Ragnar Locker ransomware group taken down
Even though it had a long run for a ransomware group, it seems the bell might be tolling for Ragnar Locker. On October 19, 2023, the group’s leak site was seized by an international group of law enforcement agencies.

The take down action was carried out between 16 and 20 October. During the action searches were conducted in Czechia, Spain and Latvia. The main target, suspected of being a developer of the Ragnar group, has been brought in front of the examining magistrates of the Paris Judicial Court.
The action was coordinated at international level by Europol and Eurojust. The ransomware group’s infrastructure was also seized in the Netherlands, Germany and Sweden and the associated data leak website was taken down in Sweden.
Ragnar Locker started its operations at the end of 2019, making it unusually long lived. Most ransomware groups do not survive that long, mostly due to internal struggles or a takedown such as this one.
Based on known attacks, as shown in out monthly ransomware reviews, Ragnar Locker was number 15 on the list of the most active ransomware groups over the last twelve months. (A known attack is one where a victim’s details are posted on a ransomware group’s leak website becasue they didn’t pay a ransom. The number of known attacks probably represents 50%-75% of the total attacks.)
Known attacks by Ragnar Locker, October 2022 – September 2023
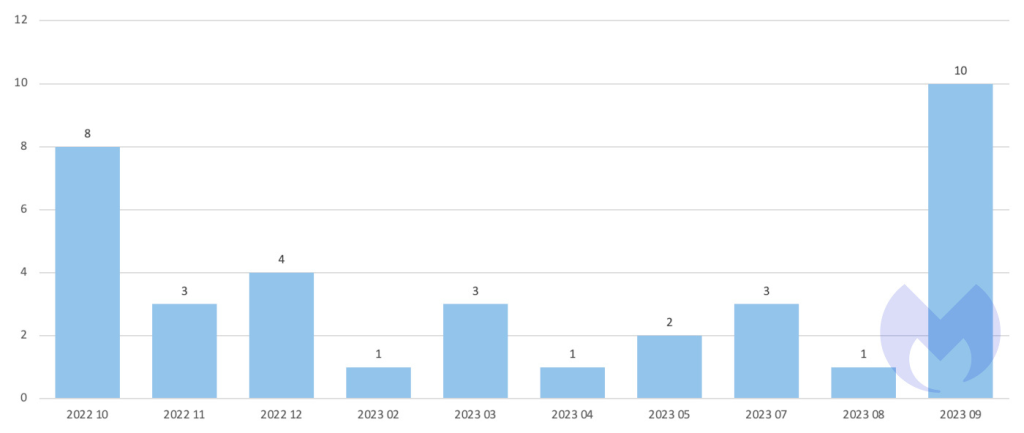
Ragnar Locker has been called out for specifically targeting the energy sector—after attacks on Energias de Portugal (EDP) and Greek gas operator DESFA—but at Malwarebytes we never noticed any specialization. In the chart below, you can see it that across 36 known attacks in the last 12 months it attacked 15 different sectors.
Ragnar Locker’s known attacks by industry sector, October 2022 – September 2023

In 2022, the FBI published a flash alert to warn that the Ragnar Locker ransomware gang had breached the networks of at least 52 organizations across 10 critical infrastructure sectors.
One of the biggest upsets occurred when Ragnar Locker published information it had stolen from police computers in Zwijndrecht, a municipality in the province of Antwerp, Belgium) The stolen information included police records about license plates, speeding tickets, and at least one case of child abuse. Other high profile victims include Campari and Capcom.
Ragnar Locker is not a Ransomware-as-a-Service (RaaS) that was constantly advertising for new affiliates, so we assume it worked with a pretty constant group of people. It also seemed capable of developing new attack methods, like the ESXi encryptor that was recently deployed by the Dark Angels group in an attack on Industrial giant Johnson Controls.
Ragnar Locker specifically targeted software commonly used by managed service providers (MSPs) to prevent its attacks from being detected and stopped. It also used the double extortion method of encryption and data theft pretty much from the start
The questionable honor of being the last victim posted on the leak site was IP international presence on October 6, 2023. There is always the chance that some victims are now left without an option to negotiate with the ransomware group.
How to avoid ransomware
- Block common forms of entry. Create a plan for patching vulnerabilities in internet-facing systems quickly; and disable or harden remote access like RDP and VPNs.
- Prevent intrusions. Stop threats early before they can even infiltrate or infect your endpoints. Use endpoint security software that can prevent exploits and malware used to deliver ransomware.
- Detect intrusions. Make it harder for intruders to operate inside your organization by segmenting networks and assigning access rights prudently. Use EDR or MDR to detect unusual activity before an attack occurs.
- Stop malicious encryption. Deploy Endpoint Detection and Response software like Malwarebytes EDR that uses multiple different detection techniques to identify ransomware, and ransomware rollback to restore damaged system files.
- Create offsite, offline backups. Keep backups offsite and offline, beyond the reach of attackers. Test them regularly to make sure you can restore essential business functions swiftly.
- Don’t get attacked twice. Once you’ve isolated the outbreak and stopped the first attack, you must remove every trace of the attackers, their malware, their tools, and their methods of entry, to avoid being attacked again.
Malwarebytes EDR and MDR removes all remnants of ransomware and prevents you from getting reinfected. Want to learn more about how we can help protect your business? Get a free trial below.