Top enterprise VPN vulnerabilities
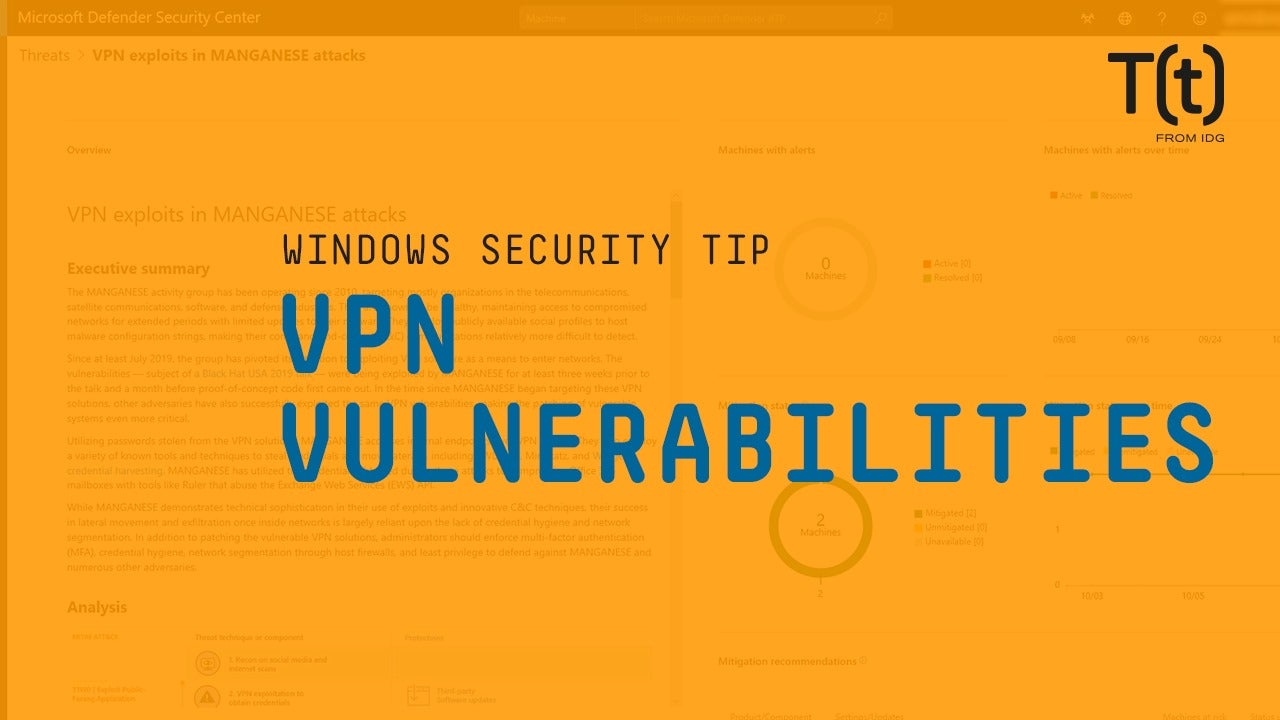
Don’t assume VPNs are always safe. These popular enterprise VPNs all have known remote code execution vulnerabilities.
RSS Reader for Computer Security Articles
Don’t assume VPNs are always safe. These popular enterprise VPNs all have known remote code execution vulnerabilities.
Credit to Author: Evan Schuman| Date: Fri, 04 Oct 2019 13:31:00 -0700
The internet of things (IoT) brings with it a wide range of IT security headaches, along with compliance nightmares — and turf wars.
Internal problem No. 1: Departments that typically have little to no interactions with IT are now directly ordering corporate IoT devices. Maybe you’ve got Facilities purchasing IoT door locks or Maintenance buying a ton of IoT light bulbs. Given that those departments have been purchasing door locks and light bulbs for as long as anyone can remember and have never needed IT or security’s signoff, this can be a problem.
Internal problem No. 2: In many ways, IoT devices (think of devices for tracking pallets on ships or for monitoring where every fleet car is and how fast it’s been driven) are very different from anything else that IT or security has dealt with. The units are capturing data that has never been tracked before — Hello, Compliance. Go away, GDPR regulator — and in different ways, such as bypassing enterprise LANs and cloud networks and using internal antennas to directly communicate.

Credit to Author: Jack Gold| Date: Fri, 04 Oct 2019 08:22:00 -0700
We love our smartphones, but there's a dark side. Their prevalence and users’ tendencies to connect over public Wi-Fi make mobile devices a common target of bad guys. Analyst Jack Gold looks at how to mitigate the risk.
Read More
Credit to Author: Woody Leonhard| Date: Fri, 04 Oct 2019 06:49:00 -0700
You may recall the Keystone Kops reenactment that goes by the code name CVE-2019-1367. In short:
Sept. 23: Microsoft released the CVE-2019-1367 bulletin, and published Win10 cumulative updates in the Microsoft Catalog for versions 1903, 1809, 1803, 1709, 1703, Server 2019 and Server 2016. It also released an IE rollup for Win7, 8.1, Server 2012 and Server 2012 R2. Those were only available by manual download from the Catalog — they didn’t go out through Windows Update, or through the Update Server.
Sept. 24: Microsoft released “optional, non-security” cumulative updates for Win10 version 1809, 1803, 1709, 1703, 1607/Server 2016. Nothing for Win10 version 1903. We also got Monthly Rollup Previews for Win7 and 8.1. Microsoft didn’t bother to mention it, but we found that those Previews include the IE zero-day patch as well. This bunch of patches went out through normal channels — Windows Update, Update Server — but they’re “optional” and “Preview,” which means most savvy individuals and companies won’t install them until they’ve been tested.

Credit to Author: Gregg Keizer| Date: Fri, 04 Oct 2019 04:06:00 -0700
Google has launched a web-based hacked-password checker, part of its efforts to bake an alert system into Chrome.
Called “Password Checker,” the service examines the username-password combinations stored in Chrome’s own password manager and reports back on those authentication pairings that have been exposed in publicly-known data breaches.
The web version can be found at passwords.google.com<>, the umbrella site for Chrome users who run the browser after logging in with their Google account, then use that to synchronize data – including passwords – between copies of Chrome on different devices.
Credit to Author: Bob Violino| Date: Thu, 03 Oct 2019 10:37:00 -0700
Here are five major industries that will benefit from blockchain technology in the near future: financial services and banking, government, healthcare, energy, and transportation and logistics.
Read More
Credit to Author: Sharky| Date: Thu, 03 Oct 2019 03:00:00 -0700
As the IT communications manager at this university, pilot fish is the person who sends out memos about IT policy to users. And he does just that when a phishing email starts circulating on campus.
Never send your user name and password to anyone via email, he warns them, and to give them an example of what to look out for, he pastes in the text of the phishing attempt.
Within minutes, his inbox is flooded with responses from students sending him their campus passwords, their Gmail passwords, their Yahoo passwords and more.
Sharky is looking for fish, not phish. Send me your true tales of IT life at sharky@computerworld.com. You can also subscribe to the Daily Shark Newsletter.
Credit to Author: Woody Leonhard| Date: Wed, 02 Oct 2019 11:00:00 -0700
It’s a smelter-weight slapdown.
In one corner you have the Chicken Little contingent, which insists that September’s IE zero-day patch must be important because Microsoft marked it as “Exploited: Yes” and memorialized it with an extremely odd patch on a Monday, followed in Keystone Kops fashion with a stumbling trail of follow-ons.