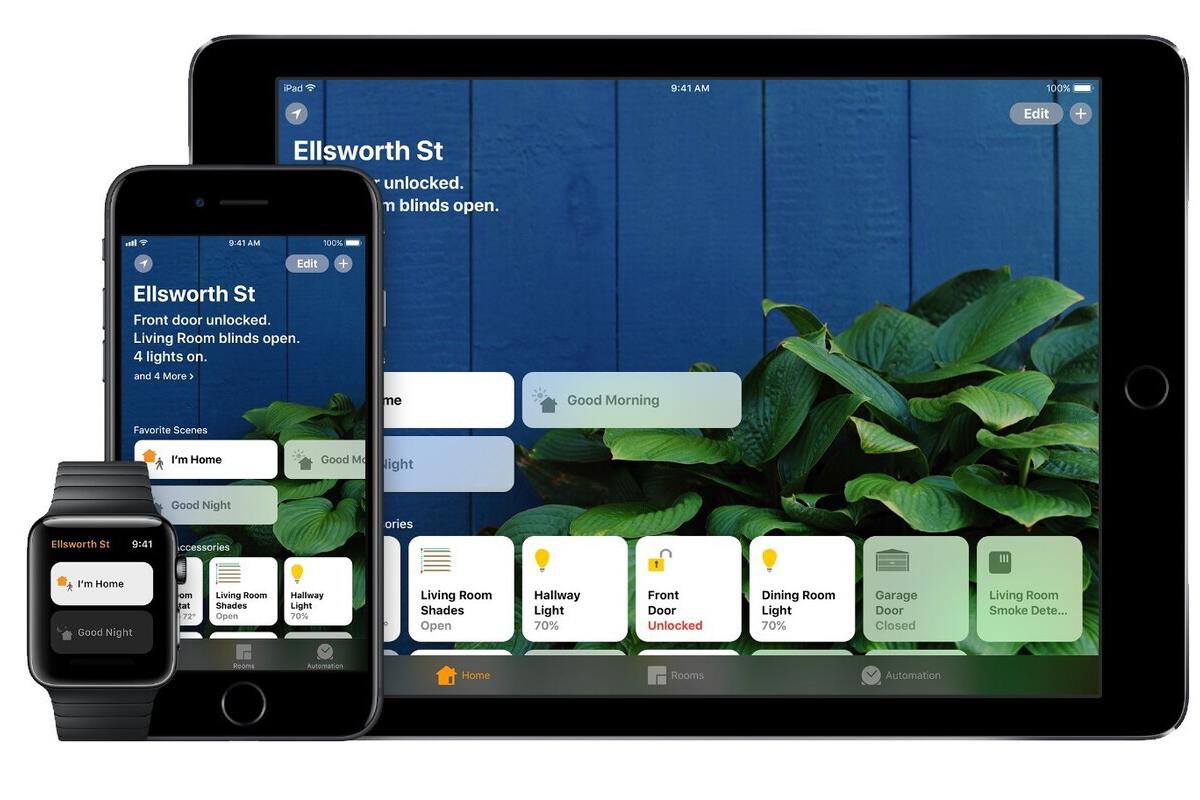
These days hackers break into home networks using our routers and smart home devices, which is why everyone must learn how to use HomeKit-secured routers to keep their connected homes safe.
Apple announced HomeKit-secured routers at WWDC 2019. The first few devices to support the tech recently began to reach market, including options from Linksys and (now) Amazon’s Eero routers.
HomeKit-secured routers provide an additional level of defence between your connected smart home devices and the outside world.
This is of benefit because by putting this ‘wall’ in place, your smart devices become a little harder to hack.
You don’t want criminals taking control of your smart locks, smart baby camera or smart anything, really, do you? You certainly won’t want them to attack your HomeKit devices in order to subvert your home network, or monitoring what your HomeKit devices do in order to figure out when your house is empty and vulnerable.
HomeKit-secured routers let you protect each of your HomeKit devices with one of three levels of protection.
These include:
Restrict to Home: The toughest setting, this restricts your devices so that they “can interact only with HomeKit through your Apple devices.” This means they have no independent access to the internet and means you must manually download software updates. But this also means no one can get to those devices unless they take control of your device.
Automatic: The default option allows for limited internet access with connections restricted to those “recommended by its manufacturer”.
No Restriction: This is what it says on the can. It is the least secure option that provides no protection at all. I wouldn’t recommend it unless you have a pressing need for it.
HomeKit-secured routers also provide iOS or iPadOS apps which you can get from the App Store and will require when setting up these systems.
First, download and install the relevant app for you router, open it and follow the manufacturer’s set-up instructions.
Because most smart home devices are actually pretty dumb, the next stage of the process is slightly annoying but necessary.
It basically comes down to switching all your HomeKit-enabled products off and switching them on again, which I suspect (though Apple didn’t say) is required to reset the (dumb) low-power processors inside these things.
It means you must remove any existing accessories you’ve already set up, which is a shame as doing so also means all the data, including accessories, scenes, automations and people you’ve invited to control your home will be deleted.
You’ll have to set them all up for your preferences once again.
There are two ways to remove the devices: You can remove individual accessories from your Home app or delete your entire home set-up in the app in order to reconfigure the whole thing from scratch.
Once you’ve removed the accessories (or your home setup) you’ll need to reset you accessories **.
** This is likely to be a tedious process, as you will need to find the tiny reset button that may exist on each of your HomeKit devices. If you can’t find that button, you’ll need to read the manual, spend half a day trying to find out more information on the manufacturer’s website, or contact the manufacturer to begin negotiating for help with its customer support service. Good luck with that.
As you add HomeKit devices to your home setup, you’ll be given the opportunity to define access privileges, which works like this:
You now know how to set this system up, but given that doing so may be a little time-consuming, it’s probably worth reprising why it’s important to take on the task.
If properly configured, most routers are smart enough to distinguish between potentially dangerous incoming traffic and traffic from (assumed to be authorized) systems you have installed in your home.
However, not every device is as well secured as you might think.
Many of the early generation smart home devices shipped with weak security, while some may even carry malware already inside the chip.
In the former case, an attacker who can find the device may want to use it to help them climb inside your home network. In the latter scenario, that trusted device may be sharing all kinds of information about you with people you know nothing about.
Spooky, huh?
That’s why limiting your smart home devices in terms of their access to the internet is the smart thing to do. If they can’t contact people, or can only contact a very limited sub-set of people, then your are a little safer. If they can’t be found, you’re safer too.
So, is this really something to worry about?
Well, clearly Apple thinks it is, and it is telling that Amazon seems to agree, given addition of HomeKit support to its Eero routers.
It’s also important to consider that pretty much the entire smart home device industry is now working with Apple to develop more secure, more compatible connectivity standard.
“The project is built around a shared belief that smart home devices should be secure, reliable, and seamless to use,” the partners said announcing this.
What are they concerned about? It’s possible they are also aware of Kaspersky research claims that attacks against smart home devices climbed by 700% across 2018-19.
So, while the need to rebuild your entire smart home setup in order to use HomeKit-secured routers may seem frustrating, the added security you get justifies the work.
Of course, many Computerworld readers are experts and may already have found their own ways to improve their own smart home (or office) security. That’s great. However, for many the fact that Apple now offers such tools makes such protection available to them, probably for the first time.
With this in mind, and the scale of the evident threat model, I’d urge anyone with a HomeKit set-up to begin taking steps to implement this kind of protection.
In an ideal world, cable and broadband suppliers would upgrade the routers they supply with support for HomeKit security as a matter of urgency — and it may be worth customers applying pressure to make sure they do. Why not contact your provider and ask about this?
Please follow me on Twitter, or join me in the AppleHolic’s bar & grill and Apple Discussions groups on MeWe.