Why security is the first thing to go, episode 65,723
Credit to Author: Sharky| Date: Mon, 10 Sep 2018 03:00:00 -0700
IT contractor has a project to upgrade some software for a client — and the project is way behind schedule, says a pilot fish on the client side.
And why is that such a problem? “The existing product goes End-of-Life soon, at which time it will no longer be an approved product for us,” fish explains.
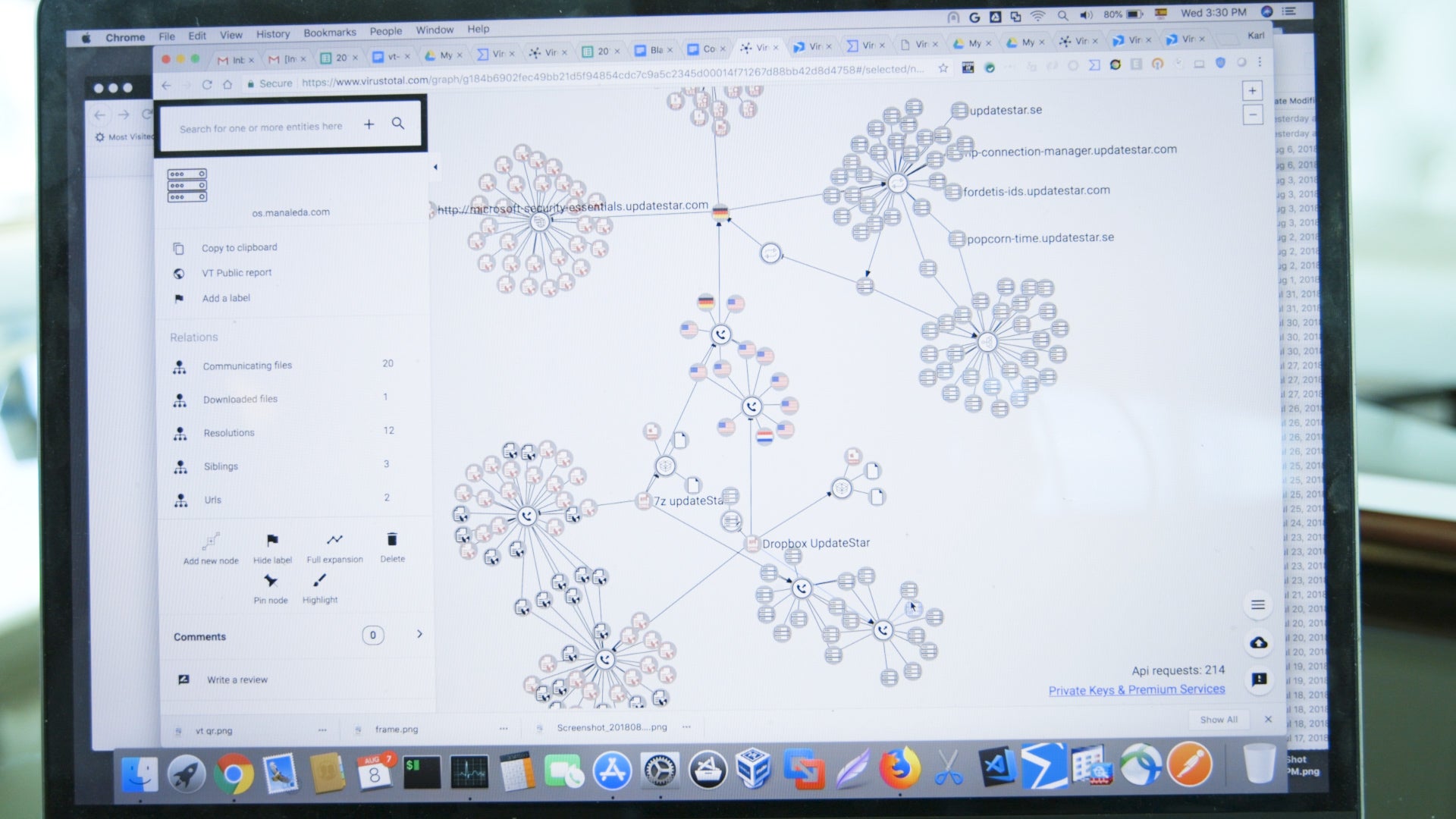
“The contractor’s people come in and pitch their schedule to upper management. In the briefing, they bring up the fact that the new product is not even approved to be on our highly secured network, and they have not even started on getting it approved.
“Essentially, if they have to get it approved, they can never get it deployed on time.