Who Wrote the ALPHV/BlackCat Ransomware Strain?

Credit to Author: BrianKrebs| Date: Fri, 28 Jan 2022 13:18:36 +0000
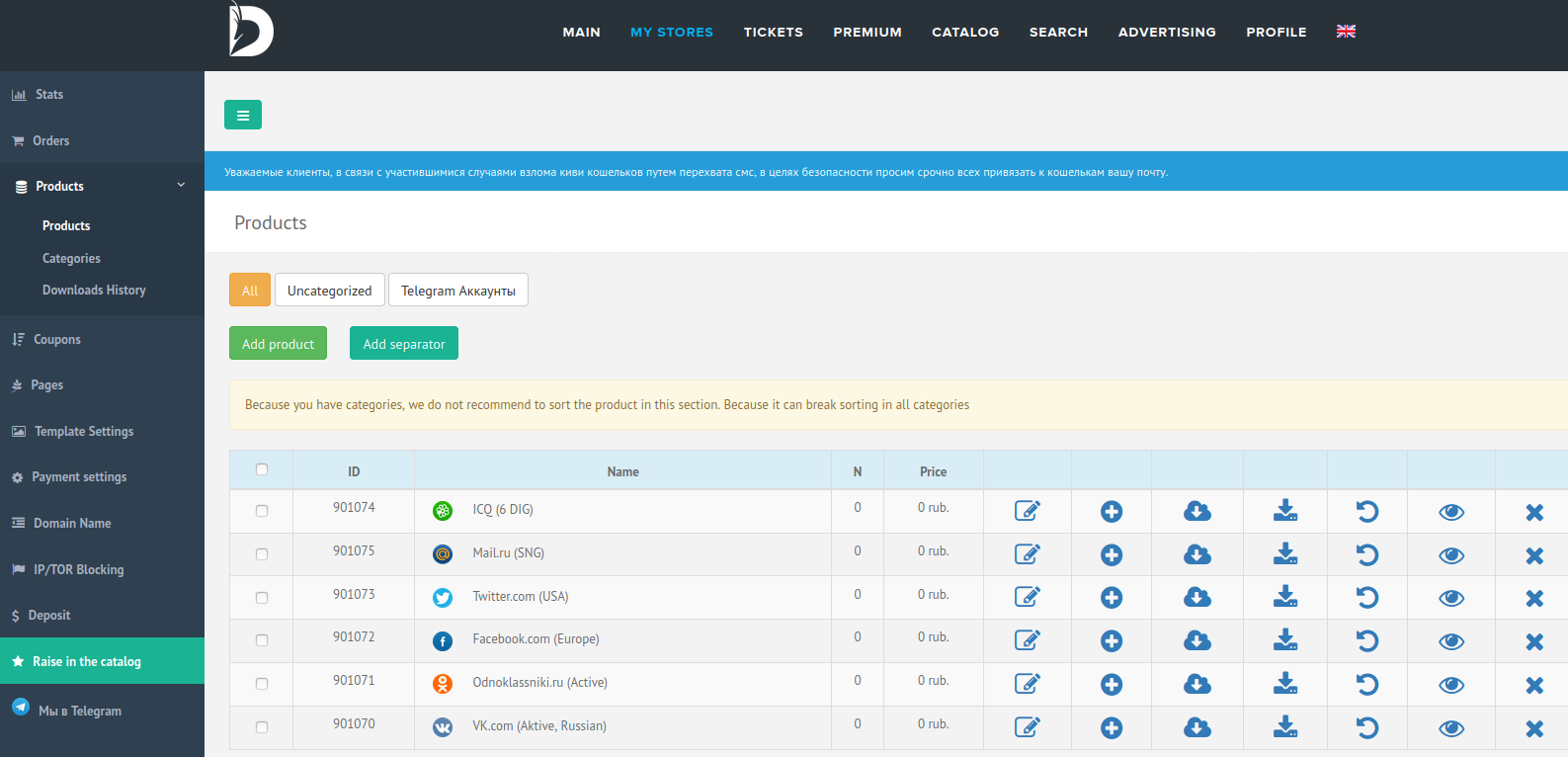
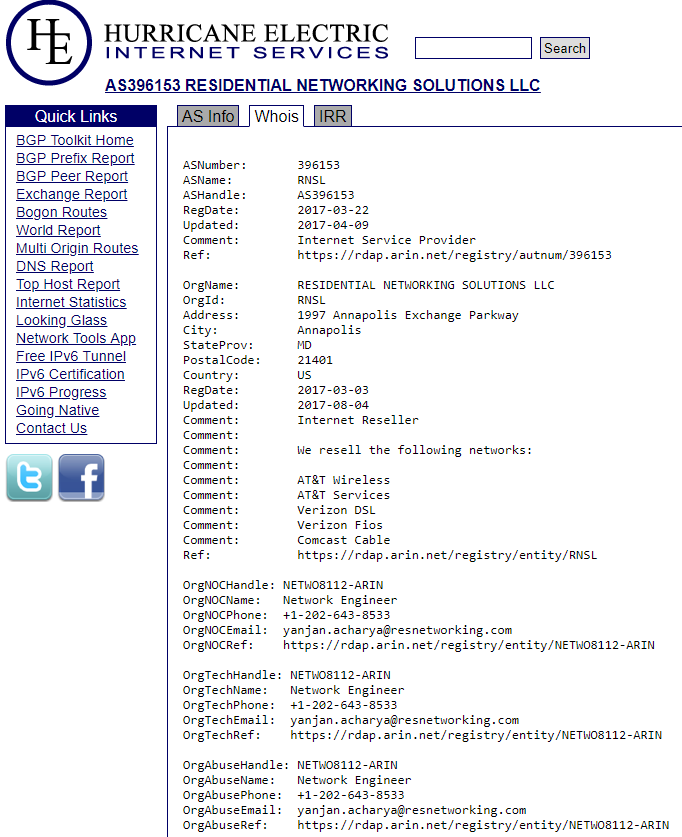
In December 2021, researchers discovered a new ransomware-as-a-service named ALPHV (a.k.a. “BlackCat”), considered to be the first professional cybercrime group to create and use a ransomware strain in the Rust programming language. In this post, we’ll explore some of the clues left behind by the developer who was reputedly hired to code the ransomware variant.
Read more