Why Linguists Watched the Same Season of ‘Big Brother’ for 6 Years

Credit to Author: Claire Downs| Date: Wed, 06 Sep 2017 17:07:01 +0000
Sometimes you gotta suffer for science.
Read MoreRSS Reader for Computer Security Articles

Credit to Author: Claire Downs| Date: Wed, 06 Sep 2017 17:07:01 +0000
Sometimes you gotta suffer for science.
Read More
Credit to Author: Bryson Masse| Date: Wed, 06 Sep 2017 17:00:00 +0000
Researchers from high-profile institutions are falling for these scams.
Read More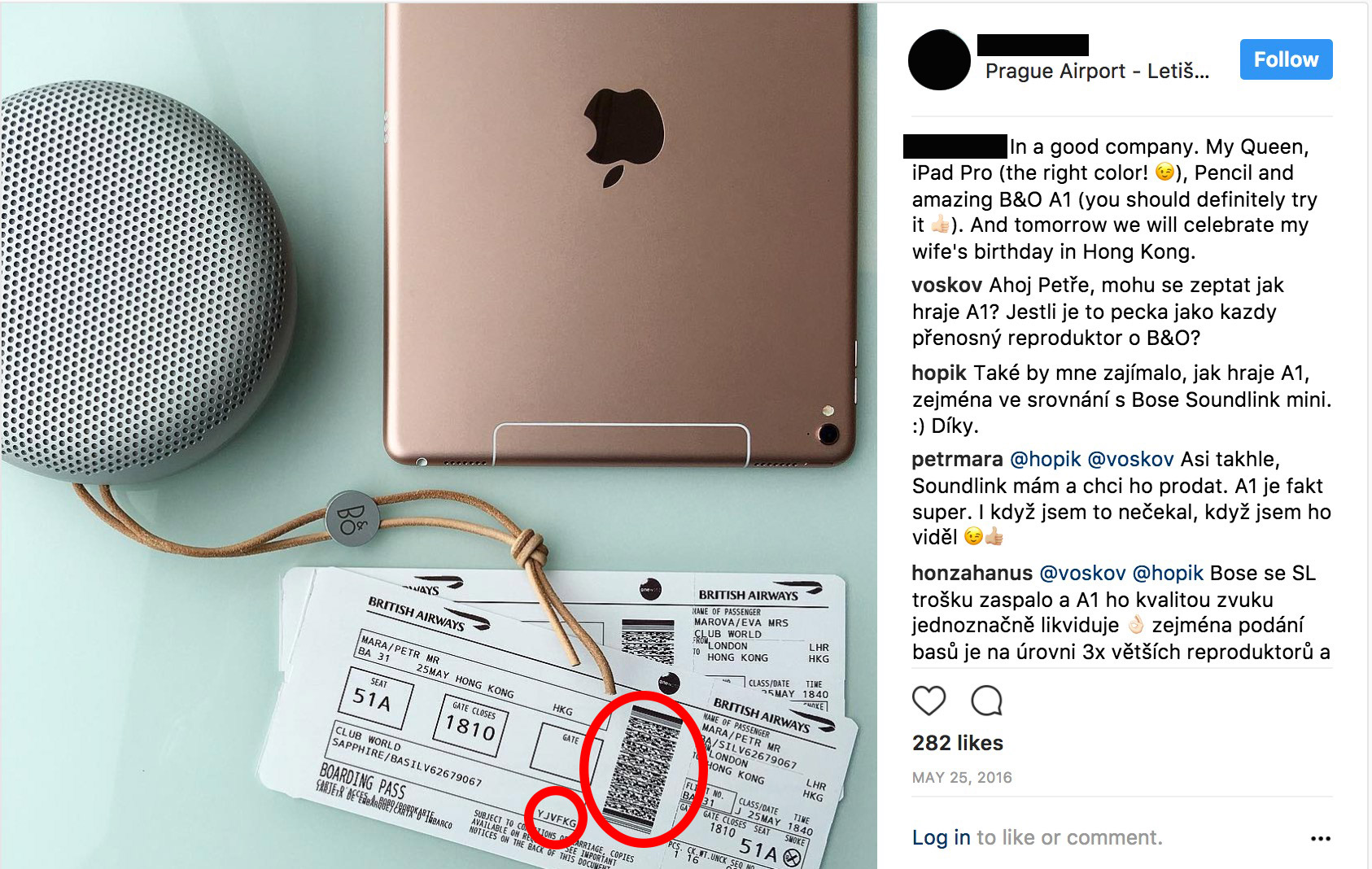
Credit to Author: Theresa Locker| Date: Wed, 06 Sep 2017 16:19:05 +0000
Not only can it wind up being expensive to post these things on Instagram, Facebook, or Twitter—it can also be very dangerous.
Read More
Credit to Author: Claire Downs| Date: Wed, 06 Sep 2017 14:51:28 +0000
4,426,165,368 possible queen positions.
Read More
Credit to Author: Louise Matsakis| Date: Wed, 06 Sep 2017 14:03:11 +0000
A new paper has troubling implications.
Read More
Credit to Author: Evan Schuman| Date: Tue, 05 Sep 2017 14:13:00 -0700
IT is seeing a very dangerous collision of two trends: BYOD and mobile apps. IT’s job is, among other things, to protect corporate data, a portion of the company’s intellectual property. And yet easily downloaded consumer apps are threatening that data security by sharing their sensitive data with mobile apps that have almost infinite capabilities.
Consider this reference from a scary story courtesy of The Intercept: “When launched for the first time, [popular app Sarahah] immediately harvests and uploads all phone numbers and email addresses in your address book. Although Sarahah does in some cases ask for permission to access contacts, it does not disclose that it uploads such data, nor does it seem to make any functional use of the information.”
To read this article in full or to leave a comment, please click here

Credit to Author: Lorenzo Franceschi-Bicchierai| Date: Wed, 06 Sep 2017 13:00:00 +0000
PSA: don’t give anyone your Bitcoin private key.
Read More