July’s Patch Tuesday: A rich harvest
Credit to Author: Angela Gunn| Date: Tue, 11 Jul 2023 17:18:08 +0000
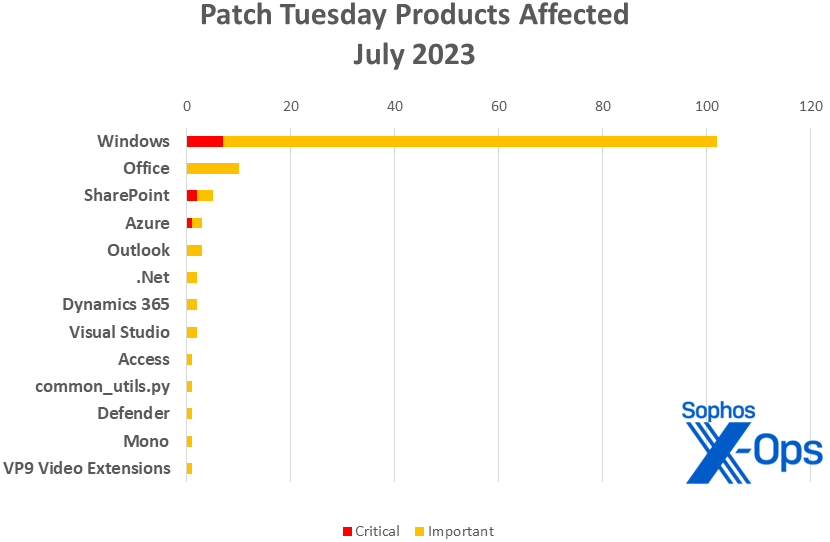
Microsoft on Tuesday released patches for 129 vulnerabilities, including seven critical-severity issues in Windows and two in SharePoint. As usual, the largest number of addressed vulnerabilities affect Windows with 104 CVEs, including two that also affect Azure. Office takes 10 patches, including three that it shares with Outlook and one that it shares with Access. SharePoint takes five. Azure takes four, though two of those are shared with Windows as noted above. Microsoft Dynamics takes two. Visual Studio and .NET share a patch and each takes another one of their own.
Microsoft is also publishing three advisories that bear a closer look. ADV230001, “Guidance on Microsoft Signed Drivers Being Used Maliciously,” addresses an issue under sustained active exploit for multiple products. For an in-depth look at the situation, including Sophos X-Ops’ role in its discovery, please see the accompanying article; Microsoft has also published a Knowledge Base article on the matter. ADV230002, “Microsoft Guidance for Addressing Security Feature Bypass in Trend Micro EFI Modules,” is also included this month, as is ADV990001, covering the latest Servicing Stack updates.
In addition to the issue detailed in ADV230001, Microsoft flags four patched CVEs, all Important-severity, as being under active exploitation in the wild. Two of those (CVE-2023-32049, CVE-2023-35311) are security bypass issues. In the former, an attacker wielding CVE-2023-32049 could send to a target a specially crafted URL that, if clicked, could bypass the usual Open File – Security Warning prompt; likewise, in the latter, a specially crafted URL could lead to bypass of the Outlook security-notice prompt. The other two issues under active exploitation are elevation-of-privilege issues touching MSHTML and the Windows Error Reporting Service.
In addition, Microsoft cautions that three of the Windows issues and two of the SharePoint issues addressed are more likely to be exploited in either the latest or earlier versions of the affected product soon (that is, within the next 30 days).
Beyond this update, Microsoft also offered information on three Adobe CVEs (CVE-2023-29298, CVE-2023-29300, CVE-2023-29301) being patched today in Bulletin APSB23-40. All three touch ColdFusion and affect CF2018 update 16, CF2021 update 6, CF2023 GA Release (2023.0.0) and earlier, and Adobe states that all three are less likely to be exploited in the next 30 days. None of the three are previously publicly disclosed.
We are including at the end of this post three appendices listing all Microsoft’s patches, sorted by severity, by predicted exploitability, and by product family.
By the numbers
- Total Microsoft CVEs: 129
- Total advisories shipping in update: 3
- Publicly disclosed: 0
- Exploited: 5 (including ADV230001)
- Severity
- Critical: 9
- Important: 120
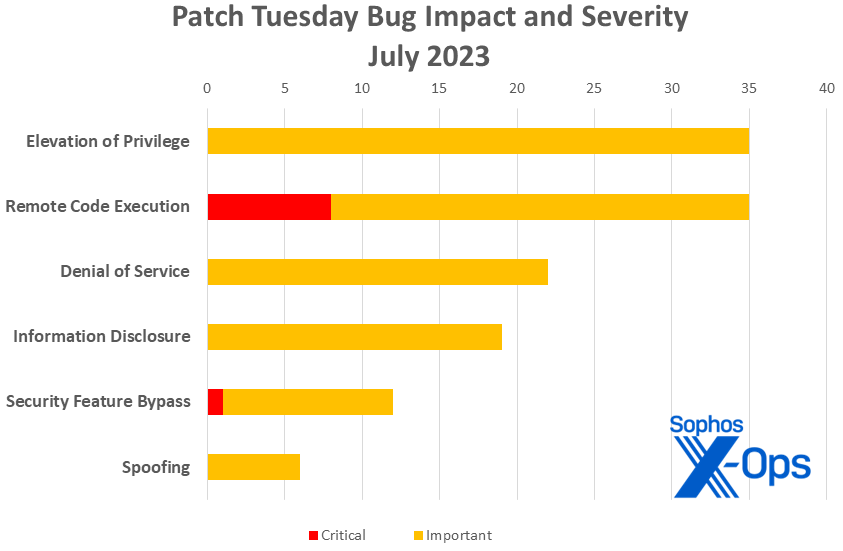
- Impact
- Elevation of Privilege: 35
- Remote Code Execution: 35
- Denial of Service: 22
- Information Disclosure: 19
- Security Feature Bypass: 12
- Spoofing: 6
Figure 1: An equal number of RCE and EoP issues this month are joined by a bumper crop of Security Feature Bypasses – one Critical-class
Products
- Windows (includes 2 shared with Azure): 104
- Office (includes one shared with Access and 3 with Outlook): 10
- SharePoint: 5
- Azure: 3
- Outlook: 3
- .NET (includes one shared with Visual Studio): 2
- Dynamics 365: 2
- Visual Studio (includes one shared with .NET): 2
- Access (shared with Office): 1
- common_utils.py: 1
- Defender: 1
- Mono: 1
- VP9 Video Extensions: 1
Figure 2: A large number of product families make an appearance in July’s Patch Tuesday set, but Windows continues to rule the roost. (For patches shared by multiple families, the numbers above reflect an instance for each family affected – for example, Visual Studio and .NET each have one patch of their own and share one patch, so in this chart each shows as having two patches)
Notable July updates
ADV230001 – Guidance on Microsoft Signed Drivers Being Used Maliciously
The discovery that drivers certified by Microsoft’s own Window Hardware Developer Program (MWHDP) were being used maliciously in post-exploitation activity will, according to the text of the advisory itself, lead to “long-term solutions to address these deceptive practices and prevent future customer impacts” at Microsoft. In the meantime, please see “Microsoft Revokes Malicious Drivers in Patch Tuesday Culling” for detailed information on what we found.
CVE-2023-35352 — Windows Remote Desktop Security Feature Bypass Vulnerability
This server-side issue is the month’s sole non-RCE Critical-class patch, and Microsoft assesses that it is more likely to be exploited in the next 30 days. An attacker who successfully exploited CVE-2023-35352 could bypass certificate or private key authentication when establishing a remote desktop protocol session.
CVE-2023-35308 – Windows MSHTML Platform Security Feature Bypass Vulnerability
CVE-2023-35336 — Windows MSHTML Platform Security Feature Bypass Vulnerability
So here’s something you probably weren’t expecting today: Internet Explorer patches. Though IE and even Edge Legacy are deprecated, the MSHTML, EdgeHTML, and scripting programs that lay beneath them are still very much present in Windows. Microsoft therefore states that all versions of Windows except Server 2008, Server 2008 R2, and Server 2012 are affected, and that customers who install Security Only updates should install the IE Cumulative updates to address this one. These aren’t the only MSHTML vulnerabilities this month, nor the most concerning – CVE-2023-32046, an Important-class Elevation of Privilege issue, is under active exploitation in the wild – but it’s definitely odd to see the ghost of the much-maligned Internet Explorer still haunting Patch Tuesday in 2023.
CVE-2023-35333 – MediaWiki PandocUpload Extension Remote Code Execution Vulnerability
CVE-2023-35373 – Mono Authenticode Validation Spoofing Vulnerability
These two items come from product families a little less familiar to regular followers of Patch Tuesday. MediaWiki extensions are developed by Microsoft for internal use, but are accessible to the public via Microsoft’s GitHub; Mono is the venerable open-source .NET-compatible software framework. Both vulnerabilities are judged by Microsoft as less likely to be exploited in the next 30 days, neither is believed to be under exploit in the wild, and both were cooperatively disclosed to Microsoft.
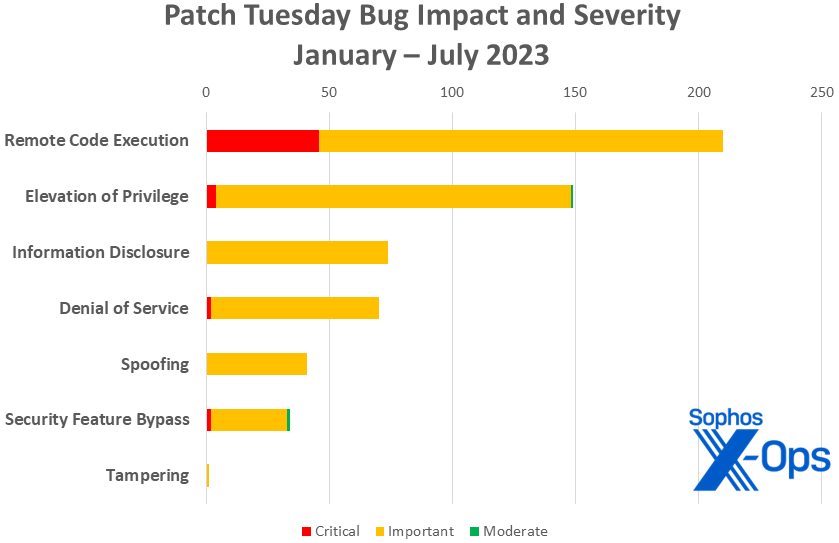
Figure 3: As the year goes on, remote code execution flaws continue to lead the Patch Tuesday pack
Sophos protections
As you can every month, if you don’t want to wait for your system to pull down Microsoft’s updates itself, you can download them manually from the Windows Update Catalog website. Run the winver.exe tool to determine which build of Windows 10 or 11 you’re running, then download the Cumulative Update package for your specific system’s architecture and build number.
Appendix A: Vulnerability Impact and Severity
This is a list of July’s patches sorted by impact, then sub-sorted by severity. Each list is further arranged by CVE.
Remote Code Execution (35 CVEs)
| Critical severity | |
| CVE-2023-32057 | Microsoft Message Queuing Remote Code Execution Vulnerability |
| CVE-2023-33157 | Microsoft SharePoint Remote Code Execution Vulnerability |
| CVE-2023-33160 | Microsoft SharePoint Server Remote Code Execution Vulnerability |
| CVE-2023-35297 | Windows Pragmatic General Multicast (PGM) Remote Code Execution Vulnerability |
| CVE-2023-35315 | Windows Hyper-V Remote Code Execution Vulnerability |
| CVE-2023-35365 | Windows Routing and Remote Access Service (RRAS) Remote Code Execution Vulnerability |
| CVE-2023-35366 | Windows Routing and Remote Access Service (RRAS) Remote Code Execution Vulnerability |
| CVE-2023-35367 | Windows Routing and Remote Access Service (RRAS) Remote Code Execution Vulnerability |
| Important severity | |
| CVE-2023-32033 | Microsoft Cluster Server Service Remote Code Execution Vulnerability |
| CVE-2023-32038 | Microsoft ODBC Driver Remote Code Execution Vulnerability |
| CVE-2023-32047 | Paint 3D Remote Code Execution Vulnerability |
| CVE-2023-32051 | Raw Image Extension Remote Code Execution Vulnerability |
| CVE-2023-33134 | Microsoft SharePoint Server Remote Code Execution Vulnerability |
| CVE-2023-33149 | Microsoft Office Graphics Remote Code Execution Vulnerability |
| CVE-2023-33152 | Microsoft Access Remote Code Execution Vulnerability |
| CVE-2023-33153 | Microsoft Outlook Remote Code Execution Vulnerability |
| CVE-2023-33158 | Microsoft Excel Remote Code Execution Vulnerability |
| CVE-2023-33161 | Microsoft Excel Remote Code Execution Vulnerability |
| CVE-2023-33163 | Windows Network Load Balancing Remote Code Execution Vulnerability |
| CVE-2023-35300 | Remote Procedure Call Runtime Remote Code Execution Vulnerability |
| CVE-2023-35302 | Microsoft PostScript and PCL6 Class Printer Driver Remote Code Execution Vulnerability |
| CVE-2023-35309 | Microsoft Message Queuing Remote Code Execution Vulnerability |
| CVE-2023-35310 | Windows DNS Server Remote Code Execution Vulnerability |
| CVE-2023-35313 | Windows Online Certificate Status Protocol (OCSP) SnapIn Remote Code Execution Vulnerability |
| CVE-2023-35322 | Windows Deployment Services Remote Code Execution Vulnerability |
| CVE-2023-35323 | Windows OLE Remote Code Execution Vulnerability |
| CVE-2023-35333 | Media-Wiki Extensions Remote Code Execution Vulnerability |
| CVE-2023-35343 | Windows Geolocation Service Remote Code Execution Vulnerability |
| CVE-2023-35344 | Windows DNS Server Remote Code Execution Vulnerability |
| CVE-2023-35345 | Windows DNS Server Remote Code Execution Vulnerability |
| CVE-2023-35346 | Windows DNS Server Remote Code Execution Vulnerability |
| CVE-2023-35350 | Windows Active Directory Certificate Services (AD CS) Remote Code Execution Vulnerability |
| CVE-2023-35351 | Windows Active Directory Certificate Services (AD CS) Remote Code Execution Vulnerability |
| CVE-2023-35374 | Paint 3D Remote Code Execution Vulnerability |
| CVE-2023-36867 | Visual Studio Code GitHub Pull Requests and Issues Extension Remote Code Execution Vulnerability |
Elevation of Privilege (35 CVEs)
| Important severity | |
| CVE-2023-21756 | Windows Win32k Elevation of Privilege Vulnerability |
| CVE-2023-32046 | Windows MSHTML Platform Elevation of Privilege Vulnerability |
| CVE-2023-32050 | Windows Installer Elevation of Privilege Vulnerability |
| CVE-2023-32053 | Windows Installer Elevation of Privilege Vulnerability |
| CVE-2023-32054 | Volume Shadow Copy Elevation of Privilege Vulnerability |
| CVE-2023-32055 | Active Template Library Elevation of Privilege Vulnerability |
| CVE-2023-32056 | Windows Update Stack Elevation of Privilege Vulnerability |
| CVE-2023-33127 | .NET and Visual Studio Elevation of Privilege Vulnerability |
| CVE-2023-33148 | Microsoft Office Elevation of Privilege Vulnerability |
| CVE-2023-33154 | Windows Partition Management Driver Elevation of Privilege Vulnerability |
| CVE-2023-33155 | Windows Cloud Files Mini Filter Driver Elevation of Privilege Vulnerability |
| CVE-2023-33156 | Microsoft Defender Elevation of Privilege Vulnerability |
| CVE-2023-35299 | Windows Common Log File System Driver Elevation of Privilege Vulnerability |
| CVE-2023-35303 | USB Audio Class System Driver Remote Code Execution Vulnerability |
| CVE-2023-35304 | Windows Kernel Elevation of Privilege Vulnerability |
| CVE-2023-35305 | Windows Kernel Elevation of Privilege Vulnerability |
| CVE-2023-35312 | Microsoft VOLSNAP.SYS Elevation of Privilege Vulnerability |
| CVE-2023-35317 | Windows Update Stack Elevation of Privilege Vulnerability |
| CVE-2023-35320 | Connected User Experiences and Telemetry Elevation of Privilege Vulnerability |
| CVE-2023-35328 | Windows Transaction Manager Elevation of Privilege Vulnerability |
| CVE-2023-35337 | Win32k Elevation of Privilege Vulnerability |
| CVE-2023-35340 | Windows CNG Key Isolation Service Elevation of Privilege Vulnerability |
| CVE-2023-35342 | Windows Image Acquisition Elevation of Privilege Vulnerability |
| CVE-2023-35347 | Microsoft Store Install Service Elevation of Privilege Vulnerability |
| CVE-2023-35353 | Connected User Experiences and Telemetry Elevation of Privilege Vulnerability |
| CVE-2023-35355 | Windows Cloud Files Mini Filter Driver Elevation of Privilege Vulnerability |
| CVE-2023-35356 | Windows Kernel Elevation of Privilege Vulnerability |
| CVE-2023-35357 | Windows Kernel Elevation of Privilege Vulnerability |
| CVE-2023-35358 | Windows Kernel Elevation of Privilege Vulnerability |
| CVE-2023-35360 | Windows Kernel Elevation of Privilege Vulnerability |
| CVE-2023-35361 | Windows Kernel Elevation of Privilege Vulnerability |
| CVE-2023-35362 | Windows Clip Service Elevation of Privilege Vulnerability |
| CVE-2023-35363 | Windows Kernel Elevation of Privilege Vulnerability |
| CVE-2023-35364 | Windows Kernel Elevation of Privilege Vulnerability |
| CVE-2023-36874 | Windows Error Reporting Service Elevation of Privilege Vulnerability |
Denial of Service (22 CVEs)
| Important severity | |
| CVE-2023-32034 | Remote Procedure Call Runtime Denial of Service Vulnerability |
| CVE-2023-32035 | Remote Procedure Call Runtime Denial of Service Vulnerability |
| CVE-2023-32044 | Microsoft Message Queuing Denial of Service Vulnerability |
| CVE-2023-32045 | Microsoft Message Queuing Denial of Service Vulnerability |
| CVE-2023-32084 | HTTP.sys Denial of Service Vulnerability |
| CVE-2023-33164 | Remote Procedure Call Runtime Denial of Service Vulnerability |
| CVE-2023-33166 | Remote Procedure Call Runtime Denial of Service Vulnerability |
| CVE-2023-33167 | Remote Procedure Call Runtime Denial of Service Vulnerability |
| CVE-2023-33168 | Remote Procedure Call Runtime Denial of Service Vulnerability |
| CVE-2023-33169 | Remote Procedure Call Runtime Denial of Service Vulnerability |
| CVE-2023-33172 | Remote Procedure Call Runtime Denial of Service Vulnerability |
| CVE-2023-33173 | Remote Procedure Call Runtime Denial of Service Vulnerability |
| CVE-2023-35298 | HTTP.sys Denial of Service Vulnerability |
| CVE-2023-35314 | Remote Procedure Call Runtime Denial of Service Vulnerability |
| CVE-2023-35318 | Remote Procedure Call Runtime Denial of Service Vulnerability |
| CVE-2023-35319 | Remote Procedure Call Runtime Denial of Service Vulnerability |
| CVE-2023-35321 | Windows Deployment Services Denial of Service Vulnerability |
| CVE-2023-35329 | Windows Authentication Denial of Service Vulnerability |
| CVE-2023-35330 | Windows Extended Negotiation Denial of Service Vulnerability |
| CVE-2023-35331 | Windows Local Security Authority (LSA) Denial of Service Vulnerability |
| CVE-2023-35338 | Windows Peer Name Resolution Protocol Denial of Service Vulnerability |
| CVE-2023-35339 | Windows CryptoAPI Denial of Service Vulnerability |
Information Disclosure (19 CVEs)
| Important severity | |
| CVE-2023-21526 | Windows Netlogon Information Disclosure Vulnerability |
| CVE-2023-32037 | Windows Layer 2 Tunneling Protocol (L2TP) Information Disclosure Vulnerability |
| CVE-2023-32039 | Microsoft PostScript and PCL6 Class Printer Driver Information Disclosure Vulnerability |
| CVE-2023-32040 | Microsoft PostScript and PCL6 Class Printer Driver Information Disclosure Vulnerability |
| CVE-2023-32041 | Windows Update Orchestrator Service Information Disclosure Vulnerability |
| CVE-2023-32042 | OLE Automation Information Disclosure Vulnerability |
| CVE-2023-32083 | Windows Failover Cluster Information Disclosure Vulnerability |
| CVE-2023-32085 | Microsoft PostScript and PCL6 Class Printer Driver Information Disclosure Vulnerability |
| CVE-2023-33162 | Microsoft Excel Information Disclosure Vulnerability |
| CVE-2023-33174 | Windows Kernel Memory Information Disclosure Vulnerability |
| CVE-2023-35296 | Microsoft PostScript and PCL6 Class Printer Driver Information Disclosure Vulnerability |
| CVE-2023-35306 | Microsoft PostScript and PCL6 Class Printer Driver Information Disclosure Vulnerability |
| CVE-2023-35316 | Remote Procedure Call Runtime Information Disclosure Vulnerability |
| CVE-2023-35324 | Microsoft PostScript and PCL6 Class Printer Driver Information Disclosure Vulnerability |
| CVE-2023-35325 | Windows Print Spooler Information Disclosure Vulnerability |
| CVE-2023-35326 | Windows CDP User Components Information Disclosure Vulnerability |
| CVE-2023-35341 | Windows Media Information Disclosure Vulnerability |
| CVE-2023-36868 | Service Fabric on Windows Information Disclosure Vulnerability |
| CVE-2023-36872 | VP9 Video Extensions Information Disclosure Vulnerability |
Security Feature Bypass (12 CVEs)
| Critical severity | |
| CVE-2023-35352 | Windows Remote Desktop Security Feature Bypass Vulnerability |
| Important severity | |
| CVE-2023-32043 | Windows Remote Desktop Security Feature Bypass Vulnerability |
| CVE-2023-32049 | Windows SmartScreen Security Feature Bypass Vulnerability |
| CVE-2023-33150 | Microsoft Office Security Feature Bypass Vulnerability |
| CVE-2023-33165 | Microsoft SharePoint Server Security Feature Bypass Vulnerability |
| CVE-2023-33170 | ASP.NET Core Security Feature Bypass Vulnerability |
| CVE-2023-35308 | Windows MSHTML Platform Security Feature Bypass Vulnerability |
| CVE-2023-35311 | Microsoft Outlook Security Feature Bypass Vulnerability |
| CVE-2023-35332 | Windows Remote Desktop Protocol Security Feature Bypass |
| CVE-2023-35336 | Windows MSHTML Platform Security Feature Bypass Vulnerability |
| CVE-2023-35348 | Azure Active Directory Security Feature Bypass Vulnerability |
| CVE-2023-36871 | Azure Active Directory Security Feature Bypass Vulnerability |
Spoofing (6 CVEs)
| Important severity | |
| CVE-2023-29347 | Windows Admin Center Spoofing Vulnerability |
| CVE-2023-32052 | Microsoft Power Apps Spoofing Vulnerability |
| CVE-2023-33151 | Microsoft Outlook Spoofing Vulnerability |
| CVE-2023-33159 | Microsoft SharePoint Server Spoofing Vulnerability |
| CVE-2023-33171 | Microsoft Dynamics 365 (on-premises) Cross-site Scripting Vulnerability |
| CVE-2023-35373 | Mono Authenticode Validation Elevation of Privilege Vulnerability |
Appendix B: Exploitability
This is a list of the July CVEs judged by Microsoft to be more likely to be exploited in the wild within the first 30 days post-release, as well as those already known to be under exploit. Each list is further arranged by CVE.
| Exploit detected | |
| ADV230001 | Guidance on Microsoft Signed Drivers Being Used Maliciously |
| CVE-2023-32046 | Windows MSHTML Platform Elevation of Privilege Vulnerability |
| CVE-2023-32049 | Windows SmartScreen Security Feature Bypass Vulnerability |
| CVE-2023-35311 | Microsoft Outlook Security Feature Bypass Vulnerability |
| CVE-2023-36874 | Windows Error Reporting Service Elevation of Privilege Vulnerability |
| Exploitation more likely | |
| CVE-2023-21526 | Windows Netlogon Information Disclosure Vulnerability |
| CVE-2023-33134 | Microsoft SharePoint Server Remote Code Execution Vulnerability |
| CVE-2023-33157 | Microsoft SharePoint Remote Code Execution Vulnerability |
| CVE-2023-35312 | Microsoft VOLSNAP.SYS Elevation of Privilege Vulnerability |
| CVE-2023-35352 | Windows Remote Desktop Security Feature Bypass Vulnerability |
Appendix C: Products Affected
This is a list of July’s patches sorted by product family, then sub-sorted by severity. Each list is further arranged by CVE.
Windows (102 CVEs)
| Critical severity | |
| CVE-2023-32057 | Microsoft Message Queuing Remote Code Execution Vulnerability |
| CVE-2023-35297 | Windows Pragmatic General Multicast (PGM) Remote Code Execution Vulnerability |
| CVE-2023-35315 | Windows Hyper-V Remote Code Execution Vulnerability |
| CVE-2023-35352 | Windows Remote Desktop Security Feature Bypass Vulnerability |
| CVE-2023-35365 | Windows Routing and Remote Access Service (RRAS) Remote Code Execution Vulnerability |
| CVE-2023-35366 | Windows Routing and Remote Access Service (RRAS) Remote Code Execution Vulnerability |
| CVE-2023-35367 | Windows Routing and Remote Access Service (RRAS) Remote Code Execution Vulnerability |
| Important severity | |
| CVE-2023-21526 | Windows Netlogon Information Disclosure Vulnerability |
| CVE-2023-21756 | Windows Win32k Elevation of Privilege Vulnerability |
| CVE-2023-29347 | Windows Admin Center Spoofing Vulnerability |
| CVE-2023-32033 | Microsoft Cluster Server Service Remote Code Execution Vulnerability |
| CVE-2023-32034 | Remote Procedure Call Runtime Denial of Service Vulnerability |
| CVE-2023-32035 | Remote Procedure Call Runtime Denial of Service Vulnerability |
| CVE-2023-32037 | Windows Layer 2 Tunneling Protocol (L2TP) Information Disclosure Vulnerability |
| CVE-2023-32038 | Microsoft ODBC Driver Remote Code Execution Vulnerability |
| CVE-2023-32039 | Microsoft PostScript and PCL6 Class Printer Driver Information Disclosure Vulnerability |
| CVE-2023-32040 | Microsoft PostScript and PCL6 Class Printer Driver Information Disclosure Vulnerability |
| CVE-2023-32041 | Windows Update Orchestrator Service Information Disclosure Vulnerability |
| CVE-2023-32042 | OLE Automation Information Disclosure Vulnerability |
| CVE-2023-32043 | Windows Remote Desktop Security Feature Bypass Vulnerability |
| CVE-2023-32044 | Microsoft Message Queuing Denial of Service Vulnerability |
| CVE-2023-32045 | Microsoft Message Queuing Denial of Service Vulnerability |
| CVE-2023-32046 | Windows MSHTML Platform Elevation of Privilege Vulnerability |
| CVE-2023-32047 | Paint 3D Remote Code Execution Vulnerability |
| CVE-2023-32049 | Windows SmartScreen Security Feature Bypass Vulnerability |
| CVE-2023-32050 | Windows Installer Elevation of Privilege Vulnerability |
| CVE-2023-32051 | Raw Image Extension Remote Code Execution Vulnerability |
| CVE-2023-32053 | Windows Installer Elevation of Privilege Vulnerability |
| CVE-2023-32054 | Volume Shadow Copy Elevation of Privilege Vulnerability |
| CVE-2023-32055 | Active Template Library Elevation of Privilege Vulnerability |
| CVE-2023-32056 | Windows Update Stack Elevation of Privilege Vulnerability |
| CVE-2023-32083 | Windows Failover Cluster Information Disclosure Vulnerability |
| CVE-2023-32084 | HTTP.sys Denial of Service Vulnerability |
| CVE-2023-32085 | Microsoft PostScript and PCL6 Class Printer Driver Information Disclosure Vulnerability |
| CVE-2023-33154 | Windows Partition Management Driver Elevation of Privilege Vulnerability |
| CVE-2023-33155 | Windows Cloud Files Mini Filter Driver Elevation of Privilege Vulnerability |
| CVE-2023-33163 | Windows Network Load Balancing Remote Code Execution Vulnerability |
| CVE-2023-33164 | Remote Procedure Call Runtime Denial of Service Vulnerability |
| CVE-2023-33166 | Remote Procedure Call Runtime Denial of Service Vulnerability |
| CVE-2023-33167 | Remote Procedure Call Runtime Denial of Service Vulnerability |
| CVE-2023-33168 | Remote Procedure Call Runtime Denial of Service Vulnerability |
| CVE-2023-33169 | Remote Procedure Call Runtime Denial of Service Vulnerability |
| CVE-2023-33172 | Remote Procedure Call Runtime Denial of Service Vulnerability |
| CVE-2023-33173 | Remote Procedure Call Runtime Denial of Service Vulnerability |
| CVE-2023-33174 | Windows Kernel Memory Information Disclosure Vulnerability |
| CVE-2023-35296 | Microsoft PostScript and PCL6 Class Printer Driver Information Disclosure Vulnerability |
| CVE-2023-35298 | HTTP.sys Denial of Service Vulnerability |
| CVE-2023-35299 | Windows Common Log File System Driver Elevation of Privilege Vulnerability |
| CVE-2023-35300 | Remote Procedure Call Runtime Remote Code Execution Vulnerability |
| CVE-2023-35302 | Microsoft PostScript and PCL6 Class Printer Driver Remote Code Execution Vulnerability |
| CVE-2023-35303 | USB Audio Class System Driver Remote Code Execution Vulnerability |
| CVE-2023-35304 | Windows Kernel Elevation of Privilege Vulnerability |
| CVE-2023-35305 | Windows Kernel Elevation of Privilege Vulnerability |
| CVE-2023-35306 | Microsoft PostScript and PCL6 Class Printer Driver Information Disclosure Vulnerability |
| CVE-2023-35308 | Windows MSHTML Platform Security Feature Bypass Vulnerability |
| CVE-2023-35309 | Microsoft Message Queuing Remote Code Execution Vulnerability |
| CVE-2023-35310 | Windows DNS Server Remote Code Execution Vulnerability |
| CVE-2023-35312 | Microsoft VOLSNAP.SYS Elevation of Privilege Vulnerability |
| CVE-2023-35313 | Windows Online Certificate Status Protocol (OCSP) SnapIn Remote Code Execution Vulnerability |
| CVE-2023-35314 | Remote Procedure Call Runtime Denial of Service Vulnerability |
| CVE-2023-35316 | Remote Procedure Call Runtime Information Disclosure Vulnerability |
| CVE-2023-35317 | Windows Update Stack Elevation of Privilege Vulnerability |
| CVE-2023-35318 | Remote Procedure Call Runtime Denial of Service Vulnerability |
| CVE-2023-35319 | Remote Procedure Call Runtime Denial of Service Vulnerability |
| CVE-2023-35320 | Connected User Experiences and Telemetry Elevation of Privilege Vulnerability |
| CVE-2023-35321 | Windows Deployment Services Denial of Service Vulnerability |
| CVE-2023-35322 | Windows Deployment Services Remote Code Execution Vulnerability |
| CVE-2023-35323 | Windows OLE Remote Code Execution Vulnerability |
| CVE-2023-35324 | Microsoft PostScript and PCL6 Class Printer Driver Information Disclosure Vulnerability |
| CVE-2023-35325 | Windows Print Spooler Information Disclosure Vulnerability |
| CVE-2023-35326 | Windows CDP User Components Information Disclosure Vulnerability |
| CVE-2023-35328 | Windows Transaction Manager Elevation of Privilege Vulnerability |
| CVE-2023-35329 | Windows Authentication Denial of Service Vulnerability |
| CVE-2023-35330 | Windows Extended Negotiation Denial of Service Vulnerability |
| CVE-2023-35331 | Windows Local Security Authority (LSA) Denial of Service Vulnerability |
| CVE-2023-35332 | Windows Remote Desktop Protocol Security Feature Bypass |
| CVE-2023-35336 | Windows MSHTML Platform Security Feature Bypass Vulnerability |
| CVE-2023-35337 | Win32k Elevation of Privilege Vulnerability |
| CVE-2023-35338 | Windows Peer Name Resolution Protocol Denial of Service Vulnerability |
| CVE-2023-35339 | Windows CryptoAPI Denial of Service Vulnerability |
| CVE-2023-35340 | Windows CNG Key Isolation Service Elevation of Privilege Vulnerability |
| CVE-2023-35341 | Windows Media Information Disclosure Vulnerability |
| CVE-2023-35342 | Windows Image Acquisition Elevation of Privilege Vulnerability |
| CVE-2023-35343 | Windows Geolocation Service Remote Code Execution Vulnerability |
| CVE-2023-35344 | Windows DNS Server Remote Code Execution Vulnerability |
| CVE-2023-35345 | Windows DNS Server Remote Code Execution Vulnerability |
| CVE-2023-35346 | Windows DNS Server Remote Code Execution Vulnerability |
| CVE-2023-35347 | Microsoft Store Install Service Elevation of Privilege Vulnerability |
| CVE-2023-35348 | Azure Active Directory Security Feature Bypass Vulnerability (shared with Azure) |
| CVE-2023-35350 | Windows Active Directory Certificate Services (AD CS) Remote Code Execution Vulnerability |
| CVE-2023-35351 | Windows Active Directory Certificate Services (AD CS) Remote Code Execution Vulnerability |
| CVE-2023-35353 | Connected User Experiences and Telemetry Elevation of Privilege Vulnerability |
| CVE-2023-35355 | Windows Cloud Files Mini Filter Driver Elevation of Privilege Vulnerability |
| CVE-2023-35356 | Windows Kernel Elevation of Privilege Vulnerability |
| CVE-2023-35357 | Windows Kernel Elevation of Privilege Vulnerability |
| CVE-2023-35358 | Windows Kernel Elevation of Privilege Vulnerability |
| CVE-2023-35360 | Windows Kernel Elevation of Privilege Vulnerability |
| CVE-2023-35361 | Windows Kernel Elevation of Privilege Vulnerability |
| CVE-2023-35362 | Windows Clip Service Elevation of Privilege Vulnerability |
| CVE-2023-35363 | Windows Kernel Elevation of Privilege Vulnerability |
| CVE-2023-35364 | Windows Kernel Elevation of Privilege Vulnerability |
| CVE-2023-35374 | Paint 3D Remote Code Execution Vulnerability |
| CVE-2023-36871 | Azure Active Directory Security Feature Bypass Vulnerability (shared with Azure) |
| CVE-2023-36874 | Windows Error Reporting Service Elevation of Privilege Vulnerability |
Office (10 CVEs)
| Important severity | |
| CVE-2023-33148 | Microsoft Office Elevation of Privilege Vulnerability |
| CVE-2023-33149 | Microsoft Office Graphics Remote Code Execution Vulnerability |
| CVE-2023-33150 | Microsoft Office Security Feature Bypass Vulnerability |
| CVE-2023-33151 | Microsoft Outlook Spoofing Vulnerability (shared with Outlook) |
| CVE-2023-33152 | Microsoft Access Remote Code Execution Vulnerability (shared with Access) |
| CVE-2023-33153 | Microsoft Outlook Remote Code Execution Vulnerability (shared with Outlook) |
| CVE-2023-33158 | Microsoft Excel Remote Code Execution Vulnerability |
| CVE-2023-33161 | Microsoft Excel Remote Code Execution Vulnerability |
| CVE-2023-33162 | Microsoft Excel Information Disclosure Vulnerability |
| CVE-2023-35311 | Microsoft Outlook Security Feature Bypass Vulnerability (shared with Outlook) |
SharePoint (5 CVEs)
| Important severity | |
| CVE-2023-33157 | Microsoft SharePoint Remote Code Execution Vulnerability |
| CVE-2023-33160 | Microsoft SharePoint Server Remote Code Execution Vulnerability |
| CVE-2023-33134 | Microsoft SharePoint Server Remote Code Execution Vulnerability |
| CVE-2023-33159 | Microsoft SharePoint Server Spoofing Vulnerability |
| CVE-2023-33165 | Microsoft SharePoint Server Security Feature Bypass Vulnerability |
Azure (3 CVEs)
| Important severity | |
| CVE-2023-36868 | Service Fabric on Windows Information Disclosure Vulnerability |
| CVE-2023-35348 | Azure Active Directory Security Feature Bypass Vulnerability (shared with Windows) |
| CVE-2023-36871 | Azure Active Directory Security Feature Bypass Vulnerability (shared with Windows) |
Outlook (3 CVEs)
| Important severity | |
| CVE-2023-33151 | Microsoft Outlook Spoofing Vulnerability (shared with Office) |
| CVE-2023-33153 | Microsoft Outlook Remote Code Execution Vulnerability (shared with Office) |
| CVE-2023-35311 | Microsoft Outlook Security Feature Bypass Vulnerability (shared with Office) |
.Net (2 CVEs)
| Important severity | |
| CVE-2023-33170 | ASP.NET Core Security Feature Bypass Vulnerability |
| CVE-2023-33127 | .NET and Visual Studio Elevation of Privilege Vulnerability (shared with Visual Studio) |
Dynamics 365 (2 CVEs)
| Important severity | |
| CVE-2023-32052 | Microsoft Power Apps Spoofing Vulnerability |
| CVE-2023-33171 | Microsoft Dynamics 365 (on-premises) Cross-site Scripting Vulnerability |
Visual Studio (2 CVEs)
| Important severity | |
| CVE-2023-33127 | .NET and Visual Studio Elevation of Privilege Vulnerability (shared with .NET) |
| CVE-2023-36867
| Visual Studio Code GitHub Pull Requests and Issues Extension Remote Code Execution Vulnerability |
Access (1 CVE)
| Important severity | |
| CVE-2023-33152 | Microsoft Access Remote Code Execution Vulnerability (shared with Office) |
common_utils.py (1 CVE)
| Important severity | |
| CVE-2023-35333 | Media-Wiki Extensions Remote Code Execution Vulnerability |
Defender (1 CVE)
| Important severity | |
| CVE-2023-33156 | Microsoft Defender Elevation of Privilege Vulnerability |
Mono (1 CVE)
| Important severity | |
| CVE-2023-35373 | Mono Authenticode Validation Elevation of Privilege Vulnerability |
VP9 Video Extensions (1 CVE)
| Important severity | |
| CVE-2023-36872 | VP9 Video Extensions Information Disclosure Vulnerability |