Industrial robots used in factories and warehouses that are connected to the internet are not secure, leaving companies open to cyberattacks and costly damages.
That’s the word coming from a study conducted by global security software company Trend Micro and Polytechnic University of Milan, the largest technical university in Italy.
“The industrial robot – it’s not ready for the world it’s living in,” said Mark Nunnikhoven, vice president of cloud research at Trend Micro. “The reality is these things are being connected in more and more places. There are a lot of attacks that could happen in that environment.”
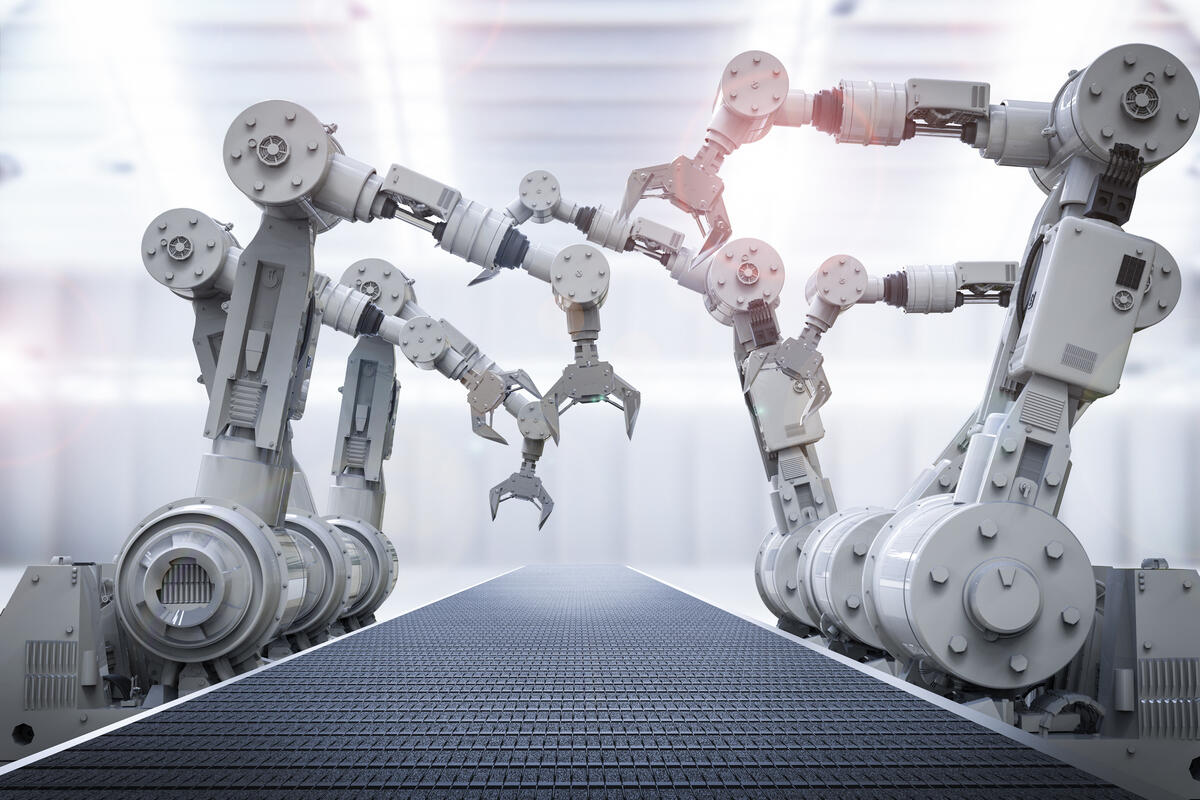
The study looked at Internet security vulnerabilities that could involve industrial robots used on manufacturing lines in areas such as the automobile and aerospace industries. The robots, which generally look like large mechanical arms, are used to move heavy objects, weld seams and fit pieces together. The machines also can be found moving and stacking crates in warehouses.
To read this article in full or to leave a comment, please click here


 In April 2017 my monthly threat webinar focused on a cyberespionage group our Forward-Looking Threat Researcher, Feike Hacquebord, has been following for many years and recently published a report into the most recent two years of activities. In this post I want to focus on their tools and tactics versus who they target since this…
In April 2017 my monthly threat webinar focused on a cyberespionage group our Forward-Looking Threat Researcher, Feike Hacquebord, has been following for many years and recently published a report into the most recent two years of activities. In this post I want to focus on their tools and tactics versus who they target since this…


 Throughout the history of cloud computing, 2006 was a momentous year. In 2006 Amazon Web Services released S3, the first pay per GB storage service. By August, they released EC2, allowing you to spin up a server and pay by the hour in the cloud. In the decade that has followed, AWS has emerged as…
Throughout the history of cloud computing, 2006 was a momentous year. In 2006 Amazon Web Services released S3, the first pay per GB storage service. By August, they released EC2, allowing you to spin up a server and pay by the hour in the cloud. In the decade that has followed, AWS has emerged as…