How to set up a Microsoft Azure backup process
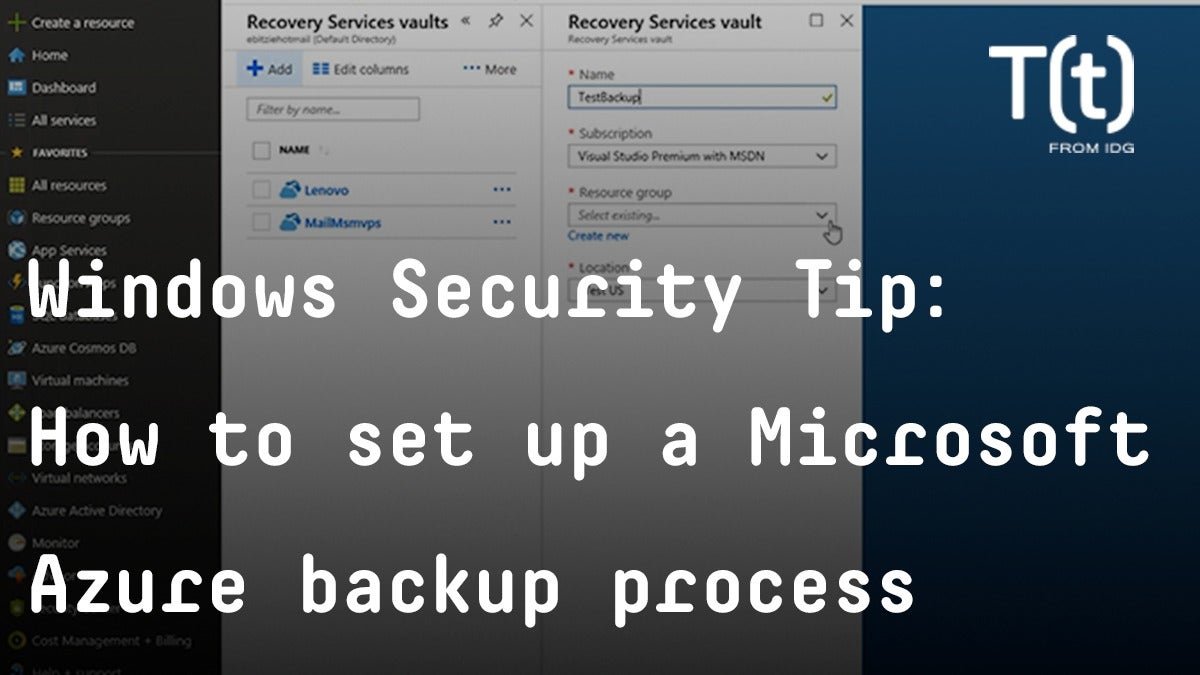
Setting up a backup process in Azure is one way to quickly recover from a ransomware attack.
RSS Reader for Computer Security Articles
Setting up a backup process in Azure is one way to quickly recover from a ransomware attack.

Credit to Author: BrianKrebs| Date: Wed, 15 May 2019 22:09:12 +0000
In the early days of the Internet, there was a period when Internet Protocol 4 (IPv4) addresses (e.g. 4.4.4.4) were given out like cotton candy to anyone who asked. But these days companies are queuing up to obtain new IP space from the various regional registries that periodically dole out the prized digits. With the value of a single IP hovering between $15-$25, those registries are now fighting a wave of shady brokers who specialize in securing new IP address blocks under false pretenses and then reselling to spammers. Here’s the story of one broker who fought back in the courts, and lost spectacularly. On May 14, South Carolina U.S. Attorney Sherri Lydon filed criminal wire fraud charges against Amir Golestan, alleging he and his Charleston, S.C. based company Micfo LLC orchestrated an elaborate network of phony companies and aliases to gather more than 735,000 IPs from the American Registry for Internet Numbers (ARIN), a nonprofit which oversees IP addresses assigned to entities in the U.S., Canada, and parts of the Caribbean.
Read More
Credit to Author: Woody Leonhard| Date: Wed, 15 May 2019 07:13:00 -0700
As of very early Wednesday morning, I don’t hear any loud screams of pain from the May Patch Tuesday bumper crop of patches. There’s still much we don’t know about the “WannaCry-like” security hole in pre-Win8 versions of Windows — more about that in a moment — but all indications at this point lead me to believe that it’s smarter to patch now and figure out how to fix any damage later.
The cause is a bug in Microsoft’s Remote Desktop Services that can allow an attacker to take over your earlier-generation Windows PC if it’s connected to the internet. Not all machines are vulnerable. But the number of exposed machines — the size of the honey jar — makes it likely that somebody will come up with a worm shortly.

Credit to Author: BrianKrebs| Date: Tue, 14 May 2019 17:11:34 +0000
Microsoft today is taking the unusual step of releasing security updates for unsupported but still widely-used Windows operating systems like XP and Windows 2003, citing the discovery of a “wormable” flaw that the company says could be used to fuel a fast-moving malware threat like the WannaCry ransomware attacks of 2017. The vulnerability (CVE-2019-0709) resides in the “remote desktop services” component built into supported versions of Windows, including Windows 7, Windows Server 2008 R2, and Windows Server 2008. It also is present in computers powered by Windows XP and Windows 2003, operating systems for which Microsoft long ago stopped shipping security updates.
Read More
Credit to Author: Jonny Evans| Date: Tue, 14 May 2019 08:17:00 -0700
Hackers have used a security bug inside WhatsApp to install spyware through an infected WhatsApp voice call, and Apple users are affected.
If you are one of the 1.5 billion people who use WhatsApp you should immediately update both your app and your iOS software to the latest version.
The app update includes fixes that should prevent hackers taking over your iPhone, while future Apple updates will also likely address these flaws.
Israeli hackers from a company called the NSO Group developed the spyware specifically so they could get into people’s devices.
Credit to Author: Sharky| Date: Tue, 14 May 2019 03:00:00 -0700
The time is 2001, not long after 9/11, and the place is New York City. Heightened security awareness is the order of the day, and everyone in pilot fish’s office is required to carry an access card that activates the office doors. Look out for tailgaters, they’re all told. Those are people dressed like professionals who slide in behind someone with an access card and then steal wallets, coats and more.
One morning, fish arrives at the office and passes a man in business-casual attire carrying a laptop tucked under his arm and headed for the elevators. Fish doesn’t recognize the fellow, but he does know the co-worker who is running behind him, calling for someone to call building security and the police. The co-worker had returned to an empty desk just seconds after this tailgater had snatched his laptop, well before the tailgater could make a clean getaway.

Credit to Author: Lucas Mearian| Date: Tue, 14 May 2019 03:00:00 -0700
After more than a year in development, Microsoft has chosen Bitcoin as the blockchain platform for a decentralized identification (DID) verification system that will allow users to have secure access to an online persona via an encrypted database hub.
The implications of the new ID network could include the elimination of passwords. A company would be able to verify the background of a new employee and onboard them with the click of a single virtual button, or a banking customer could verify their identity for a loan without exposing personally identifiable information – again with a click of a button.
Credit to Author: BrianKrebs| Date: Fri, 10 May 2019 17:02:56 +0000
Eight Americans and an Irishman have been charged with wire fraud this week for allegedly hijacking mobile phones through SIM-swapping, a form of fraud in which scammers bribe or trick employees at mobile phone stores into seizing control of the target’s phone number and diverting all texts and phone calls to the attacker’s mobile device. From there, the attackers simply start requesting password reset links via text message for a variety of accounts tied to the hijacked phone number. All told, the government said this gang — allegedly known to its members as “The Community” — made more than $2.4 million stealing cryptocurrencies and extorting people for restoring access to social media accounts that were hijacked after a successful SIM-swap.
Read More