Yahoo warns users of account breaches related to recent attacks

Credit to Author: Grant Gross| Date: Wed, 15 Feb 2017 11:01:00 -0800
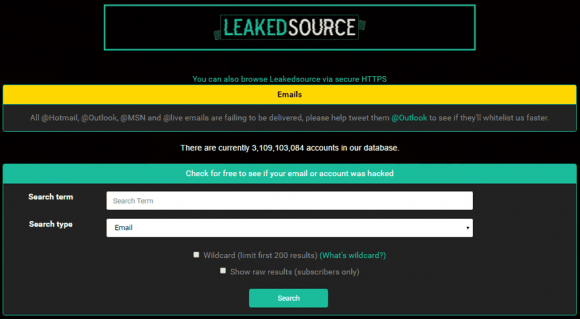
Yahoo has begun warning individual users that their accounts with the service may have been compromised in a massive data breach it reported late last year.
The warning, in email messages sent from Yahoo CISO Bob Lord, tell users that a forged cookie may have been used to access their accounts in previous years.
The warning to Yahoo users come at the same time that news reports suggest that Verizon Communications, in negotiations to buy Yahoo, may be seeking a discount of $250 million because of the data breaches.
To read this article in full or to leave a comment, please click here