Why cyber-robotics is key to cybersecurity's future

Chad Holmes, Principal of Ernst & Young LLP sits down with Network World's Neal Weinberg to talk about how cyber-robotics will help shape the future of cybersecurity.
RSS Reader for Computer Security Articles

Chad Holmes, Principal of Ernst & Young LLP sits down with Network World's Neal Weinberg to talk about how cyber-robotics will help shape the future of cybersecurity.
Credit to Author: Elisa Lippincott (TippingPoint Global Product Marketing)| Date: Fri, 17 Feb 2017 21:50:12 +0000
 Love was in the air earlier this week. This past Tuesday was Valentine’s Day and what should have been Microsoft’s “Patch Tuesday,” but it was reported last month that Patch Tuesday would never be the same as Microsoft moves to a process that includes an online searchable database and automatic updates. I was wondering what…
Love was in the air earlier this week. This past Tuesday was Valentine’s Day and what should have been Microsoft’s “Patch Tuesday,” but it was reported last month that Patch Tuesday would never be the same as Microsoft moves to a process that includes an online searchable database and automatic updates. I was wondering what…

Credit to Author: Michael Kan| Date: Fri, 17 Feb 2017 13:53:00 -0800
Almost 20 years ago, Chris Wysopal was among a group of hackers who testified before Congress, warning of the dangers of the internet.
Unfortunately, the U.S. government is still struggling to act, Wysopal said. “You’re just going to keep ending up with the status quo,” he said, pointing to the U.S. government’s failure to regulate the tech industry or provide incentives for change.
It’s a feeling that was shared by the experts who attended this week’s RSA cybersecurity show in San Francisco. The U.S. government needs to do more on cybersecurity, but what?
To read this article in full or to leave a comment, please click here

Credit to Author: Greg Lambert| Date: Fri, 17 Feb 2017 09:52:00 -0800
After a short break since our Patch Tuesday Debugged analysis in January, it looks like we are going to have some delay with Patch Tuesday in February due to a last minute technical issue with the Microsoft release process.
Microsoft had previously indicated that it was going to change the update process for security-related fixes this month — and a bug discovered during this process change may have caused the delay. Chris Goettl from Ivanti, offers this: “In the hours since Microsoft announced it was going to postpone Update Tuesday I have had a number of people asking if this delay was related to Microsoft’s change to a cumulative update model. If it were just one update that was delayed I would agree, but with all updates being delayed I think it is more of a Windows Update Services infrastructure issue.” I would tend to agree.
To read this article in full or to leave a comment, please click here

Credit to Author: Lucian Constantin| Date: Fri, 17 Feb 2017 09:08:00 -0800
Android applications that allow millions of car owners to remotely locate and unlock their vehicles are missing security features that could prevent tampering by hackers.
Researchers from antivirus vendor Kaspersky Lab took seven of the most popular Android apps that accompany connected cars from various manufacturers, and analyzed them from the perspective of a compromised Android device. The apps and manufacturers have not been named.
The researchers looked at whether such apps use any of the available countermeasures that would make it hard for attackers to hijack them when the devices they’re installed on are infected with malware. Other types of applications, such as banking apps, have such protections.
To read this article in full or to leave a comment, please click here
Credit to Author: Jaikumar Vijayan| Date: Fri, 17 Feb 2017 04:51:00 -0800
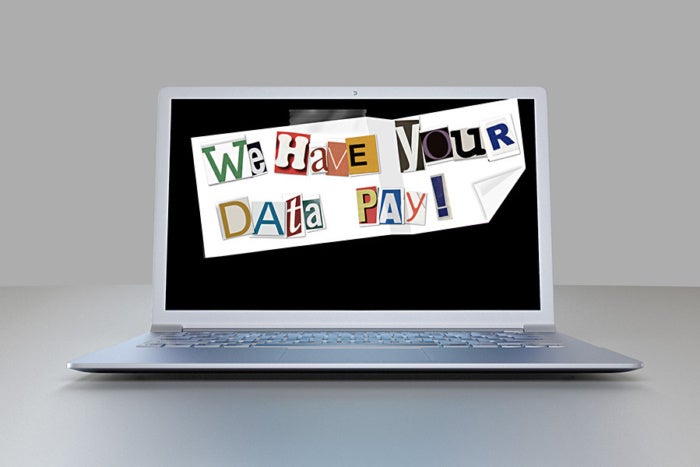
Paying ransom to a cyber extortionist holding enterprise data hostage might seem like a poor idea in principle but sometimes it might the best, or even only, option for extricating your organization from a crisis.
To read this article in full or to leave a comment, please click here
(Insider Story)
Read More
Credit to Author: Michael Kan| Date: Thu, 16 Feb 2017 16:34:00 -0800
Come to the RSA show, and you’ll find plenty of cybersecurity technology. The top vendors from across the industry are here, showing products for fighting ransomware, preventing data breaches and more.
But even the best security software is useless if users and businesses aren’t taking the right steps to protect themselves. So we asked experts at the show for their best cybersecurity tips.
Joe Stewart, director of malware research at Dell SecureWorks
He advises everyone to set up two-factor authentication to protect their internet accounts, especially email. It can be particularly useful when stopping hackers who are trying to steal login passwords from users, whether through malware or email phishing schemes.
To read this article in full or to leave a comment, please click here
Credit to Author: Andy Greenberg| Date: Thu, 16 Feb 2017 22:30:09 +0000

Kaspersky security researchers find missing security safeguards in nine different connected car apps. The post Android Phone Hacks Could Unlock Millions of Cars appeared first on WIRED.
Read More