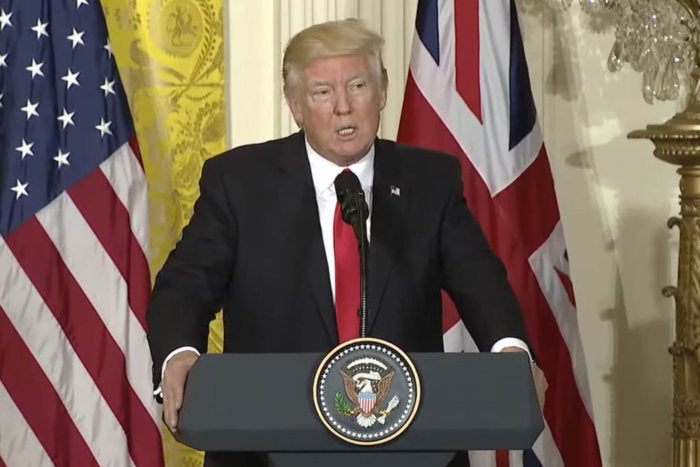
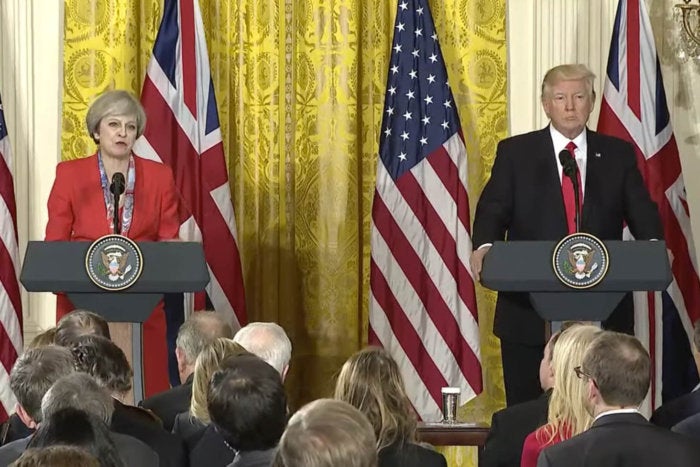
If President Donald Trump is still using his personal, unsecured Android smartphone, as reported, he is surely creating bucketsful of worry for White House communications security staff.
As CIOs and Chief Information Security Officers already know, any organization can install strong security technology into a network or a smartphone, only to be defeated if end users don’t use it or follow safe cyber practices.
“The most vulnerable parts of communications are the people, and if they aren’t taking precautions, problems exist,” said Chris Perry, chief operating officer for Secured Communications, a provider of encrypted VPNs for mobile devices used by governments and companies.
To read this article in full or to leave a comment, please click here