Secure hybrid and remote workplaces with a Zero Trust approach
Credit to Author: Christine Barrett| Date: Thu, 06 Apr 2023 16:00:00 +0000
Productivity and innovation have become critical goals in many hybrid and remote work environments. Ensuring preventative and strong security, in turn, must be at the heart of that. In this blog series, we’ll discuss two Zero Trust business scenarios: enabling a more productive hybrid or remote work environment and rapidly modernizing your organization’s security posture through a Zero Trust architecture. Adopting an end-to-end Zero Trust strategy promotes secure, optimal access for the modern hybrid workforce.
Zero Trust is a proactive, integrated approach to security across the digital estate that explicitly and continuously verifies every transaction, asserts least privilege access, and relies on intelligence, advanced detection, and real-time response in the face of threats.
Adopting an end-to-end Zero Trust security strategy, and implementing Zero Trust security pillars, promotes the most secure and optimized access for users in the modern hybrid workforce. Organizations need to adapt to stay competitive, and cybersecurity remains a top concern as work environments continue to shift toward hybrid and remote settings.
Enable a more productive hybrid or remote workplace
Hybrid work introduces significant challenges for security teams as employees spend more time outside the traditional network perimeter where visibility, control, and consistency are harder to enforce. This impacts security teams who work to secure sensitive data and devices.
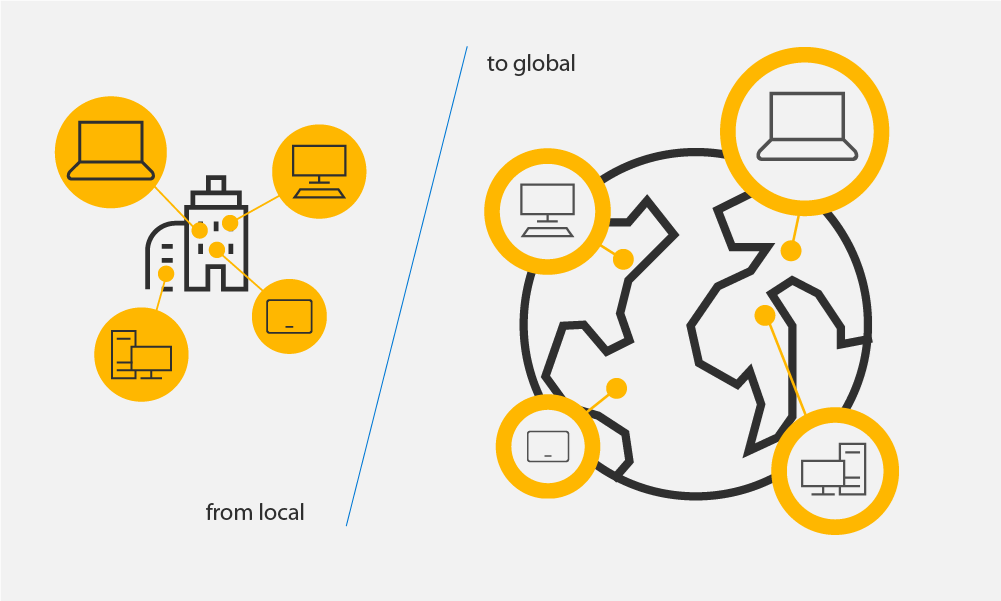
Figure 1. Hybrid and remote workers can enable more productive, secure workflows in both global and local locations with a comprehensive Zero Trust strategy in place.
Embracing a Zero Trust security model provides your organization with the necessary tools and framework to more effectively secure hybrid work environments. Adopting an end-to-end Zero Trust strategy also comes with several other business benefits in this new world of work, including:
- Improved employee experience and productivity.
- Increased organizational agility and adaptability.
- Strengthened talent retention.
One of the first steps organizations must take to modernize and equip themselves with proper data security measures is to determine if they:
- Know the types of sensitive information they have and where it lives.
- Protect and prevent loss of sensitive data across environments.
- Have a method for managing insider risks to understand user intent.
Answering these questions can help organizations discern how well they match up to today’s evolving security risks and how they could improve their security posture by implementing a Zero Trust architecture.
A Zero Trust framework helps organizations strengthen their defenses, giving employees the flexibility to work from anywhere and use applications that live outside of traditional corporate network protections. Zero Trust makes securing data across multiple channels, such as emails, messages, shared storage, cloud apps, and devices much easier. And, with hybrid workforces, data security incidents can happen anytime, anywhere.
A simplified security architecture through Zero Trust improves business agility across many types of workplaces, including hybrid. Through efficient system management and user access, organizations can move quickly to pursue business opportunities and support remote work while assessing and managing risk. This is particularly important since collaborating across multiple environments and devices due to remote and hybrid work can result in severe data security incidents, especially if your organization does not have visibility into its data or if a user has malicious intent to exfiltrate the data or share sensitive information and make it visible. Instituting Zero Trust architecture also improves security posture and reduces the risk of data breaches, even for people, resources, and data outside the corporate network perimeter.

Figure 2. Teams must collaborate with each other to implement a comprehensive, cross-cloud Zero Trust framework into their security practices.
Innovate and rapidly modernize your organization’s security posture
Zero Trust is designed to modernize your security posture and ensure comprehensive security across all identities. A comprehensive Zero Trust approach also helps break down siloes between IT teams and systems, enabling better visibility and protection across your entire IT stack. Using tools like Microsoft Purview Compliance Manager, your security team can also measure the security posture of your assets against industry benchmarks and best practices. Analyzing productivity and security signals helps your team better evaluate your security culture, identifying areas for improvement or best practices for compliance.
Today’s security leaders must balance the challenges of hybrid or remote access, protecting sensitive data, and compliance requirements with the business need to collaborate, innovate, and grow. Rapidly modernizing your security posture by implementing a Zero Trust framework will not only help your organization to meet and exceed regulatory and compliance requirements, but it will also help enable your organization to protect against a fast-changing threat landscape. As your organization begins this journey, remember that teams must:
- Collaborate on how to address the most critical threats they face.
- This involves continuous improvement and evaluation across the entire digital estate to increase visibility. Teams can automate tasks that slow down team efforts, such as implementing IT help desk support, which saves teams time and money to use for proactively addressing serious security problems.
- Simultaneously defend their organizations against attacks and other security threats.
- As a part of defending against security attacks and threats, security teams should ask themselves how they protect data and identities, while also evaluating and managing endpoint device health. This can help teams evaluate attacks that may occur while determining insider risk alongside user behavior analysis.
- Strive for continuous security improvement.
- Because of the ever-evolving threat landscape, security teams must also continuously improve and check in on their security status, including continuous monitoring for threats that otherwise would not or could not be detected proactively. Zero Trust allows teams to protect against bad actors and potential security threats automatically and proactively through multistep defense across identities and endpoints.
- Prioritize their need for end-to-end visibility.
- Another component of defending against security attacks and threats is increasing the security team’s visibility throughout the entire digital estate. Organizations should adopt specific policies to ensure data and identities are protected and meet compliance requirements, as necessary, and set alerts for attacks to enable quick remediation.
Consider the Rapid Modernization Plan guidance Microsoft uses to implement Zero Trust, which allows teams to use a set of specified initiatives for successful and quick deployment. The process goes as follows:
- Validate trust for all access requests from identities, endpoints, apps, and networks.
- Prepare and enable ransomware recovery.
- Protect on-premises and cloud data from malicious access.
- Streamline threat response.
- Unify visibility across all security pillars.
- Reduce manual effort on security teams.
Adopting a Zero Trust model enables end-to-end visibility across the security estate. The automated response that the Zero Trust approach takes protects assets, remediates threats, and supports investigations, ultimately empowering security teams to respond more quickly to threats across all pillars.
Secure your organization’s digital estate through a comprehensive Zero Trust approach
Adopting an end-to-end Zero Trust strategy is a critical step that organizations can take to increase productivity in, innovate, and modernize their hybrid work environments. We look forward to diving into additional scenarios in our next Zero Trust blog.
To learn more about protecting your business:
- Get started with our Zero Trust assessment tool.
- 5 reasons to adopt a Zero Trust security strategy for your business.
- Securely work from anywhere.
- Safeguard your most critical assets.
- Meet regulatory and compliance requirements.
- Minimize the impact of internal or external bad actors.
- Rapidly modernize your security posture.
And, to dive deeper into Microsoft Security solutions, join us on April 13, 2023, for Microsoft Secure Technical Accelerator. During this event, you can engage with our product and engineering teams through a live Q&A during each session, learn best practices, build community with your security peers, and get prescriptive technical guidance that will help you and your organization implement our comprehensive security solutions.
To learn more about Microsoft Security solutions, visit our website. Bookmark the Security blog to keep up with our expert coverage on security matters. Also, follow us on LinkedIn (Microsoft Security) and Twitter (@MSFTSecurity) for the latest news and updates on cybersecurity.
The post Secure hybrid and remote workplaces with a Zero Trust approach appeared first on Microsoft Security Blog.