Mingis on Tech: The alphabet soup of mobile device management

Do you know your MDM from MAM and EMM? It's all about BYOD, and how companies can keep data safe while making it easier for workers to be productive with their own devices.
RSS Reader for Computer Security Articles

Do you know your MDM from MAM and EMM? It's all about BYOD, and how companies can keep data safe while making it easier for workers to be productive with their own devices.
Credit to Author: BrianKrebs| Date: Tue, 06 Jun 2017 12:12:47 +0000
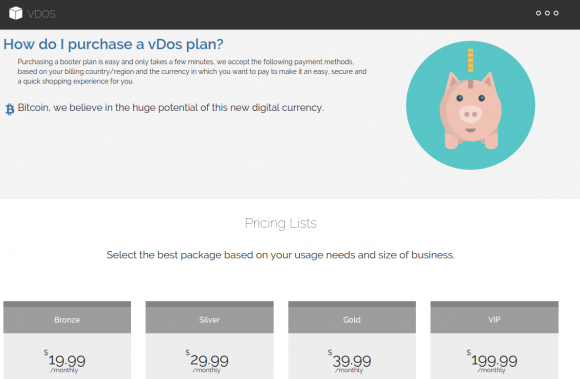
A new report proves the value of following the money in the fight against dodgy cybercrime services known as “booters” or “stressers” — virtual hired muscle that can be rented to knock nearly any website offline. Last fall, two 18-year-old Israeli men were arrested for allegedly running a vDOS, perhaps the most successful booter service of all time. The pair were detained within hours of being named in a story on this blog as the co-proprietors of the service (this site would later suffer a three-day outage as a result of an attack that was alleged to have been purchased in retribution for my reporting on vDOS). That initial vDOS story was based on data shared by an anonymous source who had hacked vDOS and obtained its private user and attack database. The story showed how the service made approximately $600,000 over just two of the four years it was in operation. Most of those profits came in the form of credit card payments via PayPal. But prior to vDOS’s takedown in September 2016, the service was already under siege thanks to work done by a group of academic researchers who teamed up with PayPal to identify and close accounts that vDOS and other booter services were using to process customer payments. The researchers found that their interventions cut profits in half for the popular booter service, and helped reduce the number of attacks coming out of it by at least 40 percent.
Read More
Credit to Author: Sandra Henry-Stocker| Date: Mon, 05 Jun 2017 11:13:00 -0700
In the last few years, we’ve been seeing some significant changes in the suggestions that security experts are making for password security. While previous guidance increasingly pushed complexity in terms of password length, the mix of characters used, controls over password reuse, and forced periodic changes, specialists have been questioning whether making passwords complex wasn’t actually working against security concerns rather than promoting them.
Security specialists have also argued that forcing complexity down users’ throats has led to them writing passwords down or forgetting them and having to get them reset. They argued that replacing a password character with a digit or an uppercase character might make a password look complicated, but does not actually make it any less vulnerable to compromise. In fact, when users are forced to include a variety of characters in their passwords, they generally do so in very predictable ways. Instead of “password”, they might use “Passw0rd” or even “P4ssw0rd!”, but the variations don’t make the passwords significantly less guessable. People are just not very good at generating anything that’s truly random.
To read this article in full or to leave a comment, please click here
Credit to Author: SSD / Maor Schwartz| Date: Fri, 02 Jun 2017 07:59:35 +0000
Vulnerability Summary The following advisory describes a Stack Buffer Overflow vulnerability found in HPE Intelligent Management Center version v7.2 (E0403P10) Enterprise, this vulnerability leads to an exploitable remote code execution. HPE Intelligent Management Center (iMC) delivers comprehensive management across campus core and data center networks. iMC converts meaningless network data to actionable information to keep … Continue reading SSD Advisory – HPE Intelligent Management Center (iMC) Code Execution
Read More
Credit to Author: BrianKrebs| Date: Thu, 01 Jun 2017 12:55:33 +0000
OneLogin, an online service that lets users manage logins to sites and apps from a single platform, says it has suffered a security breach in which customer data was compromised, including the ability to decrypt encrypted data. Headquartered in San Francisco, OneLogin provides single sign-on and identity management for cloud-base applications. OneLogin counts among its customers some 2,000 companies in 44 countries, over 300 app vendors and more than 70 software-as-a-service providers.
Read More
Credit to Author: BrianKrebs| Date: Thu, 01 Jun 2017 02:27:12 +0000
For the second time in less than three years, Kmart Stores is battling a malware-based security breach of its store credit card processing systems. Last week I began hearing from smaller banks and credit unions who said they strongly suspected another card breach at Kmart. Some of those institutions received alerts from the credit card companies about batches of stolen cards that all had one thing in comment: They were all used at Kmart locations. Ask to respond to rumors about a card breach, Kmart’s parent company Sears Holdings said some of its payment systems were infected with malicious software:
Read More
Credit to Author: SSD / Maor Schwartz| Date: Wed, 31 May 2017 07:33:40 +0000
Vulnerability Summary The following advisory describe information disclosure vulnerability in Cisco DPC3928AD DOCSIS wireless router. The Cisco DPC3928AD DOCSIS is a home wireless router that is currently “Out of support” but is provided by ISPs on a large scale in many countries. Credit An independent security researcher has reported this vulnerability to Beyond Security’s SecuriTeam … Continue reading SSD Advisory – Cisco DPC3928AD DOCSIS Wireless Router Information Disclosure
Read More
Credit to Author: Evan Schuman| Date: Wed, 31 May 2017 12:51:00 -0700
A major problem with biometric authentication is that, when it doesn’t work, there are few good options to proceed with the authentication. When the system says that’s not your eyeball, there’s no fallback akin to “Forgot your password?” You have to revert to some less discerning authentication method, such as a PIN.
Some vendors are trying to deal with this by using a simultaneous, multi-biometric method. “Simultaneous” is important because using two methods consecutively would take more time, resulting in end users’ resistance and lower participation rates.
One vendor, Sensory, is making serious headway in figuring out interesting ways to use dual biometrics.
To read this article in full or to leave a comment, please click here