Apple Phone Phishing Scams Getting Better
Credit to Author: BrianKrebs| Date: Thu, 03 Jan 2019 19:21:40 +0000
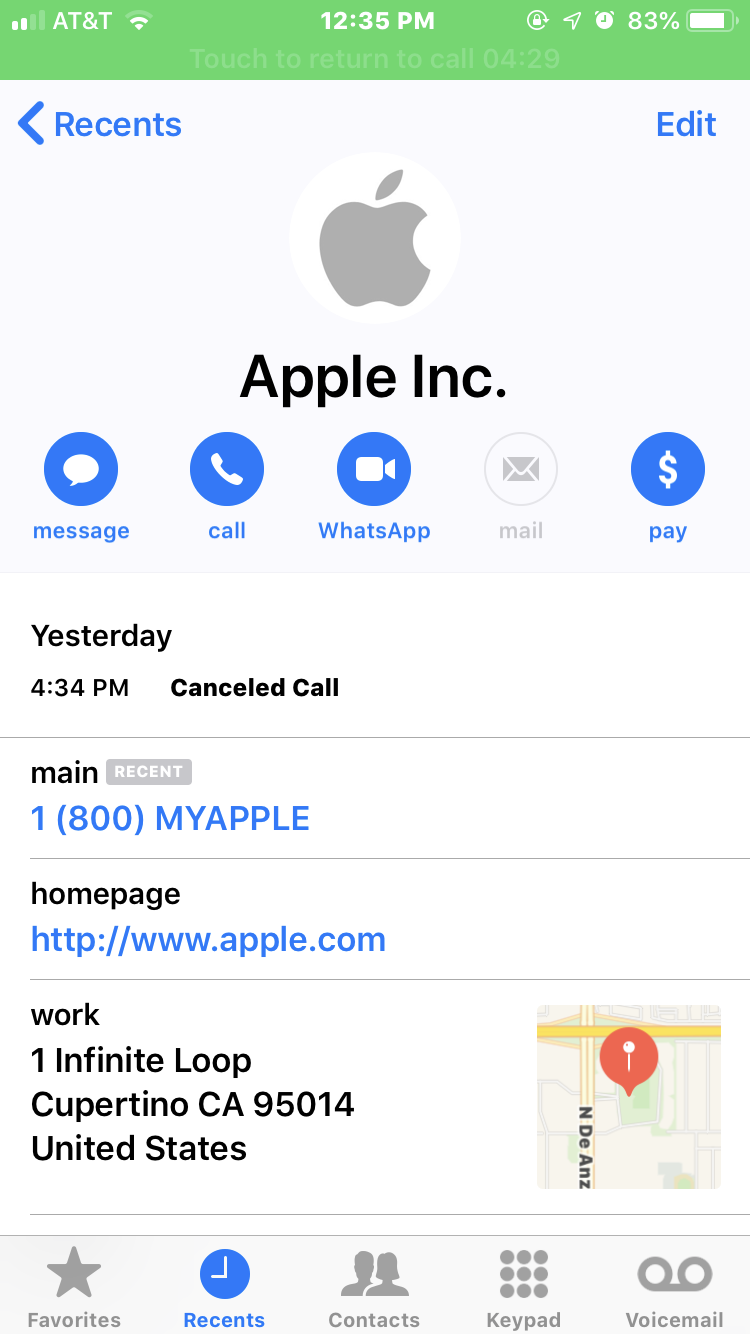
A new phone-based phishing scam that spoofs Apple Inc. is likely to fool quite a few people. It starts with an automated call that display’s Apple’s logo, address and real phone number, warning about a data breach at the company. The scary part is that if the recipient is an iPhone user who then requests a call back from Apple’s legitimate customer support Web page, the fake call gets indexed in the iPhone’s “recent calls” list as a previous call from the legitimate Apple Support line.
Read More

![CW > In Memoriam 2018 > Tech luminaries we lost this year [slideshow cover]](https://images.idgesg.net/images/article/2018/12/cw_luminaries_2018_slide_01_cover_lights_by_freedommaster_getty_images-100782416-large.jpg)
