Payroll Provider Gives Extortionists a Payday
Credit to Author: BrianKrebs| Date: Sun, 24 Feb 2019 00:16:06 +0000
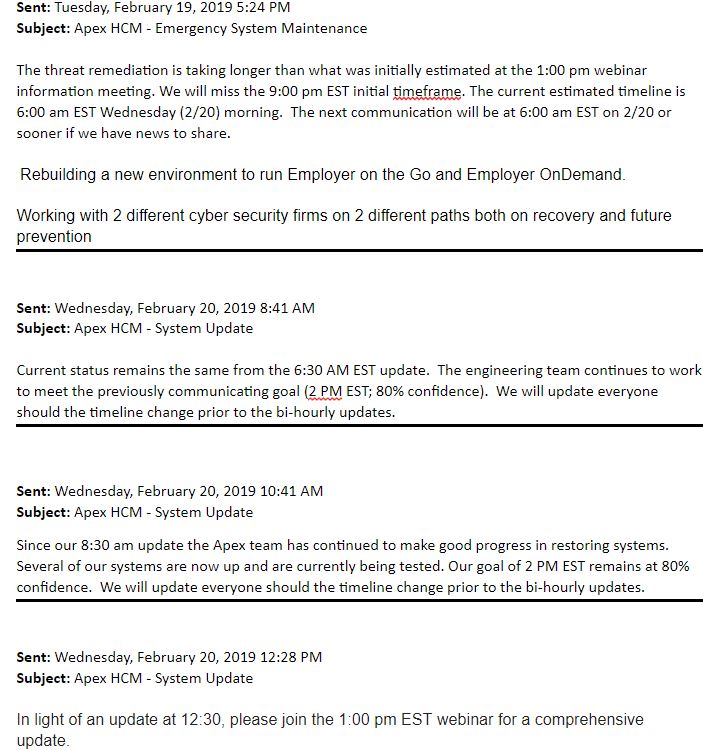
Payroll software provider Apex Human Capital Management suffered a ransomware attack this week that severed payroll management services for hundreds of the company’s customers for nearly three days. Faced with the threat of an extended outage, Apex chose to pay the ransom demand and begin the process of restoring service to customers.
Read More




