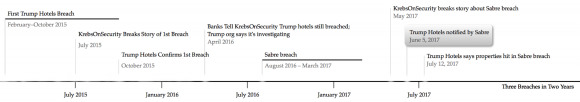
Trump Hotels Hit By 3rd Card Breach in 2 Years
Credit to Author: BrianKrebs| Date: Wed, 19 Jul 2017 15:43:36 +0000
Maybe some of you missed this amid all the breach news recently (I know I did), but Trump International Hotels Management LLC last week announced its third credit-card data breach in the past two years. I thought it might be useful to see these events plotted on a timeline, because it suggests that virtually anyone who used a credit card at a Trump property in the past two years likely has had their card data stolen and put on sale in the cybercrime underground as a result.
Read More