Sorry, Scientists Did Not Invent an ‘Exercise Pill’

Credit to Author: Kaleigh Rogers| Date: Fri, 01 Sep 2017 15:09:00 +0000
Send this to your friends who posted this nonsense on their timelines.
Read MoreRSS Reader for Computer Security Articles

Credit to Author: Kaleigh Rogers| Date: Fri, 01 Sep 2017 15:09:00 +0000
Send this to your friends who posted this nonsense on their timelines.
Read More
Credit to Author: Bettina Mangiaracina| Date: Fri, 01 Sep 2017 14:30:00 +0000
Rules are made to be broken.
Read More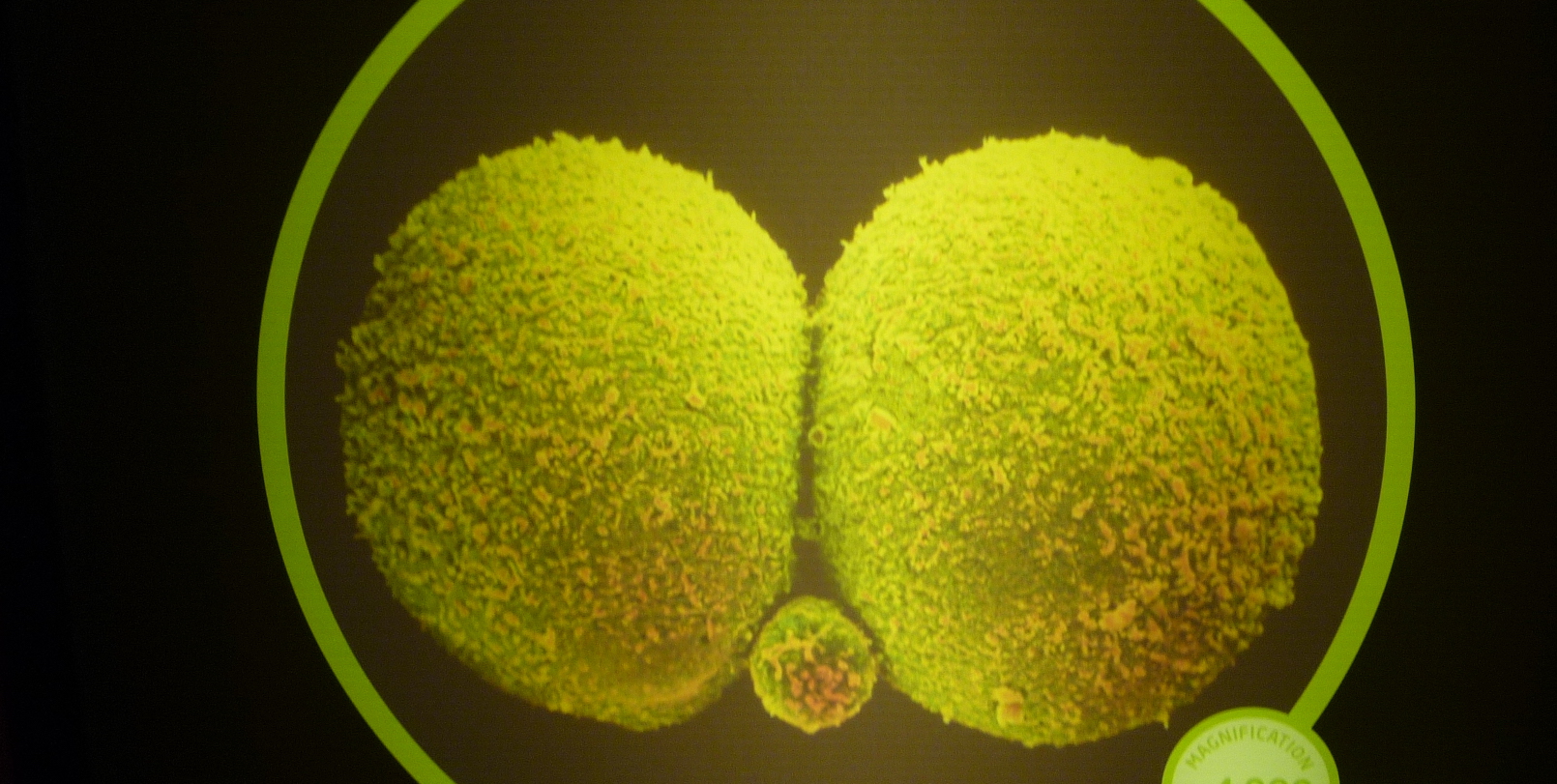
Credit to Author: Tanya Basu| Date: Fri, 01 Sep 2017 14:27:49 +0000
Some of the world’s best geneticists say they need more proof before we welcome our designer baby future.
Read More
Credit to Author: Claire Lampen| Date: Fri, 01 Sep 2017 14:00:00 +0000
Who assumed women want to fuck dolphins?
Read More
Credit to Author: John Brandon| Date: Thu, 31 Aug 2017 13:52:00 -0700
The term “improperly configured” is a real plague on the IT landscape.
It can refer to a firewall protecting an enterprise; it can create problems on a web server. For one newly minted smartphone company, it can also look pretty embarrassing.
Essential phone recently sent an email to customers asking for proof of identity. This request was a little odd in the first place — who does that anymore? The email basically asked customers to send a picture of a photo identification or passport by email. From a security standpoint, that’s a bit like asking people to text your credit card number to a hacker.
To read this article in full or to leave a comment, please click here

Credit to Author: Samantha Cole| Date: Fri, 01 Sep 2017 13:43:35 +0000
A more instinctual approach to data security.
Read More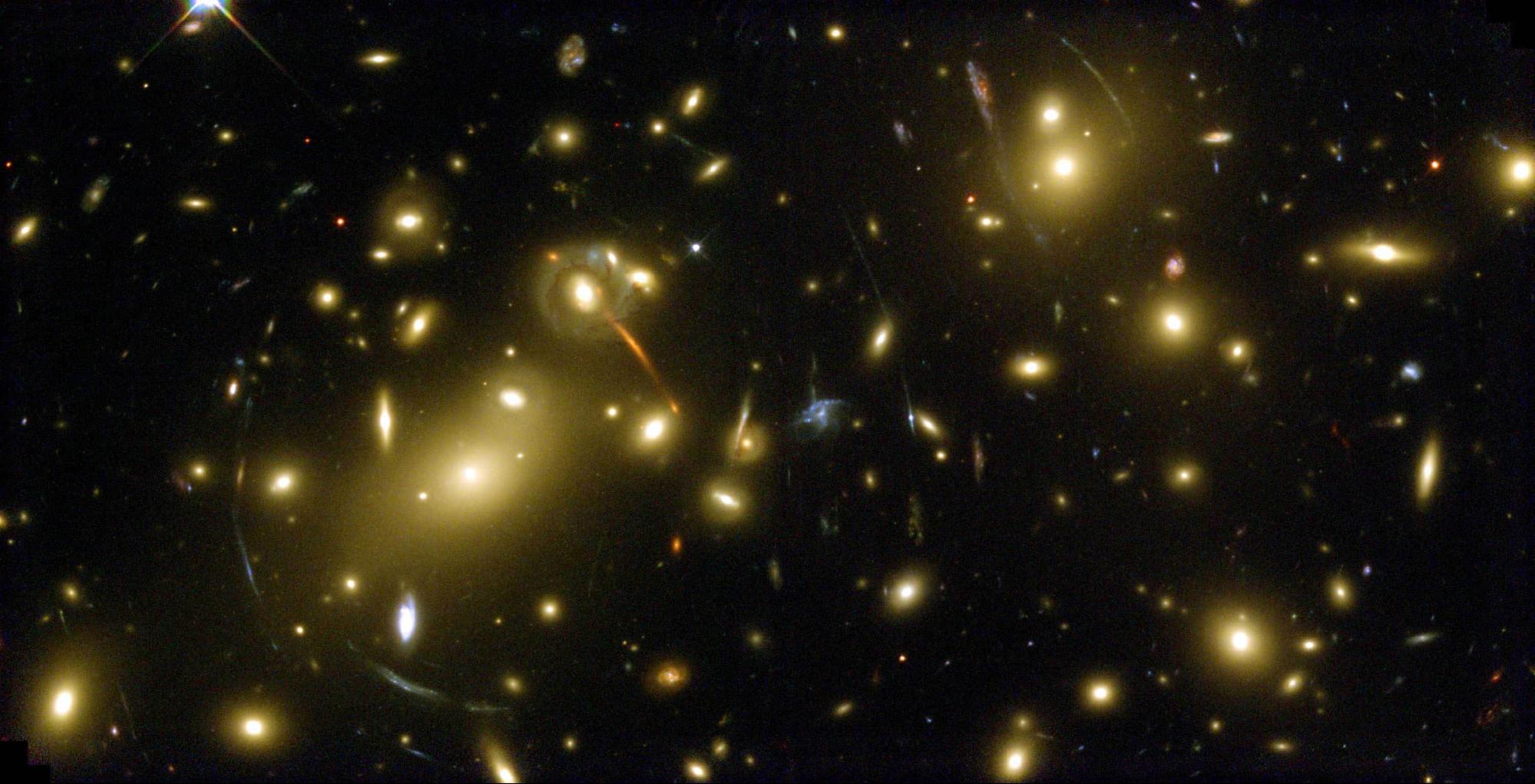
Credit to Author: Michael Byrne| Date: Fri, 01 Sep 2017 12:15:40 +0000
Machine learning offers a natural solution to astronomy’s looming data deluge.
Read More
Credit to Author: John Brandon| Date: Thu, 31 Aug 2017 13:52:00 -0700
The term “improperly configured” is a real plague on the IT landscape.
It can refer to a firewall protecting an enterprise; it can create problems on a web server. For one newly minted smartphone company, it can also look pretty embarrassing.
Essential phone recently sent out an email to customers asking for proof of identity. This request was a little odd in the first place–who does that anymore? The email basically asked customers to send a picture of a photo identification or passport by email. From a security standpoint, that’s a bit like asking people to text your credit card number to a hacker.
To read this article in full or to leave a comment, please click here