Hacker takes out dark web hosting service using well-known exploit

A hacker is proving that sites on the dark web, shrouded in anonymity, can easily be compromised.
On Friday, the unnamed hacker began dumping a sizable database stolen from Freedom Hosting II onto the internet, potentially exposing its users.
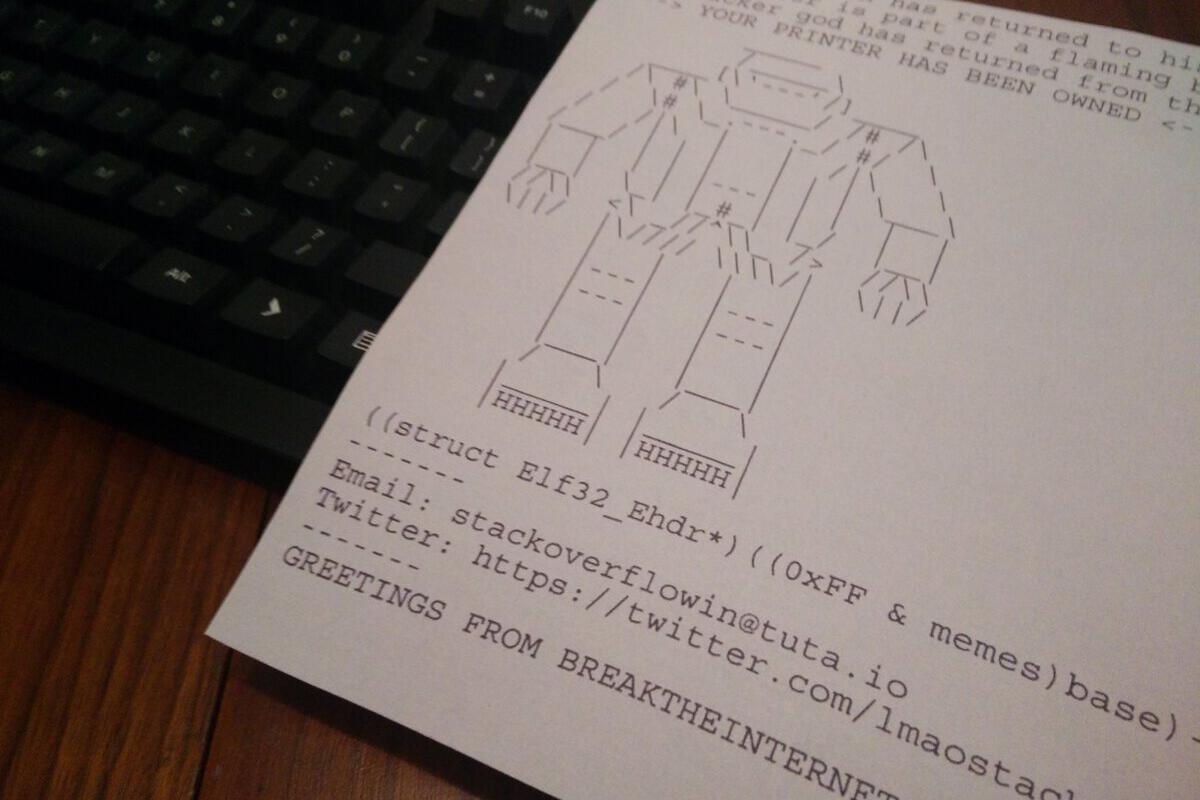
The hosting service, Freedom Hosting II, was known for operating thousands of sites that were accessible through the Tor browser; the “dark web” is essentially the encrypted network comprising Tor servers and browsers. But on Friday, the service appeared to be down. Its main landing page was replaced with a message saying that it had been hacked.
Allegedly, Freedom Hosting II had been hosting child pornography sites, though its anonymous operator claimed to have a zero-tolerance policy toward such content, according to the hacker behind the breach.
To read this article in full or to leave a comment, please click here