BitLocker on self-encrypted SSDs blown; Microsoft advises you switch to software protection
Credit to Author: Woody Leonhard| Date: Wed, 07 Nov 2018 16:08:00 -0800
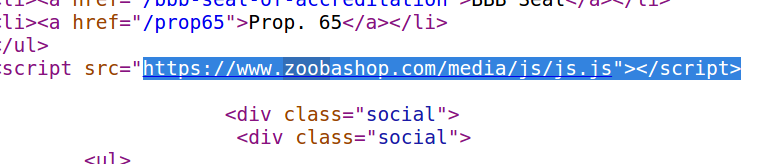
Yesterday, Microsoft released ADV180028, Guidance for configuring BitLocker to enforce software encryption, in response to a clever crack published on Monday by Carlo Meijer and Bernard van Gastel at Radboud University in the Netherlands (PDF).