A November rain of patches from Microsoft
Credit to Author: Angela Gunn| Date: Thu, 16 Nov 2023 18:08:02 +0000
Microsoft on Tuesday released patches for 57 vulnerabilities, including 31 for Windows. Eleven other product groups are also affected. Of the 57 CVEs addressed, just 3 are considered Critical in severity; 2 of those are in Windows, while the third falls in Azure. One CVE, an Important-severity elevation-of-privilege issue (CVE-2023-36049), affects both .NET and Visual Studio; another Important-severity EoP affects .NET, Visual Studio, and also ASP.NET.
At press time, three Windows issues are known to be under exploit in the wild. (Or, depending on how you count these things, there are four, as we’ll discuss in the Notable November Updates section below.) An additional 10 vulnerabilities in Windows, Exchange, Office, and SharePoint are by the company’s estimation more likely to be exploited in the next 30 days, with the Office vulnerability (CVE-2023-36413, a security feature bypass) publicly disclosed already.
In addition to the 57 CVEs, Microsoft lists one official advisory, ADV990001, which covers their latest servicing stack updates. However, the list of information-only advisories is extensive this month. In addition to 21 CVEs affecting Edge/Chromium (six of those Edge-specific), there is information on an industry-wide issue affecting BlueTooth; an HTTP/2-related issue, currently under active exploit in the wild, touching Windows, ASP.NET, .NET and Visual Studio; five CBL-Mariner-related issued covered by CVEs from Kubernetes, Red Hat, and MITRE; 17 Adobe-issued patches for Acrobat Reader, and seven more patches from Adobe for ColdFusion.
We don’t include these 53 issues in the CVE counts and graphics below, but we’ll provide information on everything in an appendix at the end of the article. We are as usual including at the end of this post three appendices listing all Microsoft’s patches, sorted by severity, by predicted exploitability, and by product family.
In addition to all of this, Windows Server 2022, 23H2 Edition (Server Core installation) is released as part of this update.
By the numbers
- Total Microsoft CVEs: 57
- Total Microsoft advisories shipping in update: 1
- Total other advisory issues covered in update: 52
- Publicly disclosed: 3
- Exploited: 3 plus one in non-Microsoft advisory issue
- Severity
- Critical: 3
- Important: 54
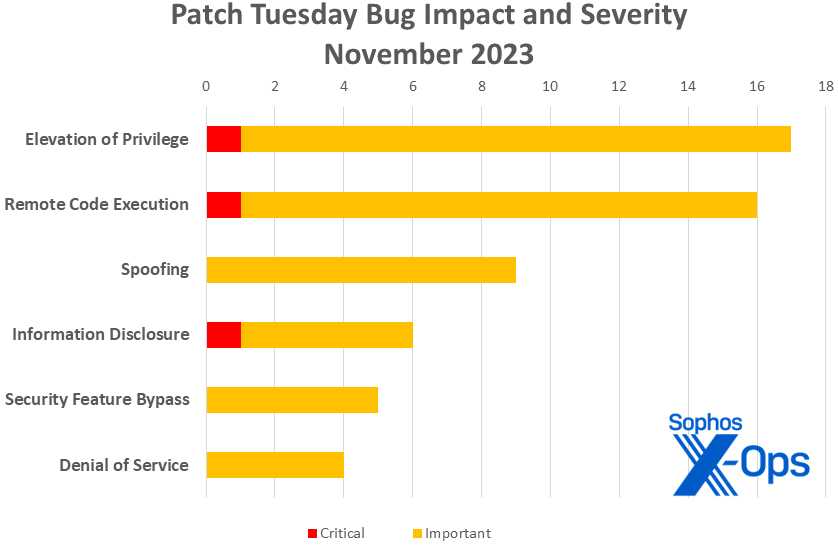
- Impact
- Elevation of Privilege: 17
- Remote Code Execution: 16
- Spoofing: 9
- Information Disclosure: 6
- Security Feature Bypass: 5
- Denial of Service: 4
Figure 1: This month elevation of privilege issues were slightly more prevalent than remote code execution for a change; spoofing also makes a strong showing
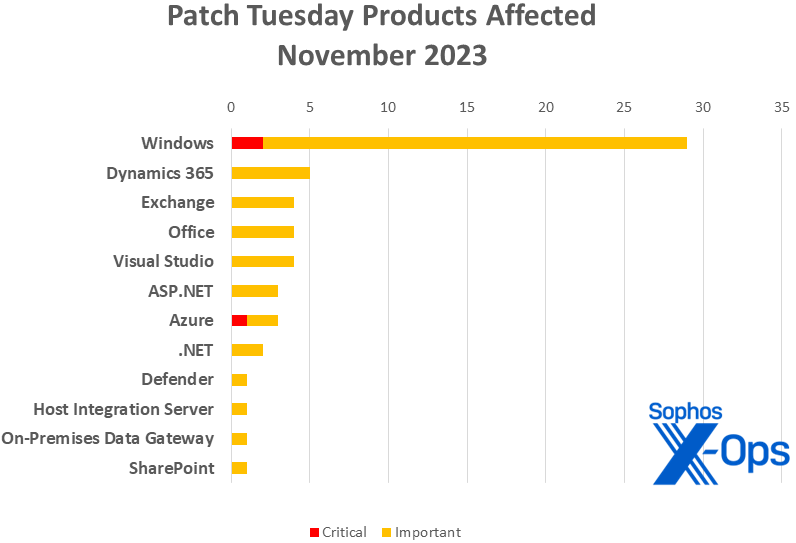
Products
- Windows: 31
- Dynamics 365: 5
- Exchange: 4
- Office: 4
- Visual Studio: 4, including one shared with .NET and one shared with ASP.NET and .NET
- ASP.NET: 3, including one shared with .NET and Visual Studio
- Azure: 3
- .NET: 2 (one shared with Visual Studio and one shared with ASP.NET and Visual Studio)
- Defender: 1
- Host Integration Server: 1
- On-Premises Data Gateway: 1
- SharePoint: 1
Figure 2: Windows as usual takes the lion’s share of patches in November, but there’s a fairly wide variety of more specialized products affected. (In the case of patches touching more than one product, each instance is represented in this chart; for instance, CVE-2023-36049, which affects both Visual Studio and .NET, is counted once for each of the two)
Notable November updates
In addition to the issues discussed above, a few interesting items present themselves.
CVE-2023-36025 — Windows SmartScreen Security Feature Bypass Vulnerability
There are three Windows CVEs this month for which active exploitation has been detected in the wild. (Or four; more on that in a minute.) This one, an Important-class security feature bypass, has the highest CVSS base and temporal scores (Base 8.8 / Temporal 8.2) of the trio. All it takes is a malicious URL, and the attacker is able to bypass Windows Defender SmartScreen checks and the prompts the user would expect to see with those.
CVE-2023-36397 — Windows Pragmatic General Multicast (PGM) Remote Code Execution Vulnerability
Is message queuing enabled on your system? This vulnerability, which can be triggered by an attacker sending a maliciously crafted file over the network, is critical-severity (CVSS 3.1 9.8/8.5) and can lead to RCE. In addition to the other protections released for this, Microsoft notes that users can check their exposure by checking to see if the service called Message Queuing is running, and if TCP port 1801 is in listening mode.
CVE-2020-8554, CVE-2023-46753, CVE-2023-46316, CVE-2020-14343, CVE-2020-1747 (5 CVEs)
These five CVEs are not part of Microsoft’s official release, but no one using Microsoft’s CBL-Mariner (Common Base Linux Mariner) should sleep on them. CBL-Mariner is Microsoft’s own Linux distro; first developed in-house for internal development and Azure management. The distro was quietly made publicly available to the public last year. None of the three CVEs are directly from Microsoft, but from Kubernetes (CVE-2020-8554), Red Hat (CVE-2020-14343, CVE-2020-1747), and MITRE (CVE-2023-46316, CVE-2023-46753). Due to the apparent age of several of these CVEs and their severity – three of the five have a CVSS base score of 9.8 out of 10 – users are encouraged to keep themselves up to date.
CVE-2023-24023 — MITRE: CVE-2023-24023 Bluetooth Spoofing Vulnerability
CVE-2023-44487 — MITRE: CVE-2023-44487 HTTP/2 Rapid Reset Attack
Speaking of MITRE, the organization features in two more CVEs about which Microsoft is publishing information. As one would expect, the MITRE CVEs are applicable for many companies, not only Microsoft. CVE-2023-24023 covers an important-severity spoofing vulnerability reported to BlueTooth’s governing body. As for CVE-2023-44487, this CVE makes an unusual repeat appearance on the Patch Tuesday roster; readers may remember that we discussed this Rapid Reset issue in last month’s roundup. It affects Windows, ASP.NET, .NET, and Visual Studio.
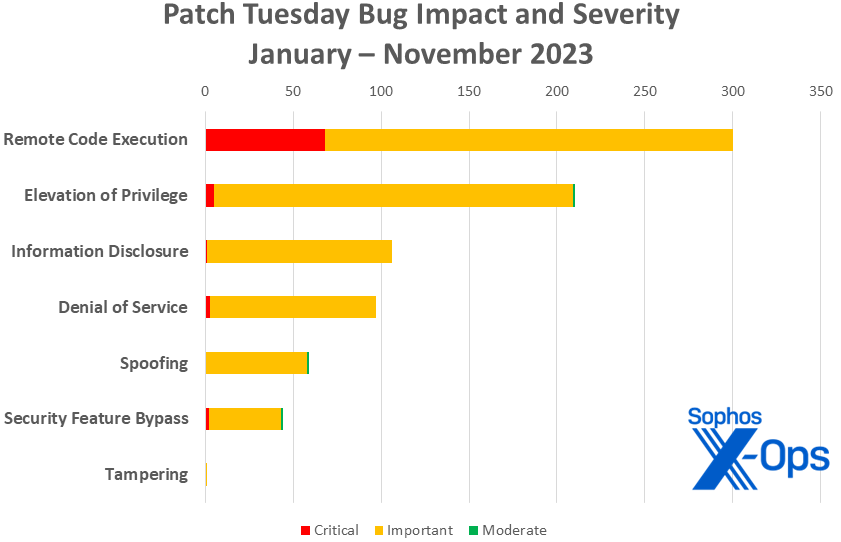
Figure 3: With one month to go in 2023, the tally of remote code execution patches releases reaches 300. Meanwhile, it’s barely visible, but the year’s first critical-level information-disclosure issue shows on the chart
Sophos protections
As you can every month, if you don’t want to wait for your system to pull down Microsoft’s updates itself, you can download them manually from the Windows Update Catalog website. Run the winver.exe tool to determine which build of Windows 10 or 11 you’re running, then download the Cumulative Update package for your specific system’s architecture and build number.
Appendix A: Vulnerability Impact and Severity
This is a list of November’s patches sorted by impact, then sub-sorted by severity. Each list is further arranged by CVE.
Elevation of Privilege (17 CVEs)
| Critical severity | |
| CVE-2023-36400 | Windows HMAC Key Derivation Elevation of Privilege Vulnerability |
| Important severity | |
| CVE-2023-36033 | Windows DWM Core Library Elevation of Privilege Vulnerability |
| CVE-2023-36036 | Windows Cloud Files Mini Filter Driver Elevation of Privilege Vulnerability |
| CVE-2023-36047 | Windows Authentication Elevation of Privilege Vulnerability |
| CVE-2023-36049 | .NET, .NET Framework, and Visual Studio Elevation of Privilege Vulnerability |
| CVE-2023-36394 | Windows Search Service Elevation of Privilege Vulnerability |
| CVE-2023-36399 | Windows Storage Elevation of Privilege Vulnerability |
| CVE-2023-36403 | Windows Kernel Elevation of Privilege Vulnerability |
| CVE-2023-36405 | Windows Kernel Elevation of Privilege Vulnerability |
| CVE-2023-36407 | Windows Hyper-V Elevation of Privilege Vulnerability |
| CVE-2023-36408 | Windows Hyper-V Elevation of Privilege Vulnerability |
| CVE-2023-36422 | Microsoft Windows Defender Elevation of Privilege Vulnerability |
| CVE-2023-36424 | Windows Common Log File System Driver Elevation of Privilege Vulnerability |
| CVE-2023-36427 | Windows Hyper-V Elevation of Privilege Vulnerability |
| CVE-2023-36558 | ASP.NET Core – Security Feature Bypass Vulnerability |
| CVE-2023-36705 | Windows Installer Elevation of Privilege Vulnerability |
| CVE-2023-36719 | Microsoft Speech Application Programming Interface (SAPI) Elevation of Privilege Vulnerability |
Remote Code Execution (16 CVEs)
| Critical severity | |
| CVE-2023-36397 | Windows Pragmatic General Multicast (PGM) Remote Code Execution Vulnerability |
| Important severity | |
| CVE-2023-36017 | Windows Scripting Engine Memory Corruption Vulnerability |
| CVE-2023-36028 | Microsoft Protected Extensible Authentication Protocol (PEAP) Remote Code Execution Vulnerability |
| CVE-2023-36041 | Microsoft Excel Remote Code Execution Vulnerability |
| CVE-2023-36042 | Visual Studio Denial of Service Vulnerability |
| CVE-2023-36045 | Microsoft Office Graphics Remote Code Execution Vulnerability |
| CVE-2023-36393 | Windows User Interface Application Core Remote Code Execution Vulnerability |
| CVE-2023-36396 | Windows Compressed Folder Remote Code Execution Vulnerability |
| CVE-2023-36401 | Microsoft Remote Registry Service Remote Code Execution Vulnerability |
| CVE-2023-36402 | Microsoft WDAC OLE DB provider for SQL Server Remote Code Execution Vulnerability |
| CVE-2023-36423 | Microsoft Remote Registry Service Remote Code Execution Vulnerability |
| CVE-2023-36425 | Windows Distributed File System (DFS) Remote Code Execution Vulnerability |
| CVE-2023-36437 | Azure DevOps Server Remote Code Execution Vulnerability |
| CVE-2023-36439 | Microsoft Exchange Server Remote Code Execution Vulnerability |
| CVE-2023-38151 | Microsoft Host Integration Server 2020 Remote Code Execution Vulnerability |
| CVE-2023-38177 | Microsoft SharePoint Server Remote Code Execution Vulnerability |
Spoofing (9 CVEs)
| Important severity | |
| CVE-2023-36007 | Microsoft Send Customer Voice survey from Dynamics 365 Spoofing Vulnerability |
| CVE-2023-36016 | Microsoft Dynamics 365 (on-premises) Cross-site Scripting Vulnerability |
| CVE-2023-36018 | Visual Studio Code Jupyter Extension Spoofing Vulnerability |
| CVE-2023-36030 | Microsoft Dynamics 365 Sales Spoofing Vulnerability |
| CVE-2023-36031 | Microsoft Dynamics 365 (on-premises) Cross-site Scripting Vulnerability |
| CVE-2023-36035 | Microsoft Exchange Server Spoofing Vulnerability |
| CVE-2023-36039 | Microsoft Exchange Server Spoofing Vulnerability |
| CVE-2023-36050 | Microsoft Exchange Server Spoofing Vulnerability |
| CVE-2023-36410 | Microsoft Dynamics 365 (on-premises) Cross-site Scripting Vulnerability |
Information Disclosure (6 CVEs)
| Critical severity | |
| CVE-2023-36052 | Azure CLI REST Command Information Disclosure Vulnerability |
| Important severity | |
| CVE-2023-36043 | Open Management Infrastructure Information Disclosure Vulnerability |
| CVE-2023-36398 | Windows NTFS Information Disclosure Vulnerability |
| CVE-2023-36404 | Windows Kernel Information Disclosure Vulnerability |
| CVE-2023-36406 | Windows Hyper-V Information Disclosure Vulnerability |
| CVE-2023-36428 | Microsoft Local Security Authority Subsystem Service Information Disclosure Vulnerability |
Security Feature Bypass (5 CVEs)
| Important severity | |
| CVE-2023-36021 | Microsoft Host Integration Server 2020 Security Feature Bypass Vulnerability |
| CVE-2023-36025 | Windows SmartScreen Security Feature Bypass Vulnerability |
| CVE-2023-36037 | Microsoft Excel Security Feature Bypass Vulnerability |
| CVE-2023-36413 | Microsoft Office Security Feature Bypass Vulnerability |
| CVE-2023-36560 | ASP.NET Security Feature Bypass Vulnerability |
Denial of Service (4 CVE)
| Important severity | |
| CVE-2023-36038 | ASP.NET Core Denial of Service Vulnerability |
| CVE-2023-36046 | Windows Authentication Denial of Service Vulnerability |
| CVE-2023-36392 | DHCP Server Service Denial of Service Vulnerability |
| CVE-2023-36395 | Windows Deployment Services Denial of Service Vulnerability |
Appendix B: Exploitability
This is a list of the November CVEs judged by Microsoft to be more likely to be exploited in the wild within the first 30 days post-release, as well as those already known to be under exploit. Each list is further arranged by CVE.
| Exploitation detected | |
| CVE-2023-36025 | Windows SmartScreen Security Feature Bypass Vulnerability |
| CVE-2023-36033 | Windows DWM Core Library Elevation of Privilege Vulnerability |
| CVE-2023-36036 | Windows Cloud Files Mini Filter Driver Elevation of Privilege Vulnerability |
| Exploitation more likely within 30 days | |
| CVE-2023-36017 | Windows Scripting Engine Memory Corruption Vulnerability |
| CVE-2023-36035 | Microsoft Exchange Server Spoofing Vulnerability |
| CVE-2023-36039 | Microsoft Exchange Server Spoofing Vulnerability |
| CVE-2023-36050 | Microsoft Exchange Server Spoofing Vulnerability |
| CVE-2023-36394 | Windows Search Service Elevation of Privilege Vulnerability |
| CVE-2023-36399 | Windows Storage Elevation of Privilege Vulnerability |
| CVE-2023-36413 | Microsoft Office Security Feature Bypass Vulnerability |
| CVE-2023-36424 | Windows Common Log File System Driver Elevation of Privilege Vulnerability |
| CVE-2023-36439 | Microsoft Exchange Server Remote Code Execution Vulnerability |
| CVE-2023-38177 | Microsoft SharePoint Server Remote Code Execution Vulnerability |
Appendix C: Products Affected
This is a list of November’s patches sorted by product family, then sub-sorted by severity. Each list is further arranged by CVE. Patches that are shared among multiple product families are listed multiple times, once for each product family.
Windows (29 CVEs)
| Critical severity | |
| CVE-2023-36397 | Windows Pragmatic General Multicast (PGM) Remote Code Execution Vulnerability |
| CVE-2023-36400 | Windows HMAC Key Derivation Elevation of Privilege Vulnerability |
| Important severity | |
| CVE-2023-36017 | Windows Scripting Engine Memory Corruption Vulnerability |
| CVE-2023-36025 | Windows SmartScreen Security Feature Bypass Vulnerability |
| CVE-2023-36028 | Microsoft Protected Extensible Authentication Protocol (PEAP) Remote Code Execution Vulnerability |
| CVE-2023-36033 | Windows DWM Core Library Elevation of Privilege Vulnerability |
| CVE-2023-36036 | Windows Cloud Files Mini Filter Driver Elevation of Privilege Vulnerability |
| CVE-2023-36046 | Windows Authentication Denial of Service Vulnerability |
| CVE-2023-36047 | Windows Authentication Elevation of Privilege Vulnerability |
| CVE-2023-36392 | DHCP Server Service Denial of Service Vulnerability |
| CVE-2023-36393 | Windows User Interface Application Core Remote Code Execution Vulnerability |
| CVE-2023-36394 | Windows Search Service Elevation of Privilege Vulnerability |
| CVE-2023-36395 | Windows Deployment Services Denial of Service Vulnerability |
| CVE-2023-36396 | Windows Compressed Folder Remote Code Execution Vulnerability |
| CVE-2023-36398 | Windows NTFS Information Disclosure Vulnerability |
| CVE-2023-36399 | Windows Storage Elevation of Privilege Vulnerability |
| CVE-2023-36401 | Microsoft Remote Registry Service Remote Code Execution Vulnerability |
| CVE-2023-36402 | Microsoft WDAC OLE DB provider for SQL Server Remote Code Execution Vulnerability |
| CVE-2023-36403 | Windows Kernel Elevation of Privilege Vulnerability |
| CVE-2023-36404 | Windows Kernel Information Disclosure Vulnerability |
| CVE-2023-36405 | Windows Kernel Elevation of Privilege Vulnerability |
| CVE-2023-36406 | Windows Hyper-V Information Disclosure Vulnerability |
| CVE-2023-36407 | Windows Hyper-V Elevation of Privilege Vulnerability |
| CVE-2023-36408 | Windows Hyper-V Elevation of Privilege Vulnerability |
| CVE-2023-36423 | Microsoft Remote Registry Service Remote Code Execution Vulnerability |
| CVE-2023-36424 | Windows Common Log File System Driver Elevation of Privilege Vulnerability |
| CVE-2023-36425 | Windows Distributed File System (DFS) Remote Code Execution Vulnerability |
| CVE-2023-36427 | Windows Hyper-V Elevation of Privilege Vulnerability |
| CVE-2023-36428 | Microsoft Local Security Authority Subsystem Service Information Disclosure Vulnerability |
Dynamics 365 (5 CVEs)
| Important severity | |
| CVE-2023-36007 | Microsoft Send Customer Voice survey from Dynamics 365 Spoofing Vulnerability |
| CVE-2023-36016 | Microsoft Dynamics 365 (on-premises) Cross-site Scripting Vulnerability |
| CVE-2023-36030 | Microsoft Dynamics 365 Sales Spoofing Vulnerability |
| CVE-2023-36031 | Microsoft Dynamics 365 (on-premises) Cross-site Scripting Vulnerability |
| CVE-2023-36410 | Microsoft Dynamics 365 (on-premises) Cross-site Scripting Vulnerability |
Exchange (4 CVEs)
| Important severity | |
| CVE-2023-36035 | Microsoft Exchange Server Spoofing Vulnerability |
| CVE-2023-36039 | Microsoft Exchange Server Spoofing Vulnerability |
| CVE-2023-36050 | Microsoft Exchange Server Spoofing Vulnerability |
| CVE-2023-36439 | Microsoft Exchange Server Remote Code Execution Vulnerability |
Office (4 CVEs)
| Important severity | |
| CVE-2023-36037 | Microsoft Excel Security Feature Bypass Vulnerability |
| CVE-2023-36041 | Microsoft Excel Remote Code Execution Vulnerability |
| CVE-2023-36045 | Microsoft Office Graphics Remote Code Execution Vulnerability |
| CVE-2023-36413 | Microsoft Office Security Feature Bypass Vulnerability |
Visual Studio (4 CVEs)
| Important severity | |
| CVE-2023-36018 | Visual Studio Code Jupyter Extension Spoofing Vulnerability |
| CVE-2023-36042 | Visual Studio Denial of Service Vulnerability |
| CVE-2023-36049 | .NET, .NET Framework, and Visual Studio Elevation of Privilege Vulnerability |
| CVE-2023-36558 | ASP.NET Core – Security Feature Bypass Vulnerability |
ASP.NET (3 CVEs)
| Important severity | |
| CVE-2023-36038 | ASP.NET Core Denial of Service Vulnerability |
| CVE-2023-36560 | ASP.NET Security Feature Bypass Vulnerability |
| CVE-2023-36558 | ASP.NET Core – Security Feature Bypass Vulnerability |
Azure (3 CVEs)
| Critical severity | |
| CVE-2023-36052 | Azure CLI REST Command Information Disclosure Vulnerability |
| Important severity | |
| CVE-2023-36043 | Open Management Infrastructure Information Disclosure Vulnerability |
| CVE-2023-36437 | Azure DevOps Server Remote Code Execution Vulnerability |
.NET (2 CVEs)
| Important severity | |
| CVE-2023-36049 | .NET, .NET Framework, and Visual Studio Elevation of Privilege Vulnerability |
| CVE-2023-36558 | ASP.NET Core – Security Feature Bypass Vulnerability |
Defender (1 CVE)
| Critical severity | |
| CVE-2023-36422 | Microsoft Windows Defender Elevation of Privilege Vulnerability |
Host Integration Server (1 CVE)
| Important severity | |
| CVE-2023-38151 | Microsoft Host Integration Server 2020 Remote Code Execution Vulnerability |
On-Premises Data Gateway (1 CVE)
| Important severity | |
| CVE-2023-36021 | Microsoft Host Integration Server 2020 Security Feature Bypass Vulnerability |
SharePoint (1 CVE)
| Important severity | |
| CVE-2023-38177 | Microsoft SharePoint Server Remote Code Execution Vulnerability |
Appendix D: Other Products
This is a list of advisories and information on other relevant CVEs in the November Microsoft release, sorted by product.
Microsoft Servicing Stack Updates
| ADV990001 | Latest Servicing Stack Updates |
Adobe Acrobat Reader Bulletin APSB23-54: Security updates available for Acrobat Reader (17 CVEs)
| CVE-2023-44336 | Use After Free (CWE-416) |
| CVE-2023-44337 | Out-of-bounds Read (CWE-125) |
| CVE-2023-44338 | Out-of-bounds Read (CWE-125) |
| CVE-2023-44339 | Out-of-bounds Read (CWE-125) |
| CVE-2023-44340 | Out-of-bounds Read (CWE-125) |
| CVE-2023-44348 | Out-of-bounds Read (CWE-125) |
| CVE-2023-44356 | Out-of-bounds Read (CWE-125) |
| CVE-2023-44357 | Out-of-bounds Read (CWE-125) |
| CVE-2023-44358 | Out-of-bounds Read (CWE-125) |
| CVE-2023-44359 | Use After Free (CWE-416) |
| CVE-2023-44360 | Out-of-bounds Read (CWE-125) |
| CVE-2023-44361 | Use After Free (CWE-416) |
| CVE-2023-44365 | Access of Uninitialized Pointer (CWE-824) |
| CVE-2023-44366 | Out-of-bounds Write (CWE-787) |
| CVE-2023-44367 | Use After Free (CWE-416) |
| CVE-2023-44371 | Use After Free (CWE-416) |
| CVE-2023-44372 | Use After Free (CWE-416) |
Adobe ColdFusion Bulletin APSB23-52: Security updates available for Adobe ColdFusion (7 CVEs)
| CVE-2023-44347 | Improper Access Control (CWE-284) |
| CVE-2023-44350 | Deserialization of Untrusted Data (CWE-502) |
| CVE-2023-44351 | Deserialization of Untrusted Data (CWE-502) |
| CVE-2023-44352 | Cross-site Scripting (Reflected XSS) (CWE-79) |
| CVE-2023-44353 | Deserialization of Untrusted Data (CWE-502) |
| CVE-2023-44354 | Improper Authentication (CWE-287) |
| CVE-2023-44355 | Improper Input Validation (CWE-20) |
Relevant MITRE releases (2 CVEs)
| CVE-2023-24023 | MITRE: CVE-2023-24023 Bluetooth Spoofing Vulnerability |
| CVE-2023-44487 | MITRE: CVE-2023-44487 HTTP/2 Rapid Reset Attack |
Relevant to CBL-Mariner (5 CVEs)
| CVE-2020-8554 | Kubernetes man in the middle using LoadBalancer or ExternalIPs |
| CVE-2023-46753 | [FRRouting issue; no title provided] |
| CVE-2023-46316 | [traceroute issue; no title provided] |
| CVE-2020-14343 | [PyYAML library issue; no title provided] |
| CVE-2020-1747 | [PyYAML library issue; no title provided] |
Relevant to Edge / Chromium (21 CVEs)
| CVE-2023-36014 | Microsoft Edge (Chromium-based) Remote Code Execution Vulnerability |
| CVE-2023-36022 | Microsoft Edge (Chromium-based) Remote Code Execution Vulnerability |
| CVE-2023-36024 | Microsoft Edge (Chromium-based) Elevation of Privilege Vulnerability |
| CVE-2023-36027 | Microsoft Edge (Chromium-based) Elevation of Privilege Vulnerability |
| CVE-2023-36029 | Microsoft Edge (Chromium-based) Spoofing Vulnerability |
| CVE-2023-36034 | Microsoft Edge (Chromium-based) Remote Code Execution Vulnerability |
| CVE-2023-5346 | Chromium: CVE-2023-5346 Type Confusion in V8 |
| CVE-2023-5480 | Chromium: CVE-2023-5480 Inappropriate implementation in Payments |
| CVE-2023-5482 | Chromium: CVE-2023-5482 Insufficient data validation in USB |
| CVE-2023-5849 | Chromium: CVE-2023-5849 Integer overflow in USB |
| CVE-2023-5850 | Chromium: CVE-2023-5850 Incorrect security UI in Downloads |
| CVE-2023-5851 | Chromium: CVE-2023-5851 Inappropriate implementation in Downloads |
| CVE-2023-5852 | Chromium: CVE-2023-5852 Use after free in Printing |
| CVE-2023-5853 | Chromium: CVE-2023-5853 Incorrect security UI in Downloads |
| CVE-2023-5854 | Chromium: CVE-2023-5854 Use after free in Profiles |
| CVE-2023-5855 | Chromium: CVE-2023-5855 Use after free in Reading Mode |
| CVE-2023-5856 | Chromium: CVE-2023-5856 Use after free in Side Panel |
| CVE-2023-5857 | Chromium: CVE-2023-5857 Inappropriate implementation in Downloads |
| CVE-2023-5858 | Chromium: CVE-2023-5858 Inappropriate implementation in WebApp Provider |
| CVE-2023-5859 | Chromium: CVE-2023-5859 Incorrect security UI in Picture In Picture |
| CVE-2023-5996 | Chromium: CVE-2023-5996 Use after free in WebAudio |