How to prevent data loss on your network
Use these tools and techniques to protect important data from being exfiltrated from your Windows network.
RSS Reader for Computer Security Articles
Use these tools and techniques to protect important data from being exfiltrated from your Windows network.

Enforcement of the California Consumer Privacy Act begins this summer, but lawsuits are already being filed. To help you comply and avoid being sued, CSO contributor Maria Korolov joins IDG TECH(talk) host Juliet Beauchamp to discuss critical components of the CCPA and answer viewers’ questions.
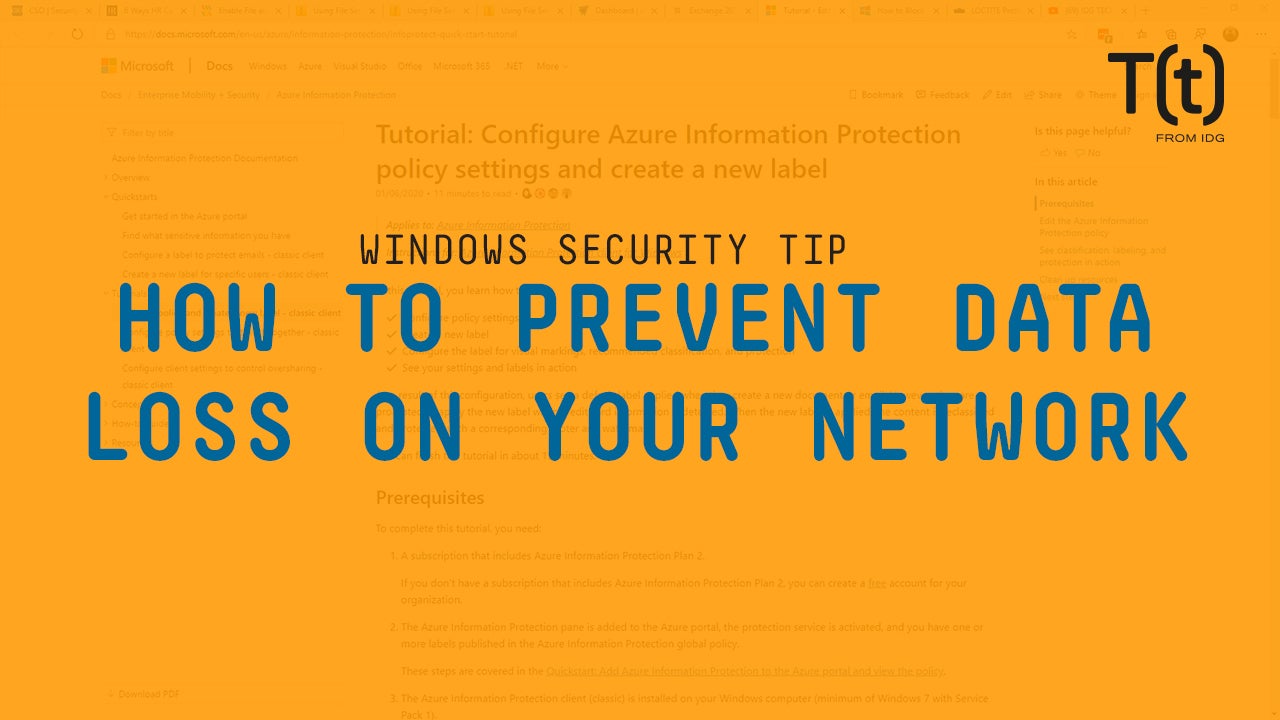
Credit to Author: BrianKrebs| Date: Tue, 18 Feb 2020 18:00:29 +0000
Crooks are constantly dreaming up new ways to use and conceal stolen credit card data. According to the U.S. Secret Service, the latest scheme involves stolen card information embedded in barcodes affixed to phony money network rewards cards. The scammers then pay for merchandise by instructing a cashier to scan the barcode and enter the expiration date and card security code.
Read More
Credit to Author: Steven J. Vaughan-Nichols| Date: Tue, 18 Feb 2020 07:00:00 -0800
Why am I still writing about Windows 7? It’s dead, Jim! The tombstone reads, “June 22, 2009 – January 14, 2020.” It was a good run, but unless you’re shelling out some serious coin for Windows 7 Extended Security Updates (ESU), you shouldn’t be running Windows 7.
But many of you are. According to the best survey of who’s running what, the U.S. government’s Digital Analytics Program (DAP), on Feb. 14, weeks after Win7’s end of life, just over one in 20 of Windows users was still using Windows 7! Oh, come on! More than 5%! A dead and buried OS! Get with the program!

Credit to Author: Evan Schuman| Date: Tue, 18 Feb 2020 03:00:00 -0800
Many security professionals have long held that the words “mobile security” are an oxymoron. True or not, with today’s mobile usage soaring in enterprises, that viewpoint may become irrelevant. It’s a reasonable estimate that 2020 knowledge workers use mobile devices to either supplement or handle much of their work 98% of the time. Laptops still have a role (OK, if you want to get literal, I suppose a laptop can be considered mobile), but that’s only because of their larger screens and keyboards. I’d give mobile players maybe three more years before that becomes moot.
That means that security on mobile needs to become a top priority. To date, that usually has been addressed with enterprise-grade mobile VPNs, antivirus and more secure communication methods (such as Signal). But in the latest Verizon Data Breach Investigations Report — always a worthwhile read — Verizon eloquently argues that aside from wireless, the form factor of mobile in and of itself poses security risks.
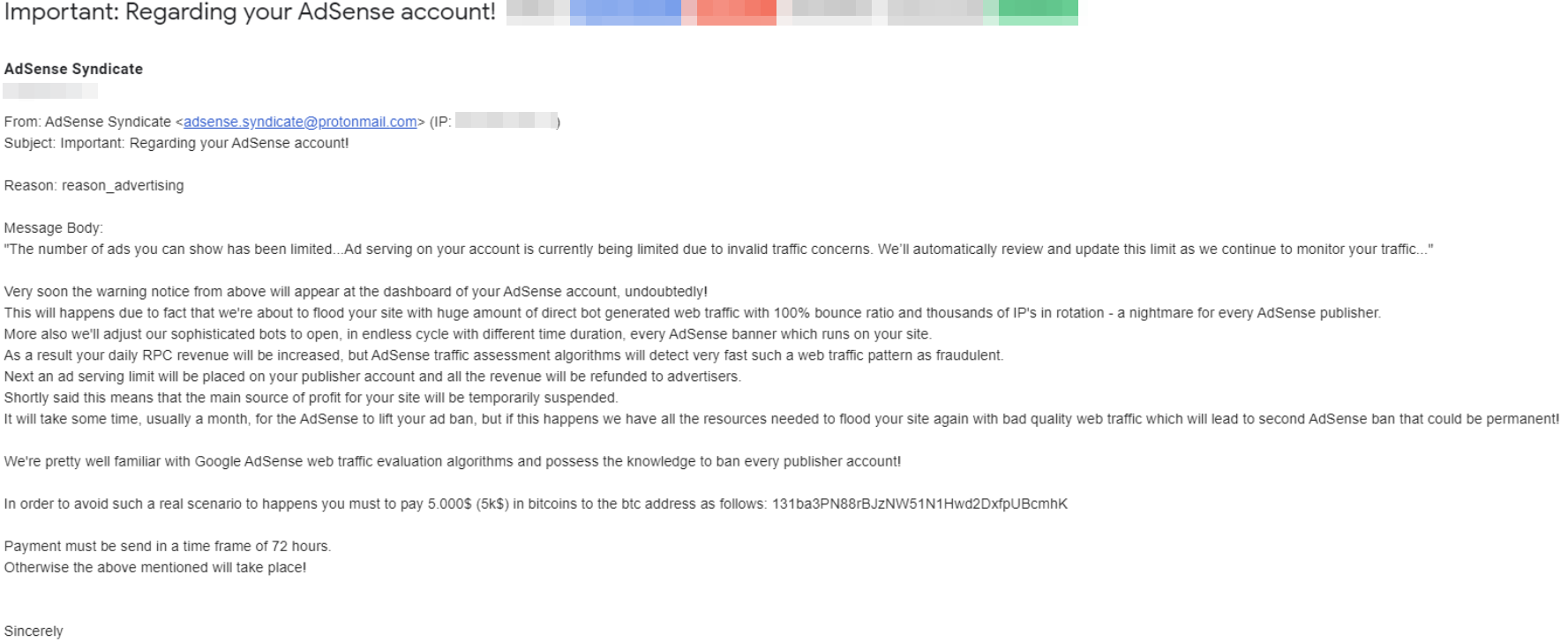
Credit to Author: BrianKrebs| Date: Mon, 17 Feb 2020 14:13:06 +0000
A new email-based extortion scheme apparently is making the rounds, targeting Web site owners serving banner ads through Google’s AdSense program. In this scam, the fraudsters demand bitcoin in exchange for a promise not to flood the publisher’s ads with so much bot and junk traffic that Google’s automated anti-fraud systems suspend the user’s AdSense account for suspicious traffic.
Read More
Credit to Author: Lucas Mearian| Date: Mon, 17 Feb 2020 03:00:00 -0800
In 2018, a video of former President Barrack Obama surfaced on YouTube explaining how easily technology could be used to manipulate video and create fake news. It got more than 7.2 million views.
In the video, Obama explains how we live in dangerous times when “enemies” can make anyone say anything at any point in time. Moments later, it’s revealed that the video was itself faked.
Whether its news articles, images or video, fake and misleading content has proliferated across the internet over the past five or so years. One possible solution to the problem now being proposed would standardize how content is delivered online, with anything outside those standards not trusted.

Credit to Author: Gregg Keizer| Date: Sat, 15 Feb 2020 05:35:00 -0800
Microsoft this week threw a wrench into the workings of its long-touted Windows 7 post-retirement support, telling IT administrators that there was a brand new prerequisite that must be installed before they can download the patches they’d already paid for.
The last-minute requirement was titled “Extended Security Updates Licensing Preparation Package” and identified as KB4538483 in Microsoft’s numerical format.
The licensing prep package can be downloaded manually from the Microsoft Update Catalog. It should also appear in WSUS (Windows Server Update Services), the patch management platform used by many commercial customers. It will not, however, be automatically delivered through the Windows Update service, which some very small businesses rely on to provide them necessary patches.