In the last few years, we’ve been seeing some significant changes in the suggestions that security experts are making for password security. While previous guidance increasingly pushed complexity in terms of password length, the mix of characters used, controls over password reuse, and forced periodic changes, specialists have been questioning whether making passwords complex wasn’t actually working against security concerns rather than promoting them.
Security specialists have also argued that forcing complexity down users’ throats has led to them writing passwords down or forgetting them and having to get them reset. They argued that replacing a password character with a digit or an uppercase character might make a password look complicated, but does not actually make it any less vulnerable to compromise. In fact, when users are forced to include a variety of characters in their passwords, they generally do so in very predictable ways. Instead of “password”, they might use “Passw0rd” or even “P4ssw0rd!”, but the variations don’t make the passwords significantly less guessable. People are just not very good at generating anything that’s truly random.
To read this article in full or to leave a comment, please click here
 As we predicted in 2016, cyberpropaganda is a major growth area for cybercriminals. Per that prediction, “The rise in the Internet penetration has opened the opportunity for invested parties to use the Internet as a free-for-all tool to influence public opinion to go one way or another.” Today, we know this through Wikileaks and self-proclaimed…
As we predicted in 2016, cyberpropaganda is a major growth area for cybercriminals. Per that prediction, “The rise in the Internet penetration has opened the opportunity for invested parties to use the Internet as a free-for-all tool to influence public opinion to go one way or another.” Today, we know this through Wikileaks and self-proclaimed… While it sounds similar to Business Email Compromise, Business Process Compromise is an entirely new beast.
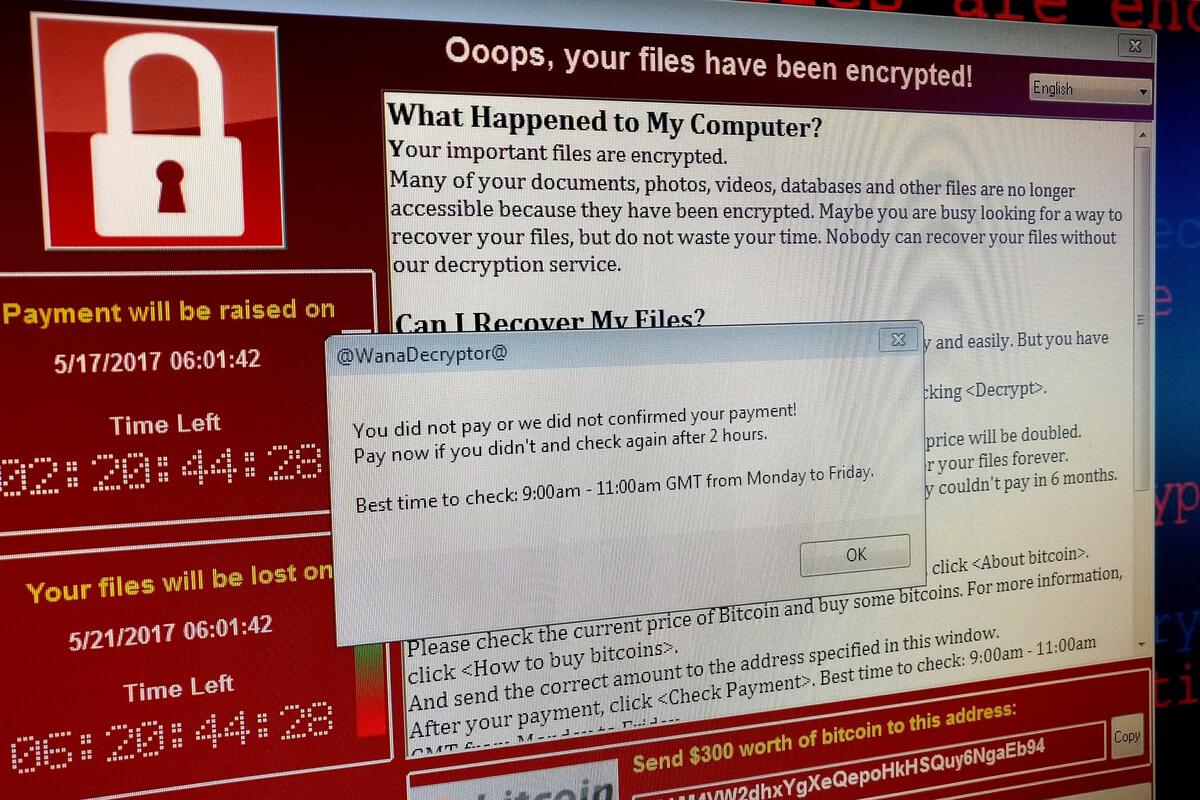
While it sounds similar to Business Email Compromise, Business Process Compromise is an entirely new beast. How are cybercriminals able to flip the board on the security measures consumers as well as businesses utilize to safeguard their most important data and content?
How are cybercriminals able to flip the board on the security measures consumers as well as businesses utilize to safeguard their most important data and content?