Latest VBWeb report describes current state of the web-based threat landscape
The web continues to be a major infection vector for individuals and organisations alike. In the VBWeb tests, which form part of Virus Bulletin’s test suite, our team measures the performance of web security products against a range of live web threats. We publish quarterly reports on the performance of the products that have opted to be included in our public testing as well as providing an overview of the current state of the web‑based threat landscape.
The latest VBWeb report, released today, reveals that the Winter 2019/20 threat landscape continues to be more interesting than previous years when it comes to exploit kits, and we are still seeing new kits emerging. At least 11 kits are currently active and during the course of the Winter 2020 VBWeb test we caught eight of them in our lab: RIG, Fallout, Spelevo, Underminer, KaiXin, Purplefox, Capesand and Lewd.
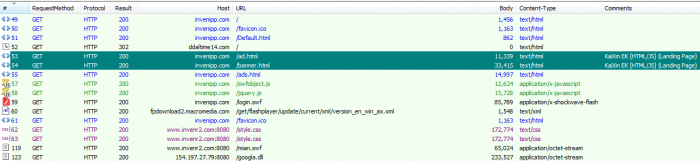 KaiXin exploit kit traffic spotted in our lab.
KaiXin exploit kit traffic spotted in our lab.
The most recent kits to emerge were Capesand, which was found by researchers from Trend Micro and delivers njRat, and Bottle, which was found by @nao_sec and delivers a stealer that targets users in Japan.
Other malware the team saw downloaded by the various exploit kits included: Danabot, Smokeloader, Trickbot, Raccoon, Dridex, Hidenbee and Qakbot.
We also spotted more than 800 instances of malware downloads from around 90 families including Emotet, Trickbot, Ursnif, Mirai and Ransomshade. Fortunately, the tested products had very few problems blocking malware in any of these categories – the full results can be read in the Winter 2020 VBWeb test report.
If you are interested in having your product tested either publicly or privately, or discussing the options with us, get in touch with our lab team at vbtest@virusbulletin.com.
outertext
https://www.virusbulletin.com/rss