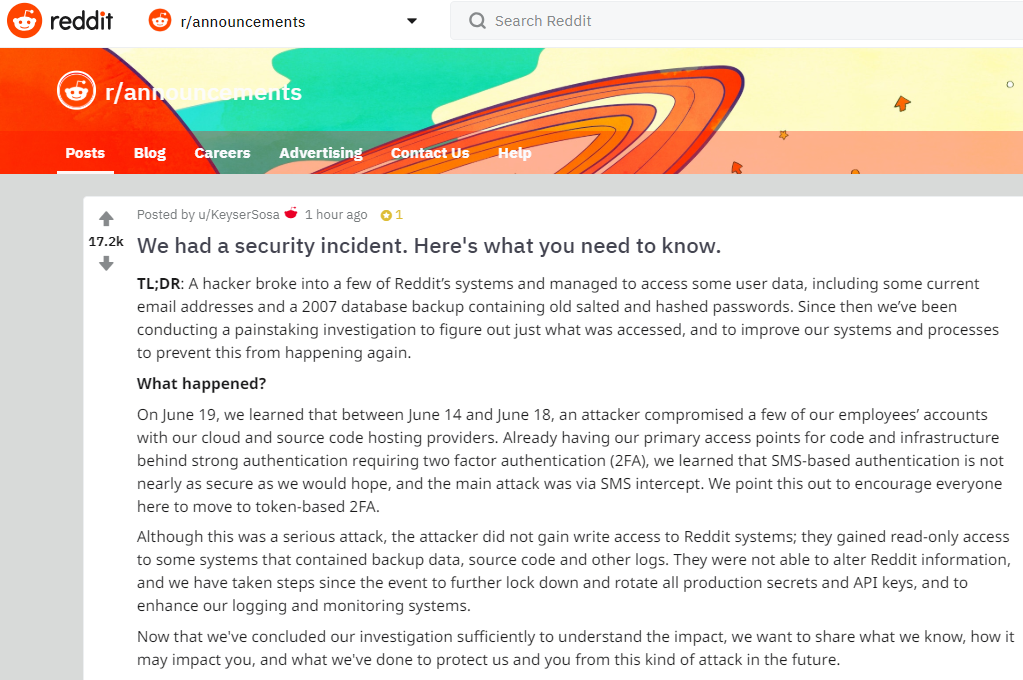
Credit Card Issuer TCM Bank Leaked Applicant Data for 16 Months

Credit to Author: BrianKrebs| Date: Fri, 03 Aug 2018 15:48:53 +0000
TCM Bank, a company that helps more than 750 small and community U.S. banks issue credit cards to their account holders, said a Web site misconfiguration exposed the names, addresses, dates of birth and Social Security numbers of thousands of people who applied for cards between early March 2017 and mid-July 2018. TCM is a subsidiary of Washington, D.C.-based ICBA Bancard Inc., which helps community banks provide a credit card option to their customers using bank-branded cards.
Read More