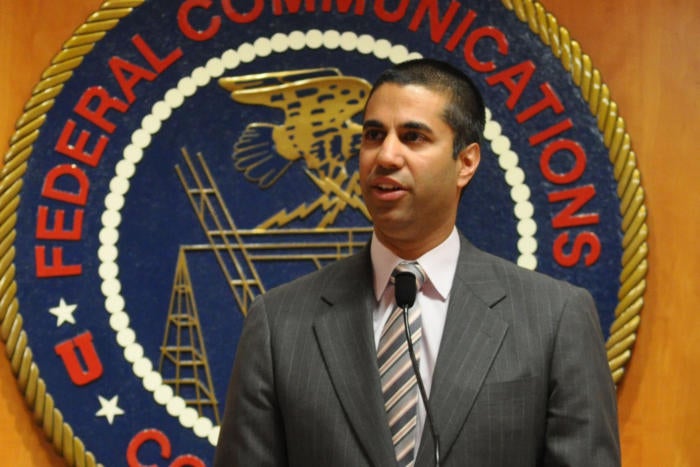
FCC puts the brakes on ISP privacy rules it passed in October
Credit to Author: Grant Gross| Date: Fri, 24 Feb 2017 10:43:00 -0800
The new chairman of the U.S. Federal Communications Commission will seek a stay on privacy rules for broadband providers that the agency just passed in October.
FCC Chairman Ajit Pai will ask for either a full commission vote on the stay before parts of the rules take effect next Thursday or he will instruct FCC staff to delay part of the rules pending a commission vote, a spokesman said Friday.
The rules, passed when the FCC had a Democratic majority, require broadband providers to receive opt-in customer permission to share sensitive personal information, including web-browsing history, geolocation, and financial details, with third parties. Without the stay, the opt-in requirements were scheduled to take effect next week.
To read this article in full or to leave a comment, please click here


 I’ve been fascinated with the rise and fall of exploit kits, especially the ones that are really popular that disappear seemingly overnight. Angler was one that at one point, contributed 59.5% in the total exploit kit activity for 2015. But now it’s presumed dead as of June 2016 after the arrest of a hacker gang….
I’ve been fascinated with the rise and fall of exploit kits, especially the ones that are really popular that disappear seemingly overnight. Angler was one that at one point, contributed 59.5% in the total exploit kit activity for 2015. But now it’s presumed dead as of June 2016 after the arrest of a hacker gang….

 Mobile gaming malware is a huge concern – and thus it’s important to take note of how these kinds of malicious programs can be guarded against.
Mobile gaming malware is a huge concern – and thus it’s important to take note of how these kinds of malicious programs can be guarded against.