DDoS-for-Hire Service Webstresser Dismantled
Credit to Author: BrianKrebs| Date: Wed, 25 Apr 2018 17:41:37 +0000
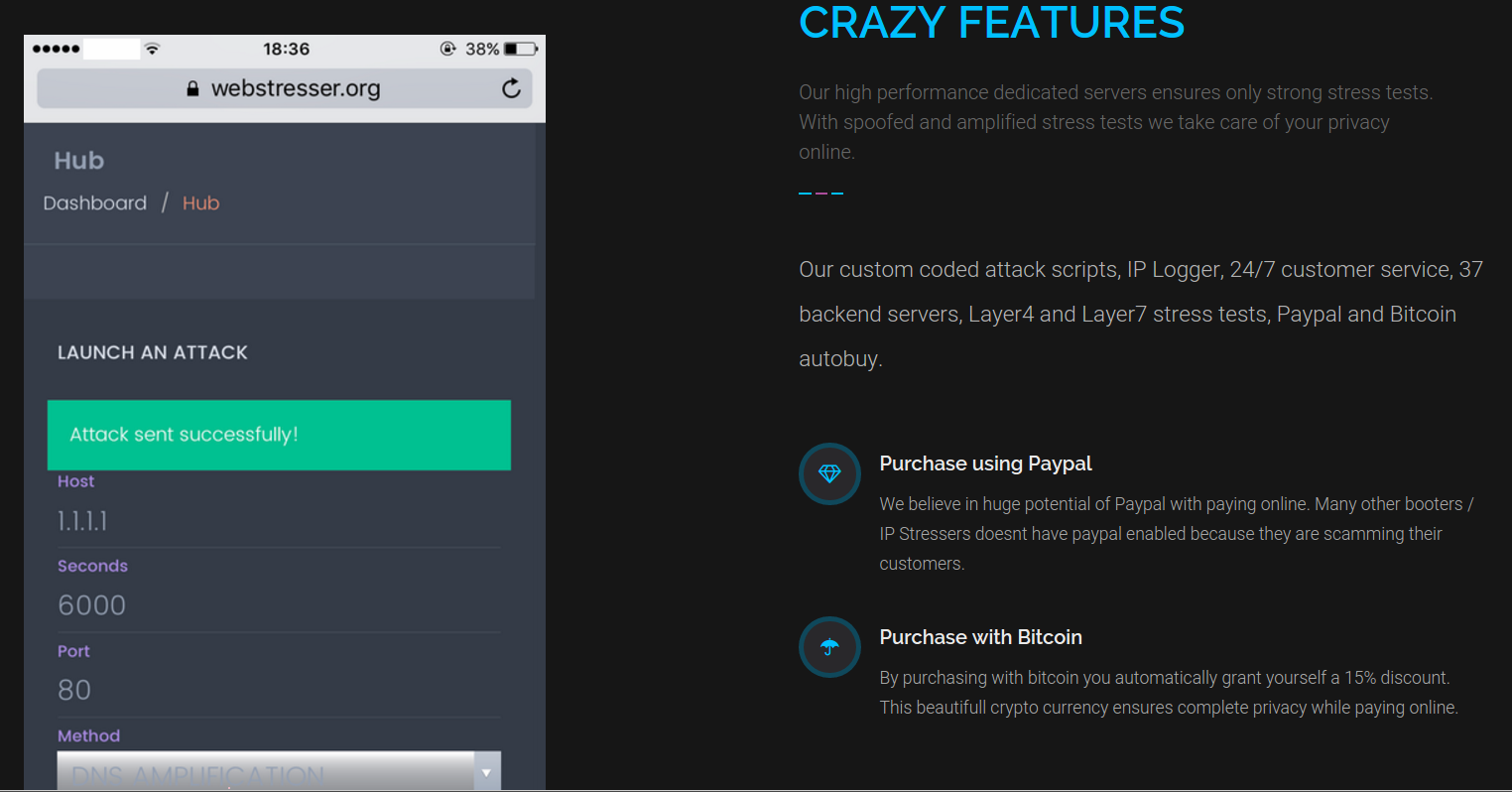
Authorities in the U.S., U.K. and the Netherlands on Tuesday took down popular online attack-for-hire service WebStresser.org and arrested its alleged administrators. Investigators say that prior to the takedown, the service had more than 136,000 registered users and was responsible for launching somewhere between four and six million attacks over the past three years.
Read More




