Tiptoe through the bugs and get Windows and Office updated
Credit to Author: Woody Leonhard| Date: Wed, 26 Jul 2017 09:55:00 -0700
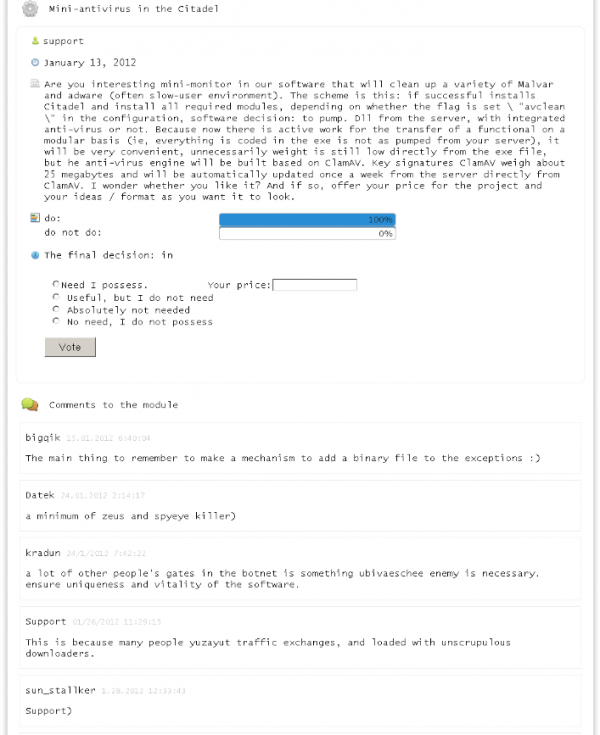
The fourth Tuesday of the month has come and gone, and it now looks reasonably safe to patch Windows and Office. I was expecting two big releases yesterday — one to fix numerous bugs in Win10 Creators Update, version 1703; the other to plug the bugs introduced by June’s Office security patches — but neither trove appeared. Given Microsoft’s past patterns, it’s unlikely that we’ll see any more serious patches until next month’s Patch Tuesday, on Aug. 8.
There’s also a bit of additional impetus right now. On July 17, security researcher Haifei published a proof of concept for running malware scripts directly in Office apps. I haven’t seen any exploits in the wild as yet, but it would be a good idea to install KB 3213640 (Office 2007), KB 3213624 (Office 2010), KB 3213555 (Office 2013) and/or KB 3213545 (Office 2016) in the short term. (Thx to @LeaningTowardsLinux.) Note that none of these patches, as best as I can tell, correct the Office bugs introduced in June.
To read this article in full or to leave a comment, please click here