February’s Patch Tuesday treats customers to 72 patches
Credit to Author: Angela Gunn| Date: Wed, 14 Feb 2024 09:23:10 +0000
After a light start to the year, February delivered 72 patches and 21 advisories to Microsoft customers. The CVEs addressed in this month’s Patch Tuesday release included 43 for Windows. Twelve other product groups or tools are also affected. Of the CVEs addressed, five are considered Critical in severity by Microsoft; these affect Windows, Office, Exchange, and Dynamics 365.
At patch time, two of the issues are known to be under exploit in the wild, and none has been publicly disclosed. (However, one of the advisory items most certainly has; more on that in a minute.) Eight of the addressed vulnerabilities in Windows, Office, and Exchange (including a Critical-severity elevation-of-privilege issue with an attention-getting 9.8 CVSS base score) are by the company’s estimation more likely to be exploited in the next 30 days. Six of the issues addressed are covered by Sophos protections, and we include information on those in a table below.
In addition to these patches the release included information on six Chromium/Edge-related CVEs, including an RCE that could lead to sandbox escapes; one MITRE-issued CVE concerning a DNS issue that could lead to denial of service; one Github-issued CVE addressing the recent CVE-2024-21626 “Leaky Vessel” issue affecting Mariner, disclosed in a lengthy public post by Snyk two weeks ago and patched by various other affected companies since then; and 13 Adobe advisories, all related to Acrobat Reader.
We don’t include advisories in the CVE counts and graphics below, but we provide information on everything in an appendix at the end of the article. We are as usual including at the end of this post three other appendices listing all Microsoft’s patches, sorted by severity, by predicted exploitability, and by product family.
- Total Microsoft CVEs: 72
- Total Adobe advisories covered in update: 13
- Total Edge / Chromium issues covered in update: 6
- Total Mariner advisories covered in update: 1
- Total MITRE advisories covered in update: 1
- Publicly disclosed: 0
- Exploited: 2
- Severity
- Critical: 5
- Important: 65
- Moderate: 2
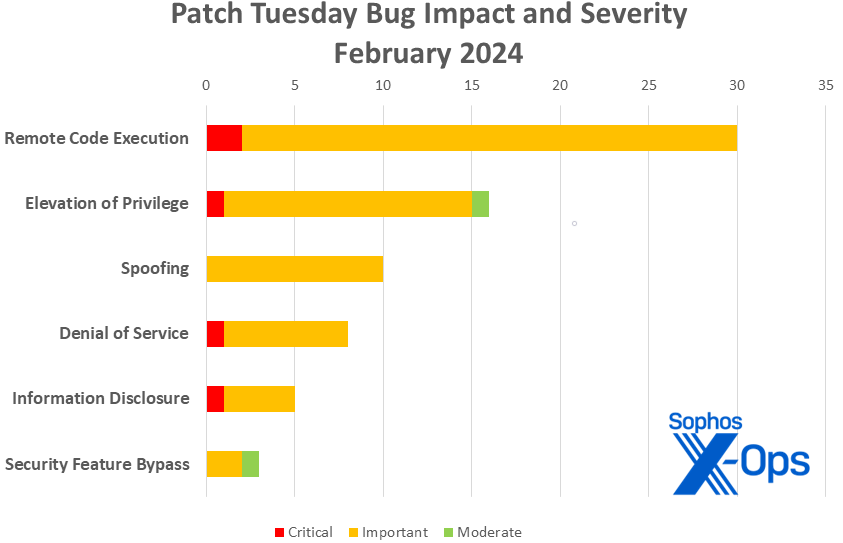
- Impact
- Remote Code Execution: 30
- Elevation of Privilege: 16
- Spoofing: 10
- Denial of Service: 8
- Information Disclosure: 5
- Security Feature Bypass: 3
Figure 1: After January’s big month for information disclosure bugs, a wealth of OLE-related fixes put remote code execution back on top for February
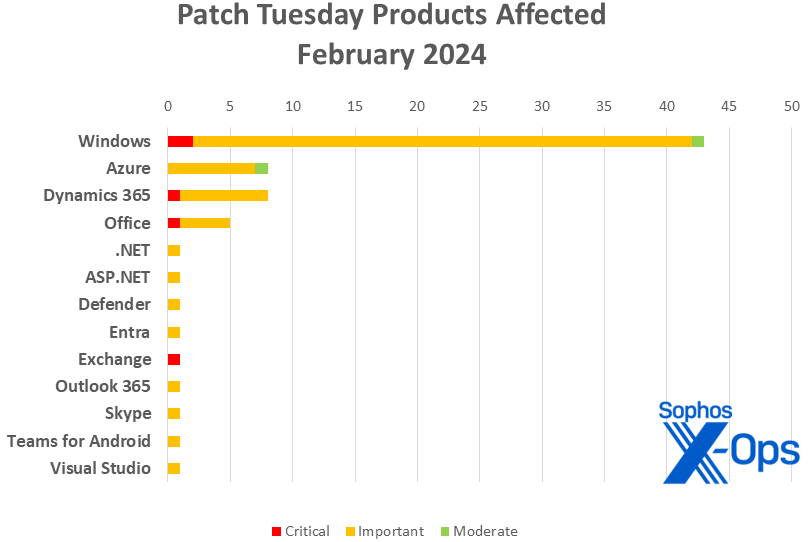
Products
- Windows: 43
- Azure: 8
- Dynamics 365: 8
- Office: 5
- .NET: 1
- ASP.NET: 1 (shared with Visual Studio)
- Defender: 1
- Entra [Azure AD]: 1
- Exchange: 1
- Outlook 365: 1
- Skype: 1
- Teams for Android: 1
- Visual Studio: 1 (shared with ASP.NET)
Figure 2: It’s a Windows-heavy month, thanks in part to a large number of fixes for Windows Defender Application Control (WDAC)
Notable February updates
In addition to the issues discussed above, a few specific items are worth noting.
CVE-2024-21350, CVE-2024-21352, CVE-2024-21358, CVE-2024-21359, CVE-2024-21360, CVE-2024-21361, CVE-2024-21365, CVE-2024-21366, CVE-2024-21367, CVE-2024-21368, CVE-2024-21369, CVE-2024-21370, CVE-2024-21375, CVE-2024-21391 (15 CVEs)
Microsoft WDAC OLE DB provider for SQL Server Remote Code Execution Vulnerability
Fifteen CVEs that share not only a name but a severity (Important), an impact (RCE), a lofty CVSS base score (8.8), and a finder non-identification (Microsoft credits all 15 to “Anonymous”). They’re accompanied by one additional (but related?) patch that shares everything but the number and name – CVE-2024-21353, Microsoft WDAC ODBC Driver Remote Code Execution Vulnerability.
CVE-2024-21404
Microsoft Entra Jira Single-Sign-On Plugin Elevation of Privilege Vulnerability
This extra-spicy EoP – Microsoft assigns it only an Important severity rating, but its base CVSS is a critical-level 9.8 – targets the Azure AD Jira SSO plugin. Significantly, it doesn’t even require the attacker to authenticate to cause trouble; all it takes is a script to access a targeted Jira server, and the attacker will be able to update Entra ID SAML metadata and information for the plugin – allowing them to change the authentication of the application as they wish. The fix is an update to version 1.1.2; it’s available from either the Microsoft Download Center or from the Atlassian Marketplace.
CVE-2024-21410
Microsoft Exchange Server Elevation of Privilege Vulnerability
The other CVE with a 9.8 CVSS this month is a NTLM relay (pass-the-hash) vulnerability. It could allow the attacker to relay a user’s leaked Net-NTLMv2 hash against a vulnerable Exchange Server and authenticate as the user. It affects a hodge-podge of versions: Exchange Server 2016, cumulative update 23; Exchange Server 2019, cumulative update 13; and Exchange Server 2019, cumulative update 14. More information is available on Microsoft’s Exchange Team Blog, but know that the company believes this one is more likely to be exploited within the next 30 days.
CVE-2024-21378
Microsoft Outlook Remote Code Execution Vulnerability
Preview Pane is an attack vector for this important-severity RCE, and Microsoft believes that exploitation is more likely in the next 30 days. The race is on.
CVE-2024-21374
Microsoft Teams for Android Information Disclosure
The patch for this important-severity information disclosure issue is available via Google Play.
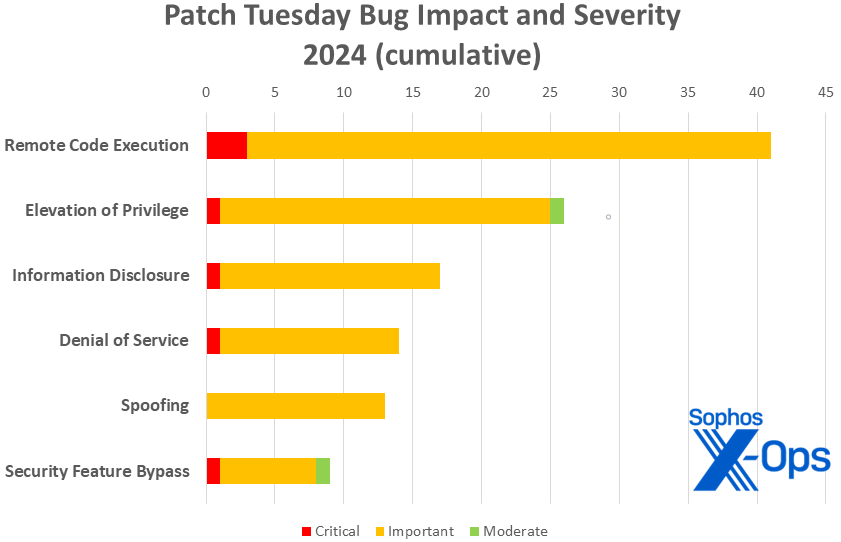
Figure 3: 2024’s off and trotting – though, with just 120 patches so far, totals are running substantially behind other years. (The first two months of 2023 brought 173 patches; 2022, 154; 2021, 139; and 2020, 150.)
Sophos protections
As you can every month, if you don’t want to wait for your system to pull down Microsoft’s updates itself, you can download them manually from the Windows Update Catalog website. Run the winver.exe tool to determine which build of Windows 10 or 11 you’re running, then download the Cumulative Update package for your specific system’s architecture and build number.
Appendix A: Vulnerability Impact and Severity
This is a list of February patches sorted by impact, then sub-sorted by severity. Each list is further arranged by CVE.
Remote Code Execution (30 CVEs)
| Critical severity | |
| CVE-2024-21357 | Windows Pragmatic General Multicast (PGM) Remote Code Execution Vulnerability |
| CVE-2024-21413 | Microsoft Office Remote Code Execution Vulnerability |
| Important severity | |
| CVE-2024-20667 | Azure DevOps Server Remote Code Execution Vulnerability |
| CVE-2024-20673 | Microsoft Office Remote Code Execution Vulnerability |
| CVE-2024-21339 | Windows USB Generic Parent Driver Remote Code Execution Vulnerability |
| CVE-2024-21341 | Windows Kernel Remote Code Execution Vulnerability |
| CVE-2024-21347 | Microsoft ODBC Driver Remote Code Execution Vulnerability |
| CVE-2024-21349 | Microsoft ActiveX Data Objects Remote Code Execution Vulnerability |
| CVE-2024-21350 | Microsoft WDAC OLE DB provider for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-21352 | Microsoft WDAC OLE DB provider for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-21353 | Microsoft WDAC ODBC Driver Remote Code Execution Vulnerability |
| CVE-2024-21358 | Microsoft WDAC OLE DB provider for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-21359 | Microsoft WDAC OLE DB provider for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-21360 | Microsoft WDAC OLE DB provider for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-21361 | Microsoft WDAC OLE DB provider for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-21363 | Microsoft Message Queuing (MSMQ) Remote Code Execution Vulnerability |
| CVE-2024-21365 | Microsoft WDAC OLE DB provider for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-21366 | Microsoft WDAC OLE DB provider for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-21367 | Microsoft WDAC OLE DB provider for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-21368 | Microsoft WDAC OLE DB provider for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-21369 | Microsoft WDAC OLE DB provider for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-21370 | Microsoft WDAC OLE DB provider for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-21372 | Windows OLE Remote Code Execution Vulnerability |
| CVE-2024-21375 | Microsoft WDAC OLE DB provider for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-21376 | Microsoft Azure Kubernetes Service Confidential Container Remote Code Execution Vulnerability |
| CVE-2024-21378 | Microsoft Outlook Remote Code Execution Vulnerability |
| CVE-2024-21379 | Microsoft Word Remote Code Execution Vulnerability |
| CVE-2024-21384 | Microsoft Office OneNote Remote Code Execution Vulnerability |
| CVE-2024-21391 | Microsoft WDAC OLE DB provider for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-21420 | Microsoft WDAC OLE DB provider for SQL Server Remote Code Execution Vulnerability |
Elevation of Privilege (16 CVEs)
| Critical severity | |
| CVE-2024-21410 | Microsoft Exchange Server Elevation of Privilege Vulnerability |
| Important severity | |
| CVE-2024-21304 | Trusted Compute Base Elevation of Privilege Vulnerability |
| CVE-2024-21315 | Microsoft Defender for Endpoint Protection Elevation of Privilege Vulnerability |
| CVE-2024-21329 | Azure Connected Machine Agent Elevation of Privilege Vulnerability |
| CVE-2024-21338 | Windows Kernel Elevation of Privilege Vulnerability |
| CVE-2024-21345 | Windows Kernel Elevation of Privilege Vulnerability |
| CVE-2024-21346 | Win32k Elevation of Privilege Vulnerability |
| CVE-2024-21354 | Microsoft Message Queuing (MSMQ) Elevation of Privilege Vulnerability |
| CVE-2024-21355 | Microsoft Message Queuing (MSMQ) Elevation of Privilege Vulnerability |
| CVE-2024-21371 | Windows Kernel Elevation of Privilege Vulnerability |
| CVE-2024-21397 | Microsoft Azure File Sync Elevation of Privilege Vulnerability |
| CVE-2024-21401 | Microsoft Entra Jira Single-Sign-On Plugin Elevation of Privilege Vulnerability |
| CVE-2024-21402 | Microsoft Outlook Elevation of Privilege Vulnerability |
| CVE-2024-21403 | Microsoft Azure Kubernetes Services Confidential Container Elevation of Privilege Vulnerability |
| CVE-2024-21405 | Microsoft Message Queuing (MSMQ) Elevation of Privilege Vulnerability |
| Moderate severity | |
| CVE-2024-21364 | Microsoft Azure Site Recovery Elevation of Privilege Vulnerability |
Spoofing (10 CVEs)
| Important severity | |
| CVE-2024-20679 | Azure Stack Hub Spoofing Vulnerability |
| CVE-2024-21327 | Microsoft Dynamics 365 Customer Engagement Cross-Site Scripting Vulnerability |
| CVE-2024-21328 | Dynamics 365 Sales Spoofing Vulnerability |
| CVE-2024-21381 | Microsoft Azure Active Directory B2C Spoofing Vulnerability |
| CVE-2024-21389 | Microsoft Dynamics 365 (on-premises) Cross-site Scripting Vulnerability |
| CVE-2024-21393 | Microsoft Dynamics 365 (on-premises) Cross-site Scripting Vulnerability |
| CVE-2024-21394 | Dynamics 365 Field Service Spoofing Vulnerability |
| CVE-2024-21395 | Microsoft Dynamics 365 (on-premises) Cross-site Scripting Vulnerability |
| CVE-2024-21396 | Dynamics 365 Sales Spoofing Vulnerability |
| CVE-2024-21406 | Windows Print Spooler Spoofing Vulnerability |
Denial of Service (8 CVEs)
| Critical severity | |
| CVE-2024-20684 | Windows Hyper-V Denial of Service Vulnerability |
| Important severity | |
| CVE-2024-21342 | Windows DNS Client Denial of Service Vulnerability |
| CVE-2024-21343 | Windows Network Address Translation (NAT) Denial of Service Vulnerability |
| CVE-2024-21344 | Windows Network Address Translation (NAT) Denial of Service Vulnerability |
| CVE-2024-21348 | Internet Connection Sharing (ICS) Denial of Service Vulnerability |
| CVE-2024-21356 | Windows Lightweight Directory Access Protocol (LDAP) Denial of Service Vulnerability |
| CVE-2024-21386 | .NET Denial of Service Vulnerability |
| CVE-2024-21404 | .NET Denial of Service Vulnerability |
Information Disclosure (5 CVEs)
| Critical severity | |
| CVE-2024-21380 | Microsoft Dynamics Business Central/NAV Information Disclosure Vulnerability |
| Important severity | |
| CVE-2024-20695 | Skype for Business Information Disclosure Vulnerability |
| CVE-2024-21340 | Windows Kernel Information Disclosure Vulnerability |
| CVE-2024-21374 | Microsoft Teams for Android Information Disclosure Vulnerability |
| CVE-2024-21377 | Windows DNS Information Disclosure Vulnerability |
Security Feature Bypass (3 CVEs)
| Important severity | |
| CVE-2024-21362 | Windows Kernel Security Feature Bypass Vulnerability |
| CVE-2024-21412 | Internet Shortcut Files Security Feature Bypass Vulnerability |
| Moderate Severity | |
| CVE-2024-21351 | Windows SmartScreen Security Feature Bypass Vulnerability |
Appendix B: Exploitability
This is a list of the February CVEs judged by Microsoft to be either already under active exploit in the wild or more likely to be exploited in the wild within the first 30 days post-release. Each list is further arranged by CVE.
| Exploitation detected | |
| CVE-2024-21351 | Windows SmartScreen Security Feature Bypass Vulnerability |
| CVE-2024-21412 | Internet Shortcut Files Security Feature Bypass Vulnerability |
| Exploitation more likely within the next 30 days | |
| CVE-2024-21338 | Windows Kernel Elevation of Privilege Vulnerability |
| CVE-2024-21345 | Windows Kernel Elevation of Privilege Vulnerability |
| CVE-2024-21346 | Win32k Elevation of Privilege Vulnerability |
| CVE-2024-21357 | Windows Pragmatic General Multicast (PGM) Remote Code Execution Vulnerability |
| CVE-2024-21371 | Windows Kernel Elevation of Privilege Vulnerability |
| CVE-2024-21378 | Microsoft Outlook Remote Code Execution Vulnerability |
| CVE-2024-21379 | Microsoft Word Remote Code Execution Vulnerability |
| CVE-2024-21410 | Microsoft Exchange Server Elevation of Privilege Vulnerability |
Appendix C: Products Affected
This is a list of February’s patches sorted by product family, then sub-sorted by severity. Each list is further arranged by CVE. Patches that are shared among multiple product families are listed multiple times, once for each product family.
Windows (43 CVEs)
| Critical severity | |
| CVE-2024-20684 | Windows Hyper-V Denial of Service Vulnerability |
| CVE-2024-21357 | Windows Pragmatic General Multicast (PGM) Remote Code Execution Vulnerability |
| Important severity | |
| CVE-2024-21304 | Trusted Compute Base Elevation of Privilege Vulnerability |
| CVE-2024-21338 | Windows Kernel Elevation of Privilege Vulnerability |
| CVE-2024-21339 | Windows USB Generic Parent Driver Remote Code Execution Vulnerability |
| CVE-2024-21340 | Windows Kernel Information Disclosure Vulnerability |
| CVE-2024-21341 | Windows Kernel Remote Code Execution Vulnerability |
| CVE-2024-21342 | Windows DNS Client Denial of Service Vulnerability |
| CVE-2024-21343 | Windows Network Address Translation (NAT) Denial of Service Vulnerability |
| CVE-2024-21344 | Windows Network Address Translation (NAT) Denial of Service Vulnerability |
| CVE-2024-21345 | Windows Kernel Elevation of Privilege Vulnerability |
| CVE-2024-21346 | Win32k Elevation of Privilege Vulnerability |
| CVE-2024-21347 | Microsoft ODBC Driver Remote Code Execution Vulnerability |
| CVE-2024-21348 | Internet Connection Sharing (ICS) Denial of Service Vulnerability |
| CVE-2024-21349 | Microsoft ActiveX Data Objects Remote Code Execution Vulnerability |
| CVE-2024-21350 | Microsoft WDAC OLE DB provider for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-21352 | Microsoft WDAC OLE DB provider for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-21353 | Microsoft WDAC ODBC Driver Remote Code Execution Vulnerability |
| CVE-2024-21354 | Microsoft Message Queuing (MSMQ) Elevation of Privilege Vulnerability |
| CVE-2024-21355 | Microsoft Message Queuing (MSMQ) Elevation of Privilege Vulnerability |
| CVE-2024-21356 | Windows Lightweight Directory Access Protocol (LDAP) Denial of Service Vulnerability |
| CVE-2024-21358 | Microsoft WDAC OLE DB provider for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-21359 | Microsoft WDAC OLE DB provider for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-21360 | Microsoft WDAC OLE DB provider for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-21361 | Microsoft WDAC OLE DB provider for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-21362 | Windows Kernel Security Feature Bypass Vulnerability |
| CVE-2024-21363 | Microsoft Message Queuing (MSMQ) Remote Code Execution Vulnerability |
| CVE-2024-21365 | Microsoft WDAC OLE DB provider for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-21366 | Microsoft WDAC OLE DB provider for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-21367 | Microsoft WDAC OLE DB provider for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-21368 | Microsoft WDAC OLE DB provider for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-21369 | Microsoft WDAC OLE DB provider for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-21370 | Microsoft WDAC OLE DB provider for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-21371 | Windows Kernel Elevation of Privilege Vulnerability |
| CVE-2024-21372 | Windows OLE Remote Code Execution Vulnerability |
| CVE-2024-21375 | Microsoft WDAC OLE DB provider for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-21377 | Windows DNS Information Disclosure Vulnerability |
| CVE-2024-21391 | Microsoft WDAC OLE DB provider for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-21405 | Microsoft Message Queuing (MSMQ) Elevation of Privilege Vulnerability |
| CVE-2024-21406 | Windows Print Spooler Spoofing Vulnerability |
| CVE-2024-21412 | Internet Shortcut Files Security Feature Bypass Vulnerability |
| CVE-2024-21420 | Microsoft WDAC OLE DB provider for SQL Server Remote Code Execution Vulnerability |
| CVE-2024-21351 | Windows SmartScreen Security Feature Bypass Vulnerability |
Azure (8 CVEs)
| Important severity | |
| CVE-2024-20667 | Azure DevOps Server Remote Code Execution Vulnerability |
| CVE-2024-20679 | Azure Stack Hub Spoofing Vulnerability |
| CVE-2024-21329 | Azure Connected Machine Agent Elevation of Privilege Vulnerability |
| CVE-2024-21376 | Microsoft Azure Kubernetes Service Confidential Container Remote Code Execution Vulnerability |
| CVE-2024-21381 | Microsoft Azure Active Directory B2C Spoofing Vulnerability |
| CVE-2024-21397 | Microsoft Azure File Sync Elevation of Privilege Vulnerability |
| CVE-2024-21403 | Microsoft Azure Kubernetes Services Confidential Container Elevation of Privilege Vulnerability |
| Moderate severity | |
| CVE-2024-21364 | Microsoft Azure Site Recovery Elevation of Privilege Vulnerability |
Dynamics 365 (8 CVEs)
| Critical severity | |
| CVE-2024-21380 | Microsoft Dynamics Business Central/NAV Information Disclosure Vulnerability |
| Important severity | |
| CVE-2024-21327 | Microsoft Dynamics 365 Customer Engagement Cross-Site Scripting Vulnerability |
| CVE-2024-21328 | Dynamics 365 Sales Spoofing Vulnerability |
| CVE-2024-21389 | Microsoft Dynamics 365 (on-premises) Cross-site Scripting Vulnerability |
| CVE-2024-21393 | Microsoft Dynamics 365 (on-premises) Cross-site Scripting Vulnerability |
| CVE-2024-21394 | Dynamics 365 Field Service Spoofing Vulnerability |
| CVE-2024-21395 | Microsoft Dynamics 365 (on-premises) Cross-site Scripting Vulnerability |
| CVE-2024-21396 | Dynamics 365 Sales Spoofing Vulnerability |
Office (5 CVEs)
| Critical severity | |
| CVE-2024-21413 | Microsoft Office Remote Code Execution Vulnerability |
| Important severity | |
| CVE-2024-20673 | Microsoft Office Remote Code Execution Vulnerability |
| CVE-2024-21378 | Microsoft Outlook Remote Code Execution Vulnerability |
| CVE-2024-21379 | Microsoft Word Remote Code Execution Vulnerability |
| CVE-2024-21384 | Microsoft Office OneNote Remote Code Execution Vulnerability |
.NET (1 CVE, shared with Visual Studio)
| Important severity | |
| CVE-2024-21404 | .NET Denial of Service Vulnerability |
ASP.NET (1 CVE)
| Important severity | |
| CVE-2024-21386 | .NET Denial of Service Vulnerability |
Defender (1 CVE)
| Important severity | |
| CVE-2024-21315
| Microsoft Defender for Endpoint Protection Elevation of Privilege Vulnerability |
Entra (1 CVE)
| Important severity | |
| CVE-2024-21401 | Microsoft Entra Jira Single-Sign-On Plugin Elevation of Privilege Vulnerability |
Exchange (1 CVE)
| Critical severity | |
| CVE-2024-21410 | Microsoft Exchange Server Elevation of Privilege Vulnerability |
Outlook 365 (1 CVE)
| Important severity | |
| CVE-2024-21402 | Microsoft Outlook Elevation of Privilege Vulnerability |
Skype (1 CVE)
| Important severity | |
| CVE-2024-20695 | Skype for Business Information Disclosure Vulnerability |
Teams for Android (1 CVE)
| Important severity | |
| CVE-2024-21374 | Microsoft Teams for Android Information Disclosure Vulnerability |
Visual Studio (1 CVE, shared with ASP.NET)
| Important severity | |
| CVE-2024-21386 | .NET Denial of Service Vulnerability |
Appendix D: Advisories and Other Products
This is a list of advisories and information on other relevant CVEs in the February Microsoft release, sorted by product.
Relevant to Edge / Chromium (6 CVEs)
| CVE-2024-1059 | Chromium: CVE-2024-1059 Use after free in WebRTC |
| CVE-2024-1060 | Chromium: CVE-2024-1060 Use after free in Canvas |
| CVE-2024-1077 | Chromium: CVE-2024-1077 Use after free in Network |
| CVE-2024-1283 | Chromium: CVE-2024-1283 Heap buffer overflow in Skia |
| CVE-2024-1284 | Chromium: CVE-2024-1284 Use after free in Mojo |
| CVE-2024-21399 | Microsoft Edge (Chromium-based) Remote Code Execution Vulnerability |
Relevant to Windows (non-Microsoft release) (one CVE)
| CVE-2023-50387 | MITRE: CVE-2023-50387 DNS RRSIGs and DNSKEYs validation can be abused to remotely consume DNS server resources |
Relevant to Adobe (13 CVEs)
| CVE-2024-20726 | Security updates available for Acrobat Reader |
| CVE-2024-20727 | Security updates available for Acrobat Reader |
| CVE-2024-20728 | Security updates available for Acrobat Reader |
| CVE-2024-20729 | Security updates available for Acrobat Reader |
| CVE-2024-20730 | Security updates available for Acrobat Reader |
| CVE-2024-20731 | Security updates available for Acrobat Reader |
| CVE-2024-20733 | Security updates available for Acrobat Reader |
| CVE-2024-20734 | Security updates available for Acrobat Reader |
| CVE-2024-20735 | Security updates available for Acrobat Reader |
| CVE-2024-20736 | Security updates available for Acrobat Reader |
| CVE-2024-20747 | Security updates available for Acrobat Reader |
| CVE-2024-20748 | Security updates available for Acrobat Reader |
| CVE-2024-20749 | Security updates available for Acrobat Reader |